Cyber Attack Task Force - Final Report - NERC
Cyber Attack Task Force - Final Report - NERC
Cyber Attack Task Force - Final Report - NERC
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Recommendations<br />
Following are the recommendations from the task force:<br />
Recommendations<br />
• Continue to build on the <strong>Attack</strong> Trees - A significant amount of work has gone into creating<br />
the attack tree framework, however recommendations from detailed analysis have not<br />
been completed. The top level root node of the attack tree is very specific to the task force<br />
scope, but lower level branches are applicable to many other scenarios such as attacks on<br />
generation, transmission/distribution or disrupting situational awareness.<br />
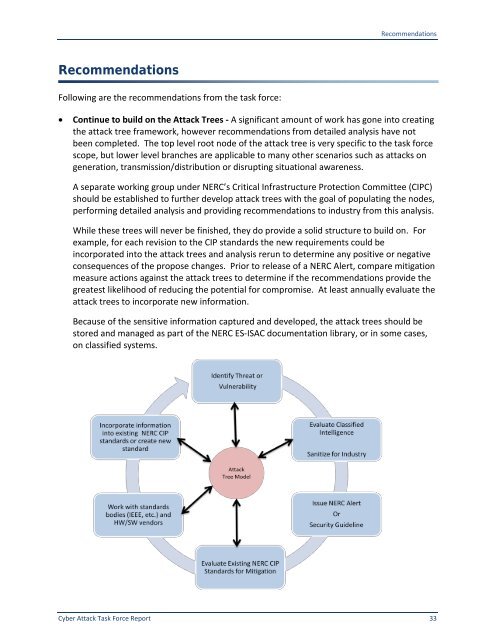
A separate working group under <strong>NERC</strong>’s Critical Infrastructure Protection Committee (CIPC)<br />
should be established to further develop attack trees with the goal of populating the nodes,<br />
performing detailed analysis and providing recommendations to industry from this analysis.<br />
While these trees will never be finished, they do provide a solid structure to build on. For<br />
example, for each revision to the CIP standards the new requirements could be<br />
incorporated into the attack trees and analysis rerun to determine any positive or negative<br />
consequences of the propose changes. Prior to release of a <strong>NERC</strong> Alert, compare mitigation<br />
measure actions against the attack trees to determine if the recommendations provide the<br />
greatest likelihood of reducing the potential for compromise. At least annually evaluate the<br />
attack trees to incorporate new information.<br />
Because of the sensitive information captured and developed, the attack trees should be<br />
stored and managed as part of the <strong>NERC</strong> ES-ISAC documentation library, or in some cases,<br />
on classified systems.<br />
<strong>Cyber</strong> <strong>Attack</strong> <strong>Task</strong> <strong>Force</strong> <strong>Report</strong> 33