Noncompliant Equipment - GIAC
Noncompliant Equipment - GIAC
Noncompliant Equipment - GIAC
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
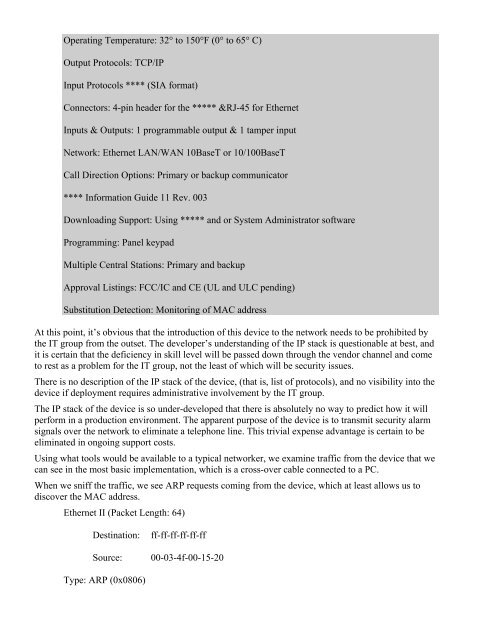
Operating Temperature: 32° to 150°F (0° to 65° C)<br />
Output Protocols: TCP/IP<br />
Input Protocols **** (SIA format)<br />
Connectors: 4-pin header for the ***** &RJ-45 for Ethernet<br />
Inputs & Outputs: 1 programmable output & 1 tamper input<br />
Network: Ethernet LAN/WAN 10BaseT or 10/100BaseT<br />
Call Direction Options: Primary or backup communicator<br />
**** Information Guide 11 Rev. 003<br />
Downloading Support: Using ***** and or System Administrator software<br />
Programming: Panel keypad<br />
Multiple Central Stations: Primary and backup<br />
Approval Listings: FCC/IC and CE (UL and ULC pending)<br />
Substitution Detection: Monitoring of MAC address<br />
At this point, it’s obvious that the introduction of this device to the network needs to be prohibited by<br />
the IT group from the outset. The developer’s understanding of the IP stack is questionable at best, and<br />
it is certain that the deficiency in skill level will be passed down through the vendor channel and come<br />
to rest as a problem for the IT group, not the least of which will be security issues.<br />
There is no description of the IP stack of the device, (that is, list of protocols), and no visibility into the<br />
device if deployment requires administrative involvement by the IT group.<br />
The IP stack of the device is so under-developed that there is absolutely no way to predict how it will<br />
perform in a production environment. The apparent purpose of the device is to transmit security alarm<br />
signals over the network to eliminate a telephone line. This trivial expense advantage is certain to be<br />
eliminated in ongoing support costs.<br />
Using what tools would be available to a typical networker, we examine traffic from the device that we<br />
can see in the most basic implementation, which is a cross-over cable connected to a PC.<br />
When we sniff the traffic, we see ARP requests coming from the device, which at least allows us to<br />
discover the MAC address.<br />
Ethernet II (Packet Length: 64)<br />
Destination:<br />
Source:<br />
ff-ff-ff-ff-ff-ff<br />
00-03-4f-00-15-20<br />
Type: ARP (0x0806)