Master of Science thesis Fighting Spam
Master of Science thesis Fighting Spam
Master of Science thesis Fighting Spam
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
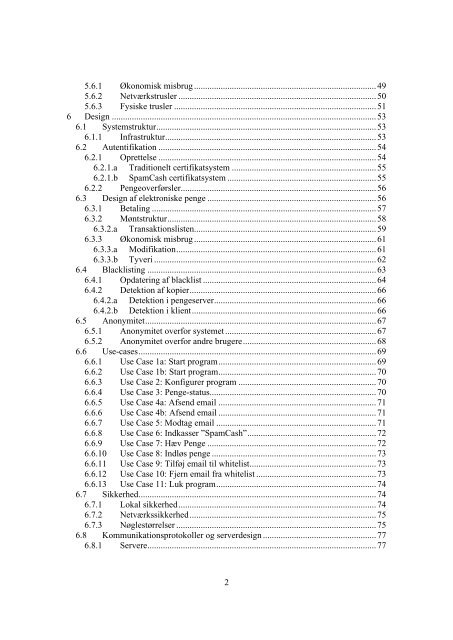
5.6.1 Økonomisk misbrug ..................................................................................49<br />
5.6.2 Netværkstrusler .........................................................................................50<br />
5.6.3 Fysiske trusler ...........................................................................................51<br />
6 Design .......................................................................................................................53<br />
6.1 Systemstruktur...................................................................................................53<br />
6.1.1 Infrastruktur...............................................................................................53<br />
6.2 Autentifikation ..................................................................................................54<br />
6.2.1 Oprettelse ..................................................................................................54<br />
6.2.1.a Traditionelt certifikatsystem ................................................................. 55<br />
6.2.1.b <strong>Spam</strong>Cash certifikatsystem ...................................................................55<br />
6.2.2 Pengeoverførsler........................................................................................56<br />
6.3 Design af elektroniske penge ............................................................................56<br />
6.3.1 Betaling .....................................................................................................57<br />
6.3.2 Møntstruktur..............................................................................................58<br />
6.3.2.a Transaktionslisten..................................................................................59<br />
6.3.3 Økonomisk misbrug ..................................................................................61<br />
6.3.3.a Modifikation..........................................................................................61<br />
6.3.3.b Tyveri ....................................................................................................62<br />
6.4 Blacklisting .......................................................................................................63<br />
6.4.1 Opdatering af blacklist ..............................................................................64<br />
6.4.2 Detektion af kopier....................................................................................66<br />
6.4.2.a Detektion i pengeserver.........................................................................66<br />
6.4.2.b Detektion i klient...................................................................................66<br />
6.5 Anonymitet........................................................................................................67<br />
6.5.1 Anonymitet overfor systemet....................................................................67<br />
6.5.2 Anonymitet overfor andre brugere............................................................68<br />
6.6 Use-cases...........................................................................................................69<br />
6.6.1 Use Case 1a: Start program.......................................................................69<br />
6.6.2 Use Case 1b: Start program.......................................................................70<br />
6.6.3 Use Case 2: Konfigurer program ..............................................................70<br />
6.6.4 Use Case 3: Penge-status...........................................................................70<br />
6.6.5 Use Case 4a: Afsend email .......................................................................71<br />
6.6.6 Use Case 4b: Afsend email .......................................................................71<br />
6.6.7 Use Case 5: Modtag email ........................................................................71<br />
6.6.8 Use Case 6: Indkasser <strong>Spam</strong>Cash ..........................................................72<br />
6.6.9 Use Case 7: Hæv Penge ............................................................................72<br />
6.6.10 Use Case 8: Indløs penge ..........................................................................73<br />
6.6.11 Use Case 9: Tilføj email til whitelist.........................................................73<br />
6.6.12 Use Case 10: Fjern email fra whitelist ......................................................73<br />
6.6.13 Use Case 11: Luk program........................................................................74<br />
6.7 Sikkerhed...........................................................................................................74<br />
6.7.1 Lokal sikkerhed.........................................................................................74<br />
6.7.2 Netværkssikkerhed....................................................................................75<br />
6.7.3 Nøglestørrelser ..........................................................................................75<br />
6.8 Kommunikationsprotokoller og serverdesign ...................................................77<br />
6.8.1 Servere.......................................................................................................77<br />
2