Government Security News
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
<strong>Government</strong> <strong>Security</strong> <strong>News</strong><br />
FEBRUARY/MARCH 2015 DIGITAL EDITION<br />
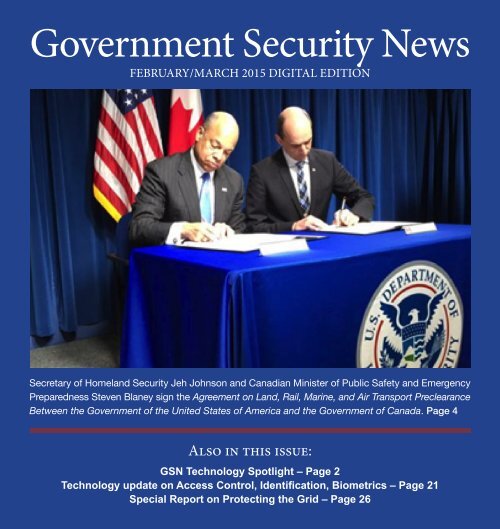
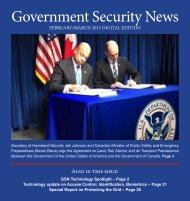
Secretary of Homeland <strong>Security</strong> Jeh Johnson and Canadian Minister of Public Safety and Emergency<br />
Preparedness Steven Blaney sign the Agreement on Land, Rail, Marine, and Air Transport Preclearance<br />
Between the <strong>Government</strong> of the United States of America and the <strong>Government</strong> of Canada. Page 4<br />
Also in this issue:<br />
GSN Technology Spotlight – Page 2<br />
Technology update on Access Control, Identification, Biometrics – Page 21<br />
Special Report on Protecting the Grid – Page 26
GSN February/March Digital Edition<br />
Table of Contents<br />
GSN TECHNOLOGY SPOTLIGHT<br />
Quantum Technology’s breakthrough in modern<br />
perimeter intrusion systems<br />
Mark Tinker is a scientist with a PHD in seismology. His company Quantum<br />
Technology has created a ground sensor system that measures vibrations<br />
in the earth from a distance beyond perimeter fences. With this technology,<br />
the company can provide earlier detection and classification of threat<br />
profiles ranging from vehicle activity, pedestrian activity, gunfire and lightning.<br />
Read all about this major breakthrough technology in the article by Mr.<br />
Tinker on Page 32<br />
InZero’s “WorkPlay” separates work and play at<br />
the hardware level<br />
In light of the kerfuffle regarding Hillary Clinton’s personal and official<br />
emails, the “WorkPlay Technology” from InZero Systems is starting to look<br />
like a very significant invention. Which is not surprising at all, when you<br />
consider that WorkPlay is the brainchild of Louis Hughes, who previously<br />
served as President of Lockheed Martin, CEO of General Motors International<br />
and Chief of Staff of the State Department’s Afghanistan Reconstruction.<br />
With Work/Play, there are two operating systems in a computer<br />
separated at the hardware level, one for work, one for play. Pretty simple?<br />
Not quite. Read more on Page Page 18<br />
2
NEWS AND FEATURES<br />
U.S. Canada Preclearance agreement Page 4<br />
Data Conversion Labs seeking participants in<br />
survey of content delivery outlets Page 6<br />
Federal Transit Administration awards nearly<br />
$55M for low and no emission buses Page 8<br />
International training essential to global stability<br />
and security Page 9<br />
PortVision CE0 blog discusses benefits and<br />
limitations of Automatic Identification<br />
Systems (AIS) Page 14<br />
Why small may be the new big for government<br />
access control providers, by Robert Laughlin,<br />
President, Galaxy Control Systems Page 16<br />
GSN Interviews Louis R. Hughes, CEO of<br />
cybersecurity start-up InZero Systems Page 18<br />
Curtiss-Wright and Airbus collaboration delivers<br />
pre-validated digital map solution Page 20<br />
Largest vessel ever calls on Savannah Page 22<br />
Transporting oil by rail: Is this a risk to national<br />
security? By K. Denise Rucker Krepp Page 24<br />
Access Control/ID and Biometrics Special Section<br />
Entrust Datacard announces new software suite<br />
for secure identification card issuance Page 27<br />
Identiv announces U.S. <strong>Government</strong><br />
FICAM Certification of uTrust TS <strong>Government</strong><br />
Readers for premises access Page 28<br />
Iris ID to enhance Canada Border Service<br />
NEXUS program using Iris Recognition Page 29<br />
Sonavation launches IDKEY featuring 3D biometric<br />
ultrasound surface scan technology Page 30<br />
Zwipe introduces HID Technology biometric<br />
cards for iCLASS ® and ProxCard ® Readers<br />
Page 31<br />
Protecting the Grid Special Section<br />
Quantum Technology’s breakthrough in modern<br />
perimeter intrusion systems, by Mark A. Tinker, PhD<br />
Page 32<br />
Challenges and solutions for substation security<br />
– applying smart thermal technology to prevent intrusions,<br />
by John Romanowich, CEO, SightLogix, Inc.<br />
Page 34<br />
Utah-Based Washakie Renewable Energy, LLC<br />
settles renewable fuel standard violations Page 36<br />
Excerpts from Chuck Brooks 2014 radio interview<br />
on the Dick Morris Show Page 38<br />
3
U.S./Canada sign preclearance agreement to<br />
reduce border congestion, increase efficiency<br />
WASHINGTON – Consistent<br />
with the initiatives outlined in<br />
the 2011 Beyond the Border Action<br />
Plan, Secretary of Homeland<br />
<strong>Security</strong> Jeh Johnson and Canadian<br />
Minister of Public Safety<br />
and Emergency Preparedness<br />
Steven Blaney today signed the<br />
Agreement on Land, Rail, Marine,<br />
and Air Transport Preclearance<br />
Between the <strong>Government</strong><br />
of the United States of America<br />
and the <strong>Government</strong> of Canada.<br />
This new agreement reaffirms the<br />
United States and Canada’s commitment<br />
to enhancing security<br />
while facilitating lawful travel<br />
and trade, and supersedes the existing<br />
U.S.-Canada Air Preclearance<br />
agreement signed in 2001.<br />
“After years of hard work<br />
and negotiations, today we have<br />
one of the most significant, visible,<br />
and anticipated products of<br />
the Beyond the Border initiative<br />
– a major achievement that will<br />
produce significant benefits for<br />
the United States and Canada,”<br />
said Secretary Johnson. “This<br />
agreement will help facilitate the<br />
legitimate trade and travel that<br />
keeps our economy thriving as<br />
we maintain utmost vigilance to<br />
the security of our borders. We<br />
remain committed to our deep<br />
partnership with Canada, a true<br />
ally, neighbor and friend of the<br />
United States.”<br />
“Our <strong>Government</strong>’s top priority<br />
remains creating jobs and<br />
opportunities for Canadians,”<br />
said Minister Blaney. “This historic<br />
new agreement builds on<br />
decades of successful preclearance<br />
operations in Canadian airports.<br />
It will enhance the security<br />
at our border and create jobs and<br />
growth in Canada by improving<br />
the flow of legitimate goods and<br />
4<br />
people between our two countries.”<br />
This Preclearance agreement<br />
– allowing for the immigration,<br />
customs and agriculture<br />
inspections required for entry<br />
into either country to occur on<br />
foreign soil – will reduce congestion<br />
and delays at the border<br />
and increase efficiency and predictability<br />
in cross-border travel,<br />
tourism and transportation. The<br />
new agreement provides officials<br />
of U.S. Customs and Border Protection<br />
(CBP) and Canada Border<br />
Services Agency (CBSA) with<br />
the requisite authorities and tools<br />
to conduct their border security,<br />
facilitation, and inspection processes<br />
in the other country.<br />
This agreement will:<br />
• Allow for the consideration<br />
of requests for new preclearance<br />
locations across all modes;<br />
• Enable exploration of co-location<br />
at small and remote ports,<br />
if desired;<br />
• Provide updates to the Air<br />
Preclearance Agreement to better<br />
reflect the post 9/11 operating
environment, including policies<br />
and tools utilized at domestic<br />
ports of entry;<br />
• Enable Canada to request<br />
that the United States regularize<br />
existing U.S. immigration preinspection<br />
sites – for example at<br />
cruise, rail and ferry terminals in<br />
British Columbia;<br />
• Enhance authorities for preclearance<br />
officers including the<br />
ability to carry firearms, defensive<br />
tools, and restraint devices to<br />
the same extent that Host Party<br />
officers are permitted to carry in<br />
the relevant operating environments;<br />
• Address officer privileges<br />
and immunities through a shared<br />
jurisdictional framework in<br />
which the sending country may<br />
generally exercise primary criminal<br />
jurisdiction for acts committed<br />
by its officers in the performance<br />
of official duties in the<br />
Host country; and<br />
• Retain the civil and administrative<br />
prosecutorial jurisdictions<br />
for preclearance officers<br />
provided for in the current Air<br />
Preclearance Agreement.<br />
Given the groundbreaking<br />
nature of the agreement, the<br />
United States and Canada must<br />
enact legislation for it to be implemented.<br />
The Civilian Extraterritorial<br />
Jurisdiction Act was<br />
introduced in the last Congress,<br />
and we are hopeful of its reintroduction<br />
in this Congress. Currently,<br />
the 2001 U.S.-Canada Air<br />
Transport Preclearance Agreement<br />
continues to apply.<br />
Preclearance is the process<br />
More on page 42<br />
THE NEW ENTRY<br />
for ACCESS CONTROL POINTS<br />
GUARANTEED DELIVERY DATES<br />
Established production methods allows us to<br />
provide short and accurate lead-time and delivery,<br />
keeping your project on schedule.<br />
FULLY GALVANIZED FRAMEWORK<br />
Corrosion resistance in trapped areas where heating<br />
and cooling cycles create moisture producing rust<br />
on conventional unprotected framework.<br />
CITADEL ® Gatehouse<br />
SINGLE SOURCE FOR PHYSICAL SECURITY<br />
Ameristar manufactures an array of perimeter security<br />
products. These products range from active vehicle<br />
barriers, gate systems (gates, operators and access<br />
controls), security fence and now guard booths.<br />
a<br />
AMERISTARBOOTHS.COM | 855.526.6847<br />
5
Data Conversion Labs seeking participants in<br />
survey of content delivery outlets<br />
Technical communicators, tools<br />
vendors, consultants, and even<br />
client organizations and end users<br />
all feel the rapid changes<br />
coming to content preparation,<br />
delivery and consumption. To<br />
better understand these changes<br />
over time Data Conversion Laboratory<br />
(DCL) and The Center<br />
for Information-Development<br />
Management (CIDM) are now<br />
conducting their third annual<br />
survey of practitioners, Following<br />
the Trends — Is Your Content<br />
Ready?, which is open now until<br />
March 16, 2015.<br />
“Content creation, management<br />
and delivery grows more<br />
complex, seemingly daily,” said<br />
DCL CEO Mark Gross. “Understanding<br />
the trends, challenges<br />
and needs of the technical communications<br />
industry, and how<br />
they change over time opens the<br />
doors to provide better solutions<br />
and evolving best practices to<br />
benefit practitioners, their organizations<br />
and their customers.”<br />
The first survey, conducted in<br />
early 2013, found that content<br />
providers in most organizations<br />
take on multiple roles. And a<br />
comparison<br />
of those roles<br />
with 2014 results<br />
shows an<br />
increasing percentage<br />
have<br />
responsibilities<br />
in technical<br />
support and in<br />
customer service.<br />
In addition,<br />
the number<br />
and variety<br />
of channels to<br />
which content is published are<br />
increasing, especially in the areas<br />
of mobile apps and mobile device<br />
delivery. The 2015 survey should<br />
uncover how these and other key<br />
areas are continuing to shift.<br />
“While many technical<br />
communicators believe their<br />
competitors are ahead of them in<br />
delivering quality content electronically,<br />
roughly half of our<br />
respondents in 2014 believe they<br />
are ready to support their organizations’<br />
business requirements<br />
for digital content,” notes Joann<br />
Hackos, Director for CIDM. “We<br />
think it’s critical to stay on top<br />
of the barriers to digital content<br />
6<br />
delivery from the business and<br />
technology perspectives, so that<br />
providers can plan for and actually<br />
meet their organization’s<br />
business requirements.”<br />
Invitations to participate<br />
in the survey have been sent to<br />
previous participants; the survey<br />
is available at: http://www.dclab.<br />
com/resources/surveys/dcl-cidm-trends-survey-2015.<br />
About Data Conversion<br />
Laboratory, Inc. (DCL)<br />
DCL (www.dclab.com) is a leader<br />
in helping organizations grow<br />
the value of their content assets<br />
investment. With digitization
and content management expertise<br />
across multiple industries<br />
including publishing, life sciences,<br />
government, manufacturing,<br />
technology and professional<br />
organizations, DCL uses its advanced<br />
technology and U.S.-<br />
based project management teams<br />
to help solve the most complex<br />
conversion challenges securely,<br />
accurately and on time. Founded<br />
in 1981, DCL was named to<br />
EContent’s Top 100 Companies<br />
in the Digital Content Industry<br />
in 2014 for the fourth straight<br />
year.<br />
About the Center for<br />
Information-Development<br />
Management (CIDM)<br />
The Center for Information-Development<br />
Management (CIDM)<br />
brings together the most highly<br />
skilled and talented managers<br />
in the field of information development<br />
from across the US<br />
and internationally to facilitate<br />
the sharing of information about<br />
current trends, best practices,<br />
and developments within the industry,<br />
from information development<br />
to training and support.<br />
Contact: Ariane Doud, Warner<br />
Communications,<br />
(978) 283-2674, Email<br />
PHYSICAL SECURITY<br />
with COMPLETE PERIMETER CONTROL<br />
ANTI-CLIMB FENCE RETRACTABLE WEDGES ANTI-RAM FENCE SECURITY BOLLARDS<br />
Call our perimeter security specialist at 866-467-2773 and visit us online at ameristarsecurity.com<br />
7
Federal Transit Administration awards nearly<br />
$55M for low and no emission buses<br />
The Federal Transit Administration<br />
(FTA) has announced<br />
awards to 10 project teams to<br />
deploy 55 low and no emission<br />
fuel cell, battery electric and electric<br />
hybrid buses in neighborhoods<br />
from Stockton, California<br />
to Canto, Ohio. 38 of the 55 will<br />
be either electric or fuel cell powered<br />
and produce zero tailpipe<br />
emissions.<br />
“This critical FTA program<br />
will help spur the growth of the<br />
advanced tech bus industry in<br />
the United States, which is a crucial<br />
part of the effort to meet our<br />
national air quality and climate<br />
challenges,” said CALSTART<br />
President and CEO John Boesel.<br />
“We are especially pleased to be<br />
working with three of the FTA<br />
awardees and helping to make<br />
zero buses competitive with existing<br />
diesel technology,” he continued.<br />
Newly established under the<br />
Moving Ahead for Progress in the<br />
21st Century Act (MAP-21), the<br />
FTA’s LoNo program focuses on<br />
deploying the cleanest and most<br />
energy-efficient U.S.-made transit<br />
buses designed to cut carbon<br />
8<br />
pollution and other traditional<br />
pollutants. Grants from the LoNo<br />
program help transit agencies<br />
integrate more of these cuttingedge<br />
buses into their fleets.<br />
The FTA provided a total of<br />
$54,469,249 in total for 10 projects<br />
nationwide. FTA received<br />
50 project proposals requesting<br />
a total of $200 million. See<br />
the FTA’s web site for more details:<br />
http://www.fta.dot.gov/<br />
grants/15926_16268.html<br />
CALSTART will work with<br />
three partner transit agencies on<br />
projects totaling nearly $24 million.<br />
The organization will assist<br />
its partners by providing various<br />
consulting services, such as<br />
data collection, analysis, surveys,<br />
specification alignment, and<br />
transit bus acquisition services.<br />
CALSTART partners awarded<br />
grants include the following projects:<br />
• Stark Area Regional Transit<br />
Authority (SARTA) will receive<br />
$8,877,405 to purchase and<br />
deploy five hydrogen fuel cell<br />
buses from the Integrated Product<br />
Team of Ballard Power Systems,<br />
BAE Systems, and ElDorado<br />
National. The agency will use<br />
the new zero-emission buses in a<br />
variety of operating conditions,<br />
including congested downtown<br />
streets, major urban roads and<br />
rural highways. SARTA provides<br />
more than 2.7 million rides per<br />
year throughout Stark County,<br />
Ohio, including servicing Canton,<br />
where the NFL Hall of Fame<br />
is located.<br />
• SunLine Transit Agency<br />
will receive $9,803,860 to build<br />
and deploy five hydrogen electric<br />
hybrid fuel cell buses. BAE Systems,<br />
Ballard Power Systems and<br />
ElDorado National will team up<br />
to build the new zero-emission<br />
buses. This project will increase<br />
SunLine’s current fleet of hydro-
gen electric hybrid fuel cell buses<br />
and allow the agency to offer<br />
expanded transit service in the<br />
Coachella Valley area of Southern<br />
California.<br />
• San Joaquin Regional<br />
Transit District (RTD) will receive<br />
$ 4,702,011 and purchase<br />
five Proterra battery-electric buses<br />
and a charging station. RTD,<br />
the transit provider for Stockton<br />
and San Joaquin County<br />
in California, plans to add the<br />
zero-emission buses and charging<br />
station to expand service and<br />
increase capacity at the Stockton<br />
Downtown Transit Center, which<br />
is the transfer point for nearly all<br />
of the RTD’s routes. Under a previous<br />
grant from the California<br />
Energy Commission the RTD<br />
purchased its first two zero emission<br />
electric buses.<br />
About CALSTART<br />
CALSTART and its 140+ member<br />
companies are dedicated<br />
to expanding and supporting a<br />
clean transportation industry<br />
that cleans the air, creates jobs<br />
and economic opportunities, reduces<br />
greenhouse gas emissions<br />
and secures our transportation<br />
energy future. For further information<br />
visit www.calstart.org/<br />
International training essential<br />
to global stability and security<br />
By Scott Seavers,<br />
Salient Federal Solutions<br />
As long as there are people<br />
on this great planet, there will be<br />
conflict and a natural tendency<br />
toward instability, regionally at a<br />
minimum. While we can’t change<br />
that, we can set the best conditions<br />
possible to avoid escalation<br />
and to minimize the periods of<br />
insecurity and security assistance,<br />
specifically international<br />
training, plays a critical role in<br />
the overall outcome.<br />
The U.S. military is shrinking,<br />
the U.S. alone cannot maintain<br />
global stability, and security<br />
assistance missions are some of<br />
the first cuts as the U.S. defense<br />
budget wanes. While cutting U.S.<br />
defense budgets is a stark reality<br />
of our time, cutting security assistance<br />
runs counter to President<br />
Obama’s recently released<br />
2015 National <strong>Security</strong> Strategy<br />
which highlights the need for the<br />
U.S. to “lead with capable partners”<br />
and acknowledges the fact<br />
that global problems require U.S.<br />
participation, but that few can be<br />
9<br />
solved by the U.S. alone. While a<br />
robust Department of Defense is<br />
absolutely essential and a critical<br />
component in ensuring national<br />
and global security, increasing<br />
partner nation capability is a costeffective<br />
force multiplier. Now is<br />
hardly the time to pull back from<br />
training our partners to defend<br />
themselves and to function effectively<br />
in coalitions.<br />
Language and cultural differences<br />
make training together<br />
far from easy, yet militaries have<br />
been training together for centuries.<br />
Foreign militaries that can<br />
defend their homelands autonomously<br />
and contribute to coalitions<br />
enhance global security exponentially.<br />
We are all firsthand<br />
witnesses to the results effective<br />
international training can attain.<br />
More on page 26
Sponsored by:<br />
ONE EVENT<br />
EVERYTHING SECURITY<br />
REGISTER TODAY AT ISCWEST.COM/GSN<br />
10
2015 Airport/Seaport/Border <strong>Security</strong> Awards<br />
Now Accepting Entries!<br />
<strong>Government</strong> <strong>Security</strong> <strong>News</strong> would like to take this opportunity to invite all Technology<br />
Vendors, Airport, Seaport and Border <strong>Security</strong> Officers, Executives and <strong>Security</strong> Teams<br />
to visit the GSN 2015 Awards website at www.asbsecurityawards.com, review the<br />
37 updated entry categories, and if you find one or more of them that fits your company<br />
or agency, go for the gold!<br />
And we mean that literally, because all winners will<br />
receive a handsome, gold-trimmed plaque that you<br />
can post in your office or other prominent position,<br />
and all Winners and Finalists will be invited to post<br />
their winning entries and additional information in our 2015 Yearbook of Airport,<br />
Seaport, Border <strong>Security</strong> Awards Recipients.<br />
It’s great publicity and exposure in <strong>Government</strong> <strong>Security</strong> <strong>News</strong>, which is sure to be further<br />
enhanced by Google and the other Search engines and Social Media. Check out<br />
the many new categories in the 2015 entry categories and be sure to see the kind of<br />
distinguished company you’ll be in as a Winner or Finalist by looking through our 2014<br />
Yearbook of Airport, Seaport, Border <strong>Security</strong> Awards at:<br />
http://www.gsnmagazine.com/2014ASB<strong>Security</strong>Yearbook.<br />
11
PortVision CE0 blog discusses benefits and limitations<br />
of Automatic Identification Systems (AIS)<br />
By Dean Rosenberg,<br />
CEO, Portvision<br />
As many of the readers of this<br />
blog already know, Automatic<br />
Identification System (AIS) is<br />
a VHF protocol that has been<br />
mandated on large vessels by<br />
IMO for collision avoidance<br />
and to enhance navigation since<br />
2005. Every vessel over 300 gross<br />
tons (or over 65 feet in the USA)<br />
carries an AIS transponder that<br />
receives broadcasts from nearby<br />
vessels, and also transmits identifying<br />
information about the<br />
vessel carrying the transponder.<br />
Information including a ship’s location,<br />
speed, and identifying information<br />
is transmitted multiple<br />
times per minute when a vessel is<br />
underway, and every few minutes<br />
when docked. You can view all<br />
details associated with the AIS<br />
specification at the USCG Navigation<br />
Center website.<br />
Once AIS became a global<br />
standard, the industry realized<br />
that in addition to leveraging<br />
the safety benefits of AIS in the<br />
wheelhouse, organizations could<br />
also drive significant value in<br />
their shore-side operations by<br />
using AIS to increase visibility<br />
and transparency to vessel movements<br />
around the world. Port-<br />
Vision launched its web-based<br />
service in 2007, and has since expanded<br />
to provide global coverage<br />
with a network of AIS receivers<br />
around the world.<br />
The challenge with a shorebased<br />
AIS service is that an individual<br />
AIS receiver is limited<br />
Photo: Institute of Aeronautical Technology<br />
to about a 50 mile radius. Ship<br />
tracking through shore-based<br />
(also known as “terrestrial”) AIS<br />
requires that each vessel be within<br />
50 miles of an AIS receiver in<br />
order to be tracked in the system.<br />
Terrestrial AIS provide significant<br />
value to users, including<br />
providing near-real-time vessel<br />
tracking when vessels are near<br />
shore. However, once a ship is<br />
in open water, terrestrial AIS<br />
becomes less effective. Initially,<br />
PortVision took steps to increase<br />
14
coverage of AIS network by adding<br />
receivers on offshore assets<br />
such as offshore platforms and<br />
workboats in high-density areas<br />
such as the Gulf of Mexico. However,<br />
while expanding visibility in<br />
those areas, the offshore receivers<br />
still did not address the challenge<br />
of tracking ships at sea.<br />
In 2008, the first commercial<br />
AIS receivers were launched<br />
into orbit as a satellite payload.<br />
The initial satellite launches<br />
were largely experimental, and<br />
demonstrated that it indeed was<br />
possible to detect AIS signals of<br />
vessels in open water from an<br />
orbiting satellite. This kicked off<br />
the era of satellite AIS, as several<br />
commercial operators began offering<br />
satellite AIS services to<br />
both government and commercial<br />
clients.<br />
From a wheelhouse perspective,<br />
satellite AIS provides<br />
minimal value. However, from<br />
a shore-based business perspective,<br />
satellite AIS provides many<br />
benefits, including:<br />
• Ability to track any AIStransmitting<br />
vessel globally<br />
• Ability to support searchand-rescue<br />
and anti-piracy measures<br />
by increasing the visibility<br />
of ships at sea by first responders<br />
and security personnel<br />
• Ability to provide market<br />
intelligence through aggregating<br />
data across many vessels and<br />
regions to answer business questions<br />
• Ability to support compliance<br />
and law enforcement activities<br />
The above benefits are compelling.<br />
However, it is also important<br />
to recognize the limitations<br />
of satellite AIS<br />
Much lower reporting frequency.<br />
While terrestrial AIS can<br />
report vessel positions in nearreal-time<br />
(with multiple updates<br />
each minute), satellite AIS has<br />
significantly higher latency and<br />
lower frequency of reporting.<br />
Current satellite AIS service providers<br />
typically provide position<br />
updates on specific vessels only<br />
a few times each day. While this<br />
lower frequency of reporting still<br />
provides compelling value to<br />
track the progress of ships at sea,<br />
it does not allow for many of the<br />
advanced alerting and reporting<br />
features that are available with<br />
terrestrial AIS.<br />
Limited detection of vessels.<br />
The ability to detect AIS signals<br />
from space is currently an imperfect<br />
“art”. Electromagnetic interference<br />
(particularly in dense<br />
areas) often limits the ability to<br />
detect vessels in congested areas,<br />
even when vessels are transmitting<br />
their AIS signal.<br />
Cost. It is expensive to<br />
launch a satellite, and the commercial<br />
satellite operators need<br />
to recoup that investment. As<br />
such, satellite AIS typically carries<br />
significantly higher licensing<br />
fees than terrestrial-only AIS<br />
providers.<br />
PortVision has been providing<br />
satellite AIS to customers<br />
since the first satellites were<br />
launched over 5 years ago. We<br />
continue to maintain a leadership<br />
position in aggregating terrestrial,<br />
offshore, and satellite<br />
AIS to provide the highest-value<br />
offering to our users. Combined,<br />
we process over 50 million ship<br />
location reports per day from all<br />
AIS sources in our network. And<br />
satellite AIS data plays an important<br />
role for many of our users,<br />
particularly those users who require<br />
in-transit visibility to ships<br />
around the world.<br />
15
Why small may be the new big for government<br />
access control providers<br />
by Robert Laughlin,<br />
President, Galaxy Control Systems<br />
Access control conglomerates<br />
have undergone a lot of changes,<br />
with some being<br />
formed by combining<br />
smaller companies,<br />
and others being dissolved<br />
with individual<br />
companies re-emerging.<br />
This has been interesting<br />
to watch,<br />
particularly for independent<br />
access control<br />
companies in the market. With<br />
this in mind, end users must<br />
take a hard look at the potential<br />
ramifications of dealing with<br />
large companies versus small/<br />
medium-sized providers. Access<br />
control systems require ongoing<br />
service and support to ensure<br />
continuous and reliable operation,<br />
and small/medium providers<br />
are well-positioned to excel in<br />
these areas because of their focus<br />
on both technology and customer<br />
relations.<br />
With government customers,<br />
all access control companies<br />
must be knowledgeable about<br />
and mindful of GSA schedules<br />
and the regulations and requirements<br />
that apply to particular entities.<br />
That’s why providers in this<br />
space must have security-cleared<br />
personnel<br />
on staff to help navigate<br />
these waters. Beyond<br />
that, there are a<br />
number of areas where<br />
small/medium companies<br />
are uniquely positioned<br />
to outperform<br />
larger companies.<br />
Innovation<br />
Every government facility and installation<br />
is unique, even facilities<br />
built using the same construction<br />
and design models. Unfortunately,<br />
off-the-shelf access control solutions<br />
rarely provide the versatility<br />
individualized installations<br />
require. Customization poses<br />
challenges for larger companies,<br />
who typically leave that task to<br />
installing dealers or end users’<br />
in-house technicians. Given the<br />
high stakes of government security,<br />
it’s difficult to argue that this<br />
16<br />
seat-of-the-pants customization<br />
is ideal.<br />
Small/medium providers,<br />
however, thrive on customization<br />
and focus on catering to customers’<br />
specific needs. To compete<br />
against large companies’ marketing<br />
budgets and sophisticated<br />
sales pitches, smaller providers<br />
must innovate with new solutions<br />
and remain conscious of<br />
customers’ investments in legacy<br />
technologies. New solutions that<br />
address longstanding problems<br />
and integrate with legacy and future<br />
deployments are innovative;<br />
rip-and-replacement solutions<br />
are not.<br />
Personal connections<br />
All customers want to feel that<br />
their provider understands their<br />
needs and can connect with<br />
them, particularly government<br />
clients, who have very specific<br />
procurement and purchasing requirements.<br />
All providers working<br />
with government entities<br />
retain employees who understand<br />
these nuances, but only<br />
smaller companies can provide
deeper, more personal relationships<br />
with someone who “speaks<br />
the language.” Interestingly, large<br />
companies often invest heavily<br />
in emulating these relationships<br />
that come naturally to smaller<br />
companies.<br />
Communication<br />
Today, personal connections<br />
seem to be scarcer than ever. The<br />
barrage of 24/7/365 communications<br />
certainly contributes,<br />
creating greater demands on<br />
people’s time. This is a challenge<br />
for larger companies, where the<br />
volume of internal interactions<br />
further hinders timely response<br />
to important issues. Delays are<br />
unacceptable for government<br />
agencies, especially those tasked<br />
with highly sensitive or missioncritical<br />
operations that cannot be<br />
interrupted while waiting for a<br />
callback.<br />
Smaller companies have<br />
clearer and more direct lines of<br />
communication that enable faster<br />
response. Generally, whoever<br />
sold the system supports their<br />
customers and can spend more<br />
time communicating with them.<br />
Delays compromise security, so<br />
customers deserve a go-to person<br />
they can rely on when they<br />
need them most – typically when<br />
something goes wrong and requires<br />
immediate attention.<br />
Timely decision-making<br />
Decision-making tends to move<br />
slowly for large organizations,<br />
which comprise numerous levels<br />
of hierarchy and specialized<br />
roles that require authorized personnel<br />
to collect and review data<br />
before taking action. Again, delays<br />
are not a viable option in the<br />
government space. For smaller<br />
companies, reporting paths to<br />
decision-makers are shorter, enabling<br />
faster resolution of critical<br />
issues.<br />
Executive involvement<br />
Large companies’ top-level executives<br />
make decisions that affect<br />
customers, often without<br />
direct involvement with those<br />
customers or everyday management<br />
issues. The opposite is true<br />
of small/medium companies,<br />
where upper-level management<br />
normally has personal interaction<br />
with customers and is aware<br />
of trends and issues that impact<br />
technology.<br />
Access to ownership<br />
17<br />
There are big differences between<br />
working directly with the owners<br />
of a small/medium company and<br />
dealing with employees at larger<br />
companies. Owners want a customer<br />
for life – not just a single<br />
sale or project – and will work<br />
hard to ensure satisfaction. This<br />
often creates a top-down corporate<br />
culture of providing superior<br />
service, support and satisfaction,<br />
which big business strives to emulate.<br />
Large access control providers<br />
play a major role in the continued<br />
development and evolution<br />
of advanced access control<br />
technologies. But technology<br />
is just one part of the equation.<br />
A combined focus on technology<br />
and customer service allow<br />
smaller companies to provide the<br />
high level of ongoing service and<br />
support crucial to ensuring reliability<br />
and performance of access<br />
control systems long after the<br />
sale. The key is to remember that<br />
big is not always better and that<br />
success and growth don’t mean a<br />
company has to become or even<br />
act big. A personal touch and access<br />
to management and ownership<br />
allow small/medium companies<br />
to treat every customer<br />
like they’re the biggest customer.<br />
As a result, the fast response and<br />
quick resolution provide government<br />
and other end users with<br />
the level of service and reliability<br />
they should expect from an access<br />
control partner.
GSN Interviews Louis R. Hughes,<br />
CEO of cybersecurity start-up InZero Systems<br />
GSN: Lou, you’ve had an illustrious<br />
career as an international<br />
executive, public company Board<br />
member and government leader.<br />
What led you to take on the challenge<br />
of cyber security technology<br />
with InZero ?<br />
LH: It was an opportunity offered<br />
me several years ago, when<br />
it had become apparent that software<br />
security is a never-ending<br />
battle between solution providers<br />
and cyber criminals. It’s just<br />
a matter of time before malware<br />
is created to overcome a given<br />
solution. InZero instead devoted<br />
itself to hardware-based security,<br />
and our experience with prior<br />
technologies in this genre gave us<br />
the expertise to develop Work-<br />
Play Technology.<br />
GSN: What is “WorkPlay Technology”?<br />
LH: It’s a way to create multiple<br />
operating systems (OS) running<br />
inside a computer using a single<br />
ARM processor, as virtually all<br />
popular devices have. But unlike<br />
other methods for data separation<br />
like dual persona or containerization,<br />
we provide hardwareseparated<br />
OS’s.<br />
GSN: What do you mean by<br />
“hardware-separated”?<br />
LH: Each OS has its own kernel,<br />
memory and storage, so in effect<br />
these OS’s are completely separated<br />
at the hardware level. Other<br />
18<br />
data separation or dual persona<br />
methods share resources that allow<br />
malware to spread and compromise<br />
security.<br />
GSN: What’s the benefit of your<br />
hardware-separated OS’s?<br />
LH: This literally solves half the<br />
problem of using a computer for<br />
both enterprise and personal activity.<br />
GSN: Can you explain how<br />
WorkPlay Technology solves<br />
“half the problem”?<br />
LH: It solves the personal use<br />
half. When you use a computer<br />
for both work and personal activity,<br />
you’ve added significant risk<br />
that your personal activity introduces<br />
malware that can access<br />
your business data and networks.<br />
WorkPlay Technology eliminates<br />
this risk, because one OS can’t<br />
access another. So if you use one<br />
OS for business and one for personal<br />
use, your personal activity<br />
can’t access the business OS, and<br />
therefore can’t compromise busi-
ness data including, critically,<br />
accessing the business intranet.<br />
Your IT administrator no longer<br />
has to worry about what you<br />
do personally. Hence, half of the<br />
problem is solved. And for an<br />
added benefit, the user’s privacy<br />
in using the personal OS can also<br />
be assured.<br />
GSN: How is it used – how would<br />
I go back and forth between business<br />
and personal computing?<br />
LH: It’s easy. You just click the<br />
switch icon to move to the other<br />
OS. Takes about 3 seconds. This<br />
allows the open OS to hibernate<br />
and activates the second OS. We<br />
also provide optional password<br />
authentication. It’s just like opening<br />
an app, and entering a password.<br />
GSN: Do you think WorkPlay<br />
Technology is a game-changer, a<br />
real difference-maker?<br />
LH: Well, you can buy two mobile<br />
devices or laptops if you<br />
want, use one for business and<br />
one personally. Of course even<br />
then you’d have to keep both<br />
open or constantly boot up.<br />
But using just one device instead<br />
of two? Yes it changes the game<br />
in several ways: So long as you<br />
use the same resources, like one<br />
kernel, a software method like<br />
containers or hypervisors is susceptible<br />
to malware that gains the<br />
elevated privileges to access the<br />
entire device. Is this a real threat?<br />
Ponemon just issued a new report<br />
and 38% of the respondents<br />
found container and other security<br />
like complex firewalls still<br />
vulnerable. In point of fact, over<br />
the last year, we have been reading<br />
about the vulnerabilities of<br />
these methods constantly. Moreover,<br />
our own technical people<br />
discovered multiple vulnerabilities<br />
in existing mainstream products<br />
when we were evaluating<br />
their compatibility with Work-<br />
Play Technology. So I’ll say it as<br />
a rhetorical question - - why not<br />
take half the risk away?<br />
GSN: Why wouldn’t WorkPlay<br />
Technology replace existing dual<br />
persona solutions?<br />
LH: Because you still would often<br />
want those solutions inside<br />
at least the business OS. Think<br />
of WorkPlay Technology as a<br />
unique, secure and cost-effective<br />
method to provide truly two devices<br />
in one. Everything else is<br />
the same. The apps, the security,<br />
all the same. You may still want<br />
19<br />
other solutions to protect data inside<br />
an OS. And these days, it is<br />
more important than ever to protect<br />
the end user device as much<br />
as you can.<br />
GSN: Why is that now increasingly<br />
important?<br />
LH: It’s evidently become the<br />
path of least resistance, often<br />
through phishing and spearphishing.<br />
While SONY received<br />
extensive publicity for its data<br />
breach, but meanwhile, we’ve<br />
lost untold amounts of government<br />
data through cybercrime<br />
like Operations Pawn Storm and<br />
Cleaver. Unwittingly, government<br />
and military personnel introduced<br />
malware by simply clicking<br />
“Like” on Facebook, exposing<br />
government data. Moreover,<br />
cybercrime like Pawn Storm has<br />
been going on for seven years, say<br />
the reports. Social media are also<br />
being targeted more and more:<br />
Facebook and YouTube were the<br />
sources of several large breaches<br />
last year. In the case of the most<br />
publicized enterprise breaches,<br />
like Target and Home Depot,<br />
over a hundred million records<br />
were exposed through a phishing<br />
attack. I’m not saying they all<br />
More on page 41
Curtiss-Wright and Airbus<br />
collaboration delivers pre-validated<br />
digital map solution<br />
ASHBURN, Va. - March 17, 2015<br />
– Curtiss-Wright Corporation<br />
(NYSE: CW) today announced<br />
that its Defense Solutions division,<br />
in collaboration with Airbus<br />
Defence and Space, has introduced<br />
the SferiAdvise System<br />
Ready Application (SRA), a new<br />
pre-validated, pre-tested digital<br />
map, flight plan, and helicopter<br />
terrain awareness and warning<br />
system (HTAWS) solution. It<br />
provides system designers with<br />
a verified software and commercial-off-the-shelf<br />
(COTS) module<br />
solution, yet adds no additional<br />
cost. The SferiAdvise SRA, which<br />
supports both 3U VPX and 6U<br />
VME form factor modules, eases<br />
and speeds the integration of<br />
digital map and mission management<br />
applications in defense and<br />
aerospace rotary-wing platforms.<br />
“We are very pleased to collaborate<br />
with Airbus Defence<br />
and Space to offer system integrators<br />
pre-tested and pre-validated<br />
cost-effective solutions for digital<br />
mapping and mission management,”<br />
said Lynn Bamford,<br />
Senior Vice President and<br />
General Manager, Defense<br />
Solutions division. “Our<br />
System Ready Application<br />
approach reduces design risk and<br />
cuts costs and time to market,<br />
helping to ensure the success of<br />
our customers’ system designs.”<br />
SferiAdvise SRA Performance<br />
Features:<br />
• Digital Map: Capable of displaying<br />
raster maps in all relevant<br />
formats and scales in accordance<br />
with the requirements defined by<br />
DO-257.<br />
• Flight Plan: In accordance<br />
with DO-257, the SferiAdvise<br />
SRA uses the GAMA protocol<br />
interface to receive and display<br />
flight plan information from<br />
a Flight Management System<br />
(FMS). When not interfaced to<br />
the FMS, it can process and display<br />
pre-loaded flight plans in<br />
accordance with real-time navigation<br />
data.<br />
• HTAWS: The SferiAdvise<br />
SRA provides predictive (as opposed<br />
to reactive) aural and visual<br />
warnings of terrain and ob-<br />
20<br />
stacle threats in accordance with,<br />
and surpassing, the requirements<br />
of DO-309 for rotary wing platforms.<br />
The SferiAdvise SRA combines<br />
the Airbus Defence and<br />
Space’s popular SferiAdvise<br />
Digital Map and Mission Management<br />
Solution and Curtiss-<br />
Wright rugged VPX-based commercial-off-the-shelf<br />
(COTS)<br />
board-sets. Two different configurations<br />
of the SferiAdvise<br />
SRA are currently available, one<br />
for use in VPX-based systems<br />
and the other for use with VME<br />
architectures.<br />
The pre-validated VPX<br />
board-set consists of Curtiss-<br />
Wright’s recently announced<br />
VPX3-150 3U VPX Single Board<br />
Computer (SBC) and VPX3-718<br />
Graphics Controller Module.<br />
Both of these compact, small<br />
form factor boards support DO-<br />
254 DAL C and DO-178C DAL
C certifiability to speed development<br />
while reducing the cost and<br />
risk of safety-certifiable aviation<br />
systems. The associated DO-178B<br />
DAL C certification artifacts are<br />
also available for SferiAdvise.<br />
The VME board-set combines<br />
SferiAdvise and Curtiss-<br />
Wright’s VME-186 SBC and<br />
XMC-715 Graphics Controller<br />
mezzanine card. This board-set,<br />
designed for applications that require<br />
higher performance, supports<br />
certifiability to DO-178C<br />
DAL C.<br />
About Curtiss-Wright SRAs<br />
Curtiss-Wright’s pre-verified<br />
SRA solutions reduce design risk<br />
from the process of integrating<br />
new application functionality<br />
into embedded systems without<br />
adding cost. Because the test and<br />
verification for the software and<br />
Curtiss-Wright modules has already<br />
been performed, SRAs ease<br />
the development of demanding<br />
deployed applications, including<br />
digital moving maps, situational<br />
awareness, and cockpit<br />
and vehicle displays. Using these<br />
pre-qualified and validated SRAs<br />
to add capabilities such as HMI,<br />
Digital Maps and Cross Domain<br />
Solutions, significantly speeds<br />
their integration into embedded<br />
systems.<br />
SRA Advantages:<br />
• Complete hardware and<br />
software solution from Curtiss-<br />
Wright providing a single point<br />
of contact for the customer<br />
• Pre-tested and validated as<br />
an integrated solution<br />
• Minimizes design risk<br />
• Reduces cost and schedule<br />
Complete System Solutions<br />
The SferiAdvise SRA is the latest<br />
pre-tested, pre-validated<br />
hardware/software solution to<br />
be offered by Curtiss-Wright.<br />
SRA solutions are offered across<br />
all Curtiss-Wright system architectures<br />
by combining our<br />
wide range of Intel® and Power®<br />
Architecture-based SBCs, with<br />
our industry-leading graphics<br />
controllers and all the software<br />
components required. Curtiss-<br />
Wright’s wide range of hardware<br />
options, industry leading software<br />
support and wide range of<br />
chassis and integrated systems<br />
enables us to offer SRAs for<br />
integration into existing systems<br />
or packaged in a turnkey rugged<br />
deployable system.<br />
About Curtiss-Wright<br />
Corporation<br />
Curtiss-Wright<br />
21<br />
Corporation<br />
(NYSE:CW) is a global innovative<br />
company that delivers highly<br />
engineered, critical function<br />
products and services to the commercial,<br />
industrial, defense and<br />
energy markets. Building on the<br />
heritage of Glenn Curtiss and the<br />
Wright brothers, Curtiss-Wright<br />
has a long tradition of providing<br />
reliable solutions through<br />
trusted customer relationships.<br />
The company employs approximately<br />
9,000 people worldwide.<br />
For more information, visit www.<br />
curtisswright.com.<br />
About Airbus Defence and<br />
Space<br />
Airbus Defence and Space is a<br />
division of Airbus Group formed<br />
by combining the business activities<br />
of Cassidian, Astrium and<br />
Airbus Military. The new division<br />
is Europe’s number one defence<br />
and space enterprise, the second<br />
largest space business worldwide<br />
and among the top ten global<br />
defence enterprises. It employs<br />
some 40,000 employees generating<br />
revenues of approximately<br />
€14 billion per year.
Largest vessel ever calls on Savannah<br />
Indianapolis, IN, March 6 -- Less<br />
Savannah, Ga. - March 18, 2015 -<br />
The Georgia Ports Authority welcomed<br />
the largest ship ever to call<br />
on the Port of Savannah today<br />
when the ZIM Tianjin docked at<br />
Garden City Terminal.<br />
“This 10,000-TEU vessel<br />
represents the future of U.S.-Asia<br />
shipping,” said Georgia Ports Authority<br />
Executive Director Curtis<br />
J. Foltz. “The Tianjin is another<br />
example of a growing trend in<br />
the ocean carrier business toward<br />
larger, more efficient vessels.”<br />
The ship measures 1,145<br />
feet long by 150 feet wide. Stood<br />
on end, it would stand nearly as<br />
tall as the Empire State Building<br />
(1,454 feet, including its antenna).<br />
The vessel’s route originated<br />
in Qingdao, China, arriving on<br />
the U.S. East Coast via the Suez<br />
Canal. “The port call by the ZIM<br />
22<br />
Tianjin is another example of the<br />
strong and long standing professional<br />
relationship between GPA<br />
and ZIM,” said ZIM Vice President<br />
Brian Black. “We are very<br />
excited to have the largest vessel<br />
call Savannah!”<br />
GPA crews will make more<br />
than 2,000 container moves on<br />
and off the vessel during its time<br />
at dock.<br />
Foltz said ships in the Tian-
jin’s class provide lower cost per<br />
container slot for cargo owners -<br />
reducing the expense of delivering<br />
goods to customers at home<br />
and abroad. “The economy of<br />
scale achieved by Super Post-<br />
Panamax vessels is the reason<br />
we’re seeing more of them in<br />
Savannah, a trend that will only<br />
continue after an expanded Panama<br />
Canal opens in 2016.”<br />
In order to better accommodate<br />
Super Post-Panamax<br />
vessels, the Savannah Harbor<br />
Expansion Project will deepen<br />
the main river channel to 47 feet<br />
at low tide (averaging 54 feet at<br />
high tide). This month, the U.S.<br />
Army Corps of Engineers issued<br />
a $134.5 million contract that<br />
will mark the start of dredging.<br />
The contract covers deepening<br />
the outer harbor, extending 18.5<br />
miles into the Atlantic Ocean.<br />
Dredging the outer harbor<br />
constitutes about half of the project<br />
to deepen the 40-mile shipping<br />
channel and harbor from<br />
deep ocean to Garden City.<br />
Georgia has approved $266<br />
million in bonds to cover the<br />
state’s projected share of construction<br />
costs. As the $706 million<br />
expansion moves forward,<br />
construction funding will shift to<br />
federal dollars. Better accommodating<br />
larger, more efficient vessels<br />
such as the Tianjin will save<br />
U.S. companies moving goods<br />
through Savannah 20 to 40 percent<br />
on transportation.<br />
The Tianjin’s next stop is<br />
Kingston, Jamaica.<br />
Georgia’s deepwater ports<br />
and inland barge terminals support<br />
more than 352,000 jobs<br />
throughout the state annually<br />
and contribute $18.5 billion in<br />
23<br />
income, $66.9 billion in revenue<br />
and $2.5 billion in state and local<br />
taxes to Georgia’s economy.<br />
The Port of Savannah handled 8<br />
percent of the U.S. containerized<br />
cargo volume and 10.9 percent of<br />
all U.S. containerized exports in<br />
FY2013.
Transporting oil by<br />
rail: Is this a risk to<br />
national security?<br />
By K Denise Rucker Krepp<br />
24<br />
When a train<br />
carrying oil<br />
has an accident,<br />
the local<br />
community<br />
is the one<br />
that suffers.<br />
Residents are<br />
forced to leave<br />
their homes, sleep on gym floors,<br />
and pray that their lives return<br />
to normal. This suffering is increasing<br />
significantly as more<br />
and more trains derail around<br />
the country. One way to stop<br />
this suffering is to designate the<br />
oil transported by rail as security<br />
sensitive material. This designation<br />
automatically imposes<br />
greater safety and security measures<br />
and increased government<br />
oversight.<br />
Designating oil transported<br />
by rail as security sensitive material<br />
doesn’t require Congressional<br />
action. In 2007, Congress passed<br />
the Implementing the Recommendations<br />
of the 9/11 Commission<br />
Act. Section 1551 requires<br />
railroad carriers “to, no later than<br />
90 days after the end of each calendar<br />
year, compile security-sensitive<br />
materials commodity data.<br />
Such data must be collected by<br />
route, line segment, or series of<br />
line segments, as aggregated by<br />
the railroad carrier. Within the<br />
railroad carrier selected route,<br />
the commodity data must identify<br />
the geographic location of<br />
the route and the total number of<br />
shipments by the United Nations<br />
identification number for the security-sensitive<br />
materials.”<br />
Section 1551 also requires<br />
the railroad carriers to “provide a<br />
written analysis of the safety and<br />
security risks for the transportation<br />
routes identified in the security-sensitive<br />
materials commodity<br />
data collected.” Additionally,<br />
Section 1551 requires railroad<br />
carriers to “identify practicable<br />
alternative routes” and to examine<br />
the “risk of a catastrophic release<br />
from a shipment traveling<br />
along the alternate route compared<br />
to the primary route.”<br />
Unfortunately, the Obama<br />
Administration has not fully defined<br />
security sensitive material.<br />
Section 1501 of the 9/11 Act defines<br />
it as “a material, or a group<br />
or class of material, in a particular<br />
amount and form that the<br />
Secretary, in consultation with<br />
the Secretary of Transportation,<br />
determines, through a rulemaking<br />
with opportunity for public<br />
comment, poses a significant risk<br />
to national security while being<br />
transported in commerce due to<br />
the potential use of the material<br />
in an act of terrorism.”<br />
It’s been 8 years and the U.S.<br />
Department of Homeland Secu-
25<br />
rity has still not drafted the rule<br />
making. The Department indicated<br />
that it might do so soon in<br />
its Fall 2014 Regulatory Agenda.<br />
But hey, it’s been eight years so<br />
what’s the rush?<br />
The impetus to finally identifying<br />
security sensitive material<br />
and imposing greater rail safety<br />
and security precautions is Galena,<br />
Gogama, Timmis, and Mount<br />
Carbon. In each of these locations,<br />
trains derailed and local<br />
communities were upended. No<br />
longer could people sleep in their<br />
beds, drink their water, or safely<br />
breath the air. The environment<br />
was contaminated and remained<br />
so for weeks.<br />
More importantly from the<br />
homeland security perspective,<br />
these derailments demonstrated<br />
to potential terrorists the vulnerabilities<br />
to our nation’s rail<br />
system. If a train could derail<br />
by accident, imagine what type<br />
of damage a terrorist could do.<br />
Death and destruction on an unimaginable<br />
scale.<br />
So the first step in resolving<br />
the problem is for DHS to<br />
determine that oil by rail shipments<br />
pose a threat to national<br />
security. This shouldn’t be a significant<br />
hurdle. Multiple government<br />
agencies have involved in<br />
the response and recovery phases<br />
of these spills. They can testify to<br />
the monumental financial costs<br />
involved in cleaning up the accidents.<br />
The second step is to release<br />
the security sensitive rule making<br />
and hold public meetings. These<br />
meetings will allow residents<br />
from Galena, Gogama, Timmis,<br />
and Mount Carbon to explain in<br />
detail the suffering they endured<br />
when trains derailed in their<br />
communities.<br />
The government needs to<br />
understand the emotional toll a<br />
train accident it takes on a person.<br />
The toll of closely watching<br />
your children to make sure they<br />
don’t drink contaminated water.<br />
The toll it takes to grab your<br />
clothes and run out of the house,<br />
not sure if you will be able to return.<br />
It may not give you gray<br />
hair in two weeks, but you’ll definitely<br />
get an ulcer.<br />
Taken together, the suffering<br />
in Galena, Gogama, Timmis,<br />
and Mount Carbon, plus the 47<br />
people who died in Lac Megantic<br />
provide the justification for DHS<br />
to finally define security sensitive<br />
material and to include oil transported<br />
on trains within this definition.<br />
These communities have<br />
seen first hand the catastrophic<br />
nature of the accidents and its<br />
time for government to act.<br />
K. Denise Rucker Krepp is a homeland<br />
security and transportation<br />
security consultant. While serving<br />
as the Senior Counsel on the<br />
House of Representatives Homeland<br />
<strong>Security</strong> Committee, Ms.<br />
Krepp wrote the rail security provisions<br />
in the Implementing Recommendations<br />
of the 9/11 Commission<br />
Act.
International training essential to<br />
global stability and security<br />
Continued from page 9<br />
NATO forces have been training<br />
together from its establishment<br />
in 1949. Collectively NATO has<br />
experienced success in Afghanistan,<br />
Libya, the Balkans and<br />
Kosovo, and the coast of Africa<br />
just in the past 10 years. NATO’s<br />
success epitomizes the Aristotle<br />
saying “The whole is greater than<br />
the sum of its parts.”<br />
We are also firsthand wit-<br />
nesses to less than effective results.<br />
Part of ISIS’s success has<br />
come due to the lack of capability<br />
for indigenous forces to contain<br />
them. While foreign forces have<br />
been willing to participate for the<br />
most part, lack of capability has<br />
stifled the efforts. As the coalition<br />
of capable and interoperable<br />
forces increases, the success rate<br />
will go up.<br />
I’m certainly not an advocate<br />
of giving away all of our<br />
military secrets nor our best<br />
26<br />
equipment to foreign militaries.<br />
However, there is substantial<br />
benefit to providing our coalition<br />
and partner forces with comparable<br />
U.S. military capability. Writing<br />
the check for the equipment<br />
is actually the easy part though –<br />
the difficulty comes in effectively<br />
integrating and employing military<br />
equipment and capability.<br />
This is where security assistance<br />
via international training plays<br />
an important role – the ability to<br />
effectively operate autonomously<br />
and as interoperable partners<br />
in a coalition is as essential<br />
as having the capability in<br />
the first place. The resultant<br />
benefit is immeasurable and<br />
mitigates many of the risks<br />
we incur with a diminished<br />
U.S. military fighting force.<br />
Again, the whole is greater<br />
than the sum of its parts.<br />
Capable foreign military<br />
partners offer the U.S.<br />
many tangible benefits in<br />
terms of stability and security.<br />
First and foremost,<br />
strong foreign militaries act<br />
as a deterrent to aggression.<br />
Both internal and regional<br />
bad actors are less likely to<br />
take hostile action knowing<br />
a capable military is within<br />
More on page 42
Special Section: Access Control/ID and Biometrics<br />
Entrust Datacard announces<br />
new software suite for secure<br />
identification card issuance<br />
Entrust Datacard has announced the new Datacard®<br />
TruCredentialTM Suite Software which is<br />
designed to help organizations of all sizes deploy a<br />
secure ID program that meets a wide range of application<br />
requirements—from basic photo IDs to<br />
high-assurance credentials.<br />
The new software suite can be used to issue<br />
a variety of credentials such as student, faculty or<br />
visitor IDs; employee or contract badges; patient<br />
and staff healthcare IDs; credentials for local government<br />
programs; membership and customer<br />
loyalty cards; and transit passes.<br />
Available in four editions that allow organizations<br />
to easily scale from a single workstation<br />
to a multi-station, enterprise-wide application<br />
without increasing complexity – the TruCredential<br />
Suite offers a combination of functionalities.<br />
These include pre-configured card design templates<br />
that can be easily customized to develop<br />
unique designs; enrollment and data capture capabilities<br />
with support for QR code, photo and signature<br />
devices for capturing physical and logical<br />
cardholder data; workflow tools for reduced setup<br />
time; enterprise integration including physical<br />
access control system (PACS) interfaces; and<br />
smart card encoding support to drive operational<br />
efficiencies.<br />
“For most public and private organizations,<br />
the ability to positively identify employees, students<br />
and visitors serves as the foundation for effective<br />
security – and this requires a flexible, web<br />
based secure ID solution,” said Ryan Zlockie, vice<br />
president of software product marketing for Entrust<br />
Datacard. “We are pleased to offer a complete<br />
software suite that can support a wide range<br />
of issuance technologies that gives organizations<br />
the ability to determine precisely who should and<br />
who should not access their facilities.”<br />
For more information, please visit www.datacard.com/issuance-software/trucredential-software.<br />
About Entrust Datacard<br />
Consumers, citizens and employees increasingly<br />
expect anywhere-anytime experiences — whether<br />
they are making purchases, crossing borders, accessing<br />
e-gov services or logging onto corporate<br />
networks. Entrust Datacard offers the trusted<br />
identity and secure transaction technologies that<br />
make those experiences reliable and secure. Solutions<br />
range from the physical world of financial<br />
cards, passports and ID cards to the digital realm<br />
of authentication, certificates and secure communications.<br />
With more than 2,000 Entrust Datacard<br />
colleagues around the world, and a network of<br />
strong global partners, the company serves customers<br />
in 150 countries worldwide. For more information,<br />
visit www.entrustdatacard.com.<br />
27
Special Section: Access Control/ID and Biometrics<br />
Identiv announces U.S. <strong>Government</strong> FICAM Certification<br />
of uTrust TS <strong>Government</strong> Readers for premises access<br />
Identiv, Inc. (NASDAQ: INVE), a global security<br />
technology company that provides trusted identity<br />
solutions for premises, information, and everyday<br />
items, has announced that Identiv’s uTrust<br />
TS <strong>Government</strong> Readers for premises access are<br />
now included on the U.S. government’s FICAM<br />
Approved Products List (APL). The General Services<br />
Administration (GSA) lab, which is part of<br />
the Federal Identity, Credential, and Access Management<br />
(FICAM) Testing Program, has evaluated<br />
and approved Identiv’s uTrust TS <strong>Government</strong><br />
Readers.<br />
Identiv’s uTrust TS <strong>Government</strong><br />
Reader is specifically<br />
designed for U.S. government<br />
customers to support<br />
any existing building access<br />
system (such as Identiv, Lenel,<br />
AMAG, Honeywell, or<br />
Software House) and provide<br />
a forward path to FICAM<br />
compliance. Featuring high<br />
security with an inbuilt secure<br />
processor certified to the<br />
highest standards (EAL 6+), uTrust TS Readers<br />
support all major commercial and government<br />
access credentials, including U.S. government<br />
PIV, PIV-I, and CAC. Multiple form factors are<br />
available, including mullion and wall mount, with<br />
an upcoming keypad model.<br />
28<br />
Offering a seamless transition to standardsbased<br />
network cabling, uTrust TS Readers support<br />
simultaneous Wiegand, RS485, and Ethernet<br />
communication. Four independent processors<br />
combine to deliver the fastest building entry transaction<br />
times, speeding access and reducing user<br />
frustration. One reader can be used at all building<br />
access points, delivering secure, future-proof access,<br />
while simplifying purchasing and reducing<br />
deployment and management costs.<br />
“The uTrust TS <strong>Government</strong> Reader delivers a single<br />
cost-effective reader that<br />
supports all existing access<br />
systems and all major credential<br />
types, providing a clear<br />
path to a standards-based FI-<br />
CAM solution and migration<br />
to network cabling,” said Jason<br />
Hart, Identiv CEO. “Identiv<br />
Channel Alliance Network<br />
partners are able to deliver a<br />
product from an American<br />
company to 100% of the U.S.<br />
government marketplace, giving<br />
customers a cost-effective solution for over<br />
150,000 access points across all U.S. government<br />
buildings, recently mandated to adopt FICAM<br />
standards. uTrust TS <strong>Government</strong> Readers are<br />
available now and have already shipped to U.S.<br />
government customers.”
Identiv’s uTrust TS family of connected premises<br />
readers utilizes open, secure standards and a flexible,<br />
updatable platform design to support a broad<br />
range of access card technologies from proximity<br />
to public key infrastructure (PKI) at the door.<br />
Identiv’s uTrust TS Readers enable agencies to<br />
support existing access systems and migrate to a<br />
secure U.S. government FICAM solution at a fraction<br />
of the cost of other competitive solutions.<br />
uTrust TS Readers are available immediately<br />
through the Identiv Channel Alliance Network<br />
(ICAN) Global Partner Program and to original<br />
equipment manufacturer (OEM) partners<br />
through the uTrust Technology Partnership Program.<br />
Identiv’s approved products on the FICAM<br />
PACS APL can be downloaded here. For more information<br />
on the FICAM Testing Program, please<br />
click here.<br />
About Identiv<br />
Identiv is a global security technology company<br />
that establishes trust in the connected world, including<br />
premises, information, and everyday<br />
items. CIOs, CSOs, and product departments<br />
rely upon Identiv’s trust solutions to reduce risk,<br />
achieve compliance, and protect brand identity.<br />
Identiv’s trust solutions are implemented using<br />
standards-driven products and technology, such<br />
as digital certificates, trusted authentication, mobility,<br />
and cloud services. For more information,<br />
visit identiv.com.<br />
Iris ID to enhance<br />
Canada Border Service<br />
NEXUS program using<br />
Iris Recognition<br />
CRANBURY, N.J., and OTTAWA, ON—25 February<br />
2015 Iris ID in collaboration with IBM<br />
(NYSE:IBM) announced today that they are providing<br />
iris recognition technology to the Canada<br />
Border Services Agency’s NEXUS program. Enrolled<br />
travelers can now clear customs by simply<br />
looking into a camera that uses the eye’s iris as<br />
proof of identity.<br />
The biometric technology will improve security<br />
and expedite border clearance processes<br />
between Canada and the U.S. More than one million<br />
pre-approved members of the program will<br />
be able to use the authentication process at eight<br />
international airports in Canada, 19 land ports of<br />
entry, and approximately 430 marine locations.<br />
Members also benefit from expedited security<br />
screening lines in preclearance areas at dedicated<br />
immigration lanes at more than 100 participating<br />
U.S. airports.<br />
Charles Koo, CEO and President of Iris ID<br />
More on page 40<br />
29
Special Section: Access Control/ID and Biometrics<br />
Sonavation launches IDKEY featuring 3D biometric<br />
ultrasound surface scan technology<br />
Palm Beach Gardens-based Sonavation, a pioneer<br />
in biometric ultrasound technology for digital<br />
security, has announced the launch of its IDKEY<br />
biometric security key product line. IDKEY is the<br />
most complete FIDO Ready U2F/UAF solution<br />
for multi-factor authentication that securely protects<br />
logical and physical access to online systems,<br />
documents, files and facilities.<br />
IDKEY is powered by Sonavation’s patented<br />
3D biometric ultrasound surface scan technology,<br />
which provides the most in-depth scan of a user’s<br />
biometric fingerprint, creating a unique identifier<br />
for each user that is virtually unspoofable. IDKEY<br />
secures a users’ access across all digital touchpoints<br />
and is convenient, smart and simple, delivering<br />
peace of mind. With just a swipe of the finger,<br />
a user’s identity and online life are protected.<br />
“The current state of passwords is broken,”<br />
said Bob Stewart, COO, Sonavation. “Today, a<br />
hacker’s biggest opportunity is through the digital<br />
front door, which is often left open due to poor<br />
password security. We’ve seen multiple instances<br />
of this in the past few months alone – from the<br />
iCloud disaster to the recent Sony hack. The best<br />
approach to locking this door is with biometric<br />
technology. As our fingerprint scanning technology<br />
is the most well-developed and sound biometric<br />
approach, with IDKEY, we’re committed to<br />
giving consumers and businesses the most secure<br />
environment possible.”<br />
Eliminating unauthorized access to online<br />
accounts and files by providing all users with<br />
unique identifiers, IDKEY is fully compliant with<br />
FIDO universal 2nd factor (U2F/UAF) standards.<br />
With IDKEY, a user’s biometric information is<br />
stored on the device and off the grid. Additional<br />
features of the IDKEY product line include:<br />
• 16GB of encrypted storage to securely store<br />
passwords and files and quickly access on-the-go<br />
• Voice search – As the device can store thousands<br />
of passwords, use voice search to pull up<br />
specific passwords in seconds<br />
• Bluetooth & Wi-Fi enabled – Seamlessly<br />
connect wirelessly, with auto-fill in of passwords<br />
to websites, online bank accounts and files<br />
• Uses NFC and Secure Element technology<br />
allowing it to be HID SEOS ready<br />
• USB – Plug directly into any computer for<br />
immediate access to your passwords and file folders<br />
• OLED screen display – Enter and view your<br />
30
passwords with the simple swipe of a fingerprint<br />
and click of a button<br />
• Rechargeable battery<br />
• Water resistant – Device is protected and fully<br />
functional in all environments<br />
• Apps for iOS and Android – Ensure ultimate<br />
identity security on all devices due to mobile compatibility<br />
and functionality<br />
• Software Upgradeable<br />
“As a founding member of the FIDO Alliance,<br />
we know that that secure authentication is<br />
a critical step to solving the pain point of password<br />
insecurity,” said Stewart. “FIDO standards<br />
of multi-factor authentication are the future of<br />
digital security and access. With IDKEY, users can<br />
own the most advanced FIDO-compliant technology<br />
designed to keep their online identities in<br />
their own hands.”<br />
For more information, please visit www.ID-<br />
KEY.com.<br />
Zwipe introduces HID Technology <br />
biometric cards for iCLASS ® and<br />
ProxCard ® Readers<br />
About Sonavation<br />
The Sonavation product line is designed to provide<br />
secure authentication and protection for digital<br />
and physical environments for consumers and<br />
businesses. Solutions include both embedded and<br />
stand-alone device offerings designed to protect<br />
physical access as well as online systems, including:<br />
eCommerce, financial services, health data<br />
and other sensitive applications.<br />
Sonavation designs and manufactures the<br />
industry’s leading biometric fingerprint sensors,<br />
utilizing ultrasound. Its 3D surface scan and subsurface<br />
technology is protected by 38 awarded<br />
patents plus over 70 additional patents filed, making<br />
it the world’s smallest low-power ultrasound<br />
sensor. Headquartered in Palm Beach Gardens,<br />
Fla., Sonavation is committed to “Empowering<br />
Trust, Delivering Peace of Mind.”<br />
For more information, please visit http://www.<br />
sonavation.com/.<br />
Oslo, Norway based Zwipe, a global leader in biometric<br />
authentication technology, has announced<br />
that HID Global’s iCLASS® and 125kHz ProxCard®<br />
users can now easily integrate the Zwipe Access<br />
biometric card, eliminating the need to add biometric<br />
readers to an existing HID Global®iClass®<br />
or Prox-based system.<br />
“As the largest smart and proximity card provider<br />
in the world, HID Global has thousands of<br />
users who would like to upgrade to biometric authorization,<br />
but may not have the budget or the resources<br />
to invest in biometric readers,” added Robert<br />
Fee, director of sales, Americas, Zwipe. “The<br />
Zwipe biometric card provides an easy, affordable<br />
option for security professionals to extend the use<br />
of their present card systems by adding biometrics<br />
for multi-factor, card-based authentication.”<br />
By providing authorized users with Zwipe<br />
Access biometric cards that interoperate with<br />
their existing iCLASS and 125 kHz ProxCard<br />
More on page 39<br />
31
Special Section: Protecting the Grid<br />
New CIP standards provide a catalyst to unite se<br />
By Mark A. Tinker, PhD<br />
32<br />
In late 2014, the Federal Energy<br />
Regulatory Commission<br />
(FERC) outlined new rules,<br />
which take effect in 2016, requiring<br />
electrical utility companies<br />
to determine the key<br />
electric transmission stations<br />
and substations that could<br />
have large scale impact on the US electrical grid.<br />
Heading into 2015, those tasked with securing<br />
the national electrical grid must proactively<br />
enhance their security posture to address these<br />
critical infrastructure protection guidelines. However,<br />
large power corporations are starting to realize<br />
it is possible to capitalize upon compliance<br />
by leveraging security investments across other<br />
departments. Enhancing security not only has<br />
the desired effect, but when done from an holistic<br />
perspective, it can actually improve operations,<br />
increase asset resilience, and improve rate payer<br />
value. In other words, security is no longer a line<br />
item in a budget, but a critical element of corporate<br />
performance.<br />
According to an article in the Wall Street<br />
Journal in November 2014, large power companies<br />
such as PG&E and Dominion Resources plan<br />
to invest hundreds of millions of dollars to alleviate<br />
current weaknesses that incidents like Metcalf<br />
exploited. Among the vulnerabilities common to<br />
electrical transmission substations were remoteness<br />
of assets, security operators lack of confidence<br />
in alerts, and the image quality from cameras,<br />
especially in darkness or difficult weather<br />
conditions.<br />
Addressing these vulnerabilities means<br />
proactively turning operator intuition into intelligence.<br />
Intelligence stems from validated alerts<br />
that lead to action, whether by operator initiative<br />
or automatically by the security system. This leads<br />
to proactive deterrence.<br />
Shift from Reaction to Deterrence<br />
Since 9/11, reaction became the dominant element<br />
of the new security paradigm. Today, while reaction<br />
is still a common and necessary requirement,<br />
a new theme is appearing, which is deterrence. It<br />
is now possible to model how modern perimeter<br />
intrusion systems can significantly increase the<br />
probability of deterrence. As utility companies<br />
strengthen their security posture, they seek to deter<br />
or delay threats before they can act. A driver<br />
for deterrence capability is having space and time<br />
available for intercession.<br />
The technologies that enable deterrence also<br />
add value to business operations and resilience.<br />
Operators can now confirm with security if they<br />
are witnessing an anomaly and if so, begin to take<br />
necessary actions.<br />
Integrated <strong>Security</strong> Enabling Defense in<br />
Depth<br />
What is most intriguing are emerging new technologies<br />
that can single-handedly do much more<br />
than ever before, yet when integrated with other
curity with operations in electrical utilities<br />
technologies or existing systems provide superior<br />
intelligence that can be integrated into operations<br />
or other non-security functions. For example, new,<br />
concealed seismic sensors are able to detect and<br />
classify complete threat profiles such as vehicle activity,<br />
pedestrian activity, gunfire, even lightning,<br />
in non-line-of-sight conditions. Validating the results<br />
with other sensors allows the security operator<br />
to confidently and quickly act, or the system<br />
automatically employ reactive measures, such as<br />
audible or visual warnings directed at the possible<br />
intruder. Even more impressive is how integrated<br />
architectures can even ascertain intent within a<br />
broad awareness zone outside the fence, all from<br />
sensors at or inside the fence line. For example, is<br />
the gunfire a legal hunter or actual threat?<br />
The North American Electric Reliability<br />
Corporation (NERC) sets out best practices for<br />
delivering early warning and opportunities for<br />
rapid response. With these new technologies, the<br />
tip of the security spear has pushed the boundary<br />
of the awareness zone farther out in distance<br />
and time. Potential threats such as gunshots can<br />
be detected and classified outside the perimeter<br />
sooner and with greater accuracy. This ability to<br />
reach beyond a perimeter, such as a fence or property<br />
line, provides a significantly increased level of<br />
situational awareness, increasing time and space<br />
in which to act.<br />
burglary incidents which often go unreported,<br />
leading utilities see the financial and operational<br />
benefit of achieving fewer intrusions, suffering<br />
fewer losses that derail safety, or reducing expensive<br />
system redundancies. Collaboration between<br />
security, IT, and operations yields reduced operational<br />
expenses and affords increased uptime. In<br />
the event of an incident, be it security or otherwise,<br />
the additional data may provide forensic information<br />
for later understanding, criminal prosecution,<br />
or system efficiency improvement.<br />
With 2016’s new rules for electrical utilities<br />
as a catalyst, there is a growing understanding<br />
among energy company leaders that increased<br />
collaboration between security and operations<br />
yields reduced operational expenses and results<br />
in increased uptime. The reaction culture remains<br />
ever important, but now we can validate our intuition<br />
and intercede as necessary, all with a high<br />
level of confidence. Leveraging the security awareness<br />
zone and the intelligence it provides is just<br />
the beginning.<br />
About Mark Tinker<br />
Mark Tinker, PhD, is the CEO of Quantum Technology<br />
Sciences, a science and engineering company<br />
delivering real-time situational awareness solutions<br />
around critical infrastructure assets to expand and<br />
enhance physical security.<br />
Collaboration between <strong>Security</strong> and Operations<br />
In light of instances such as the Metcalf attack and<br />
33
Special Section: Protecting the Grid<br />
ROMANOWICH ON SURVEILLANCE<br />
Challenges and solutions for substation security –<br />
applying smart thermal technology to prevent intrusions<br />
John Romanowich<br />
CEO, SightLogix, Inc.<br />
Protecting electrical substations<br />
presents a number<br />
of unique challenges,<br />
ranging from theft, vandalism<br />
and safety concerns to complying with increasingly<br />
enforced regulations from the National<br />
Electrical Reliability Commission’s (NERC) Critical<br />
Infrastructure Protection (CIP) program.<br />
Despite the threat of terrorist activity to<br />
disrupt the nation’s power grid, theft of valuable<br />
copper and vandalism are more common. Substation<br />
owners have taken some precautions, such as<br />
painting or marking wiring, to alert scrap yards<br />
that copper has been stolen, but that has not<br />
stopped thieves from breaking in, often with serious<br />
consequences. The risk of injuries and even<br />
loss of life brings new liabilities above and beyond<br />
disrupted electrical service. Maintenance personnel<br />
have been severely injured or killed in the process<br />
of performing regular maintenance due to<br />
the destabilization of elements of the power grid<br />
caused by copper theft.<br />
In light of these and other concerns, the Federal<br />
Energy Regulatory Commission (FERC) has<br />
worked together with NERC to put additional<br />
safeguards in place for physical security around<br />
these assets and to prevent cascading consequences.<br />
This partnership has led to the strengthening<br />
of NERC’s critical infrastructure protection (CIP)<br />
standards. As CIP standards move toward mandates,<br />
utilities will be required to deploy security<br />
equipment to comply with regulations, or face<br />
fines and other measures for non-compliance.<br />
To assure the physical security of potentially<br />
vulnerable substations, CIP standards require<br />
protection on all six sides of assets; the four surrounding<br />
sides plus above and below. To meet this<br />
requirement, conventional wisdom has been to<br />
use video surveillance cameras, but there are limitations<br />
to what video surveillance can do. What is<br />
really needed is a security modality that can detect<br />
intruders as soon as they threaten a secured area.<br />
Real-time awareness when an intrusion is taking<br />
place is critical to ensuring a timely response and<br />
preventing an incident from escalating.<br />
Real-time awareness is where automated solutions<br />
excel. These smart systems never tire, cover<br />
wide areas, and see what the human eye would<br />
miss, while delivering immediate, actionable information<br />
to help security staff make fast response<br />
decisions.<br />
Reliable accuracy is the key to success with<br />
34
smart outdoor security systems. When alerts are<br />
unreliable, responders lose confidence in the system<br />
and resources are wasted on false alarms.<br />
Historically, blind sensors, such as fiber on fence<br />
lines, were used to detect activity. The drawbacks<br />
to that approach are that these sensors generate<br />
many nuisance alerts, diminishing reliability, and<br />
incurring an additional cost of either a confirming<br />
camera system or a physical confirmation by<br />
a guard.<br />
Thermal cameras with video analytics – also<br />
known as “smart” thermal cameras - provide substantial<br />
advantages. They increase the probability<br />
of intruder detection while greatly reducing the<br />
nuisance alarms that have plagued automated<br />
perimeter systems in the past. They also detect<br />
break-ins as they occur to better thwart an intruder<br />
in real time, while providing enough detail to<br />
determine the “what and where” of an alert without<br />
additional verification systems.<br />
Smart thermal cameras accurately and reliably<br />
detect intruders in conditions when visible<br />
light cameras will fail. Thermal cameras ignore<br />
headlights, reflections off water, and other lighting<br />
issues that cause false detections with visible<br />
light cameras. Because they can detect in complete<br />
darkness, bright sunlight, or poor weather,<br />
smart thermal cameras are a 24/7 outdoor detection<br />
solution. Combining manpower, automation<br />
and smart thermal systems will deliver reliable,<br />
real-time security and meet federal physical security<br />
mandates.<br />
In terms of system design, the historic focus<br />
for securing critical assets such as substations<br />
has been on perimeter security. The capabilities<br />
of smart thermal cameras can provide additional<br />
advantages and new operational modes. For example,<br />
they can be used to create virtual barriers<br />
outside a perimeter fence or along open areas that<br />
surround a building or any specific asset. These<br />
virtual barriers can alert officials to real time activity<br />
for review, and can provide alerts when someone<br />
is about to enter an area – before they had an<br />
opportunity to steal, vandalize or disrupt substation<br />
operations. Within a facility, such alerts could<br />
prevent insider theft where physical barriers don’t<br />
exist. Smart video can be used to create a security<br />
“buffer zone” around areas of special concern to<br />
control access based on time of day or other criteria,<br />
mitigating possible sabotage or theft from<br />
insiders.<br />
When it comes to protecting critical assets,<br />
real-time awareness of an intrusion is critical.<br />
Real-time awareness is the key to ensuring a<br />
timely response and preventing theft, vandalism,<br />
and other potentially dangerous events that could<br />
disrupt power grid stability – while also meeting<br />
increasingly enforced security regulations.<br />
35
Special Section: Protecting the Grid<br />
Utah-Based Washakie Renewable Energy, LLC<br />
WASHINGTON, March 19 – The U.S. Environmental<br />
Protection Agency (EPA) and the U.S. Department<br />
of Justice (DOJ) today announced a<br />
settlement with Utah-based Washakie<br />
Renewable Energy, LLC, that resolves<br />
allegations that the company<br />
generated more than<br />
7.2 million invalid renewable<br />
fuel credits worth<br />
more than $2 million.<br />
From January<br />
to October of 2010,<br />
Washakie generated<br />
more than 7.2 million<br />
Renewable Identification<br />
Numbers,<br />
or RINs, and reported<br />
to EPA that it produced<br />
biodiesel associated with<br />
those RINs at its Plymouth,<br />
Utah facility. During that time,<br />
however, Washakie did not produce<br />
any biodiesel at the Plymouth<br />
facility. The biodiesel associated with the 7.2<br />
million RINs would have accounted for a reduction<br />
of emissions equivalent to more than 30,000<br />
metric tons of carbon dioxide. Washakie has purchased<br />
and retired from the market an equivalent<br />
number of RINs, which achieved this reduction of<br />
emissions.<br />
36<br />
Renewable fuel producers and importers<br />
generate RINs for each gallon of renewable fuel in<br />
the U.S. market that meets greenhouse gas<br />
emissions reduction standards established<br />
under the Renewable<br />
Fuel Standard. Washakie<br />
will pay a $3 million penalty<br />
under the settlement,<br />
which was<br />
lodged today in the<br />
U.S. District Court<br />
for the District of<br />
Columbia.<br />
“This case is<br />
another example of<br />
EPA’s commitment<br />
to maintain the integrity<br />
of the Renewable<br />
Fuel Standard program,”<br />
said Cynthia Giles,<br />
EPA Assistant Administrator<br />
for Enforcement and Compliance<br />
Assurance. “Making sure<br />
producers are supporting their claims<br />
with production of actual renewable fuels is critical<br />
to reducing greenhouse gas emissions that are<br />
fueling climate change.”<br />
“The defendant made quite a profit by failing<br />
to adhere to the requirements of the Renewable<br />
Fuel Program regulations,” said Assistant At-
settles renewable fuel standard violations<br />
torney General Cruden. “The penalty here sends<br />
the message that renewable fuel producers will<br />
be held accountable for meeting all legal requirements.<br />
The Department of Justice remains committed<br />
to taking the profit out of illegal activity.”<br />
This is the first case under the second Renewable<br />
Fuels Standards in which, as a part of a<br />
settlement, EPA secured the replacement of invalid<br />
RINs by the producer of those RINs. Because<br />
Washakie purchased and retired an equal amount<br />
of RINs to the number identified as invalid and<br />
used for compliance purposes, EPA does not plan<br />
to request that the obligated parties who used the<br />
invalid RINs replace them. This reduces the burden<br />
on the parties that purchased and used the<br />
RINs for compliance purposes.<br />
EPA initially discovered these violations<br />
during an EPA inspection of the Washakie facility<br />
in Plymouth, Utah in 2010, and uncovered additional<br />
information concerning the violations in<br />
Washakie’s response to information requests and<br />
additional investigative work by the agency.<br />
EPA is responsible for developing and implementing<br />
regulations to ensure that transportation<br />
fuel sold in the United States contains a minimum<br />
volume of renewable fuel. The Renewable Fuel<br />
Standard program – created under the Energy<br />
Policy Act of 2005 – was developed in collaboration<br />
with refiners, renewable fuel producers, and<br />
many other stakeholders. It was expanded and<br />
37<br />
strengthened under the Energy Independence and<br />
<strong>Security</strong> Act of 2007, which was designed to encourage<br />
the blending of renewable fuels into our<br />
nation’s motor vehicle fuel supply, and reduce the<br />
nation’s dependence on foreign oil, help grow the<br />
nation’s renewable energy industry, and achieve<br />
greenhouse gas reductions.<br />
To read the settlement, or for more information<br />
about the case, visit: To read the settlement,<br />
or for more information about the case, visit:<br />
http://www2.epa.gov/enforcement/washakie-renewable-energy-llc-clean-air-act-settlement.<br />
For more information on the Renewable Fuel<br />
Standards, visit: http://www.epa.gov/oms/fuels/<br />
renewablefuels/
Special Section: Protecting the Grid<br />
Excerpts from Chuck Brooks 2014 radio interview<br />
on the Dick Morris Show<br />
Dick Morris: Tell us what’s going on with<br />
the Grid, Chuck<br />
Chuck Brooks: It’s a monumental issue.<br />
Nobody is paying attention to the electrical grid<br />
even though we all depend upon it. Most of the<br />
grid was built in the 1950s, It’s vulnerable not only<br />
to terrorist incidents, but also from being old.<br />
Most of the telephone lines and circuit breakers<br />
are over 30 years old. Yet energy usage has increased<br />
almost 60% since the 70’s. It’s an $860 billion<br />
industry involving 70,000 transformer power<br />
stations, with 70% of the transmission lines 25<br />
years old or more and 60% of the circuit breakers<br />
over 30 years old.<br />
On the subject of Cyber/SCADA, aka “Supervisory<br />
Control and Data Acquisition”, a new<br />
Ponemon study has revealed that 67 percent of<br />
critical infrastructure providers reporting falling<br />
victim to at least one security breach in the last<br />
twelve months, causing<br />
disruption of operation<br />
or loss of sensitive information.<br />
“Breaches in a<br />
cyber-way”, Brooks responded<br />
to another<br />
question from Morris<br />
asking “What kind of<br />
Breaches”.<br />
But terrorist activites<br />
are only one of<br />
38<br />
the threats, said Brooks.<br />
There are cyber threats<br />
involving malware that<br />
can cause Denial of<br />
Service aimed at master<br />
stations and control<br />
centers, and blackouts<br />
can be caused by human<br />
error… But the biggest<br />
threats of all are weather threats, ranging from<br />
lightning to geomagnetic storms – such as the<br />
Carrington Event of 1859 and the Railroad Storm<br />
of 1921 – and solar flares. A solar geo-storm that<br />
sends an electric wave, a “flare from the sun”, could<br />
take out 90% of our infrastructure. And there have<br />
been terrible solar geo-storms in the past. But we<br />
weren’s as connected then<br />
Morris: So what are the solutions?<br />
Brooks: It’s a combination of solutions.<br />
Incredibly, there are few facilities that even have<br />
guards, despite the fact that the grid is an $860-billion<br />
industry that generates enormous profits for<br />
90% of the facilities that are privately owned. The<br />
combination of solutions includes guards for the<br />
facilities, sharing of information between electrical<br />
power companies and hardening the “targets”<br />
for surge protection, because the biggest threat is<br />
the voltage surge threat. The targets would also<br />
protect citizens from solar flares or geo-magnetic<br />
storms.<br />
Morris: And what is the government doing
Zwipe introduces HID Technology biometric<br />
cards for iCLASS® and ProxCard® Readers<br />
Continued from page 31<br />
these organizations can now benefit from the leading<br />
edge biometric authorization technology by<br />
simply incorporating the card into their existing<br />
systems in the same way they already incorporate<br />
proximity or HID Global smart cards. The Zwipe<br />
solution enables customers to extend the life of<br />
their existing infrastructure while simultaneously<br />
increasing its security.<br />
With Zwipe’s patented on-card authentication<br />
technology, only the authorized cardholder<br />
can activate card communication with the reader.<br />
This means no more lending or borrowing of ID<br />
badges to access buildings, university labs, hospital<br />
pharmacies, data centers or networks. By upgrading<br />
the authentication from something they carry<br />
(a card) to something they are (a fingerprint), the<br />
issues associated with a lost or stolen credential<br />
are dramatically reduced.<br />
The problems associated with PINs and passwords<br />
are eliminated through the use of Zwipe’s<br />
biometric authentication technology. The on-card<br />
fingerprint scanner with 3D capacitive technology<br />
resides on the contactless smart card that utilizes<br />
an embedded HID Global 13.56MHz iCLASS or<br />
125kHz Proximity transponder. The Zwipe biometric<br />
card is also compatible with MIFARE Classic<br />
and DESFIRE EV1.<br />
By incorporating Zwipe’s biometric solution<br />
to access control, organizations can increase<br />
the security of their systems, their employees and<br />
their assets by changing the authentication from<br />
something you carry to something you are without<br />
any modification to their existing infrastructure.<br />
About Zwipe<br />
Starting in 2009, Zwipe challenged the status quo<br />
of identity verification by replacing PINs and<br />
passwords with fingerprint authentication. After<br />
developing the leanest, fastest, and most power efficient<br />
fingerprint algorithm in the world, Zwipe<br />
continued disrupting the industry through its patented<br />
energy harvesting technology. No longer<br />
dependent on batteries, Zwipe fingerprint readers<br />
harvest the energy needed from already existing<br />
access, transport, border control and financial infrastructures.<br />
With its already strong portfolio of<br />
patent applications, Zwipe continues to develop<br />
and refine its innovative technology. For more information,<br />
visit www.zwipe.com or follow them on<br />
Twitter@Zwipe.<br />
to encourage responsible actions and investments<br />
by the electric power plant operators?<br />
Brooks: With the Critical Infrastructure<br />
Protection Act of Representative Trent Franks<br />
HR3410, Congress is now establishing standards<br />
that business has to follow. The needs are for:<br />
• Collecting and sharing information<br />
39<br />
• Hardening of targets to provide grid protection<br />
by protecting against surges and voltage<br />
• Storage and automated self-healing<br />
• Mandatory security standards<br />
• Training and contingency planning<br />
It would not be too expensive to harden the facilities.<br />
It’s an $860 billion industry.
Iris ID to enhance Canada Border Service<br />
Continued from page 29<br />
said, “We are excited to work with IBM to make<br />
the enhancements to the NEXUS program. Iris<br />
ID’s iCAM 7 Series and IrisAccelerator backend<br />
matching engine are integral parts of the changes<br />
to the Nexus program. Koo added, “A similar system<br />
is also being used by Canadian Air Transport<br />
<strong>Security</strong> Authority (CATSA) across 29 major international<br />
airports in Canada for employee identity<br />
management and access control.”<br />
The iris-scanning systems enable the validation<br />
of the iris-scanning camera, reads the Nexus<br />
card, and prints a receipt and other functions.<br />
“IBM is always looking for innovative ways<br />
to improve the lives of Canadians so boosting security<br />
and reducing time spent in lines at border<br />
crossings is something we’re proud to be part of,”<br />
said John Fursey, VP and Partner Public Sector<br />
Leader Canada. “<br />
Iris recognition is a superior verification process<br />
because a picture of the human iris provides<br />
measurement unparalleled by other methods. The<br />
unique pattern in the human iris is formed by 10<br />
months of age and remains unchanged throughout<br />
one’s lifetime. The probability of two irises<br />
producing the same code is nearly impossible and<br />
the technology is easily integrated into existing<br />
security systems or can operate alone. A distinctive<br />
iris pattern is not susceptible to theft, loss or<br />
compromise and it is non-invasive. Unlike other<br />
biometric technologies, iris recognition is noncontact<br />
and quick, offering unmatched accuracy<br />
when compared to any other security alternative,<br />
from distances as far as six inches to one meter<br />
from the eye.<br />
With the enhancements pre-screened, frequent<br />
travelers can be identified quickly and allow<br />
enforcement activities to be focused on high-risk<br />
travelers. For more information about the Nexus<br />
program please visit http://www.cbsa-asfc.gc.ca/<br />
prog/nexus/menu-eng.html. For more information<br />
about IrisID visit: http://www.irisid.com/irisrecognitiontechnology<br />
About Iris ID Systems<br />
Iris ID Systems, Inc, formerly a division of LG<br />
Electronics USA known as LG Iris, has been active<br />
in iris recognition research, development and production<br />
since 1997. Today, U.S. based Iris ID Systems<br />
in a proven global leader in the Iris recognition<br />
market. IrisAccess® is the world’s most widely<br />
deployed Iris recognition platform, used in thousands<br />
of locations authenticating the identities of<br />
millions of people. More people look to IrisAccess<br />
for iris- and face-based authentication than to all<br />
other iris recognition products combined. To find<br />
out more about Iris ID visit www.irisid.com.<br />
For IrisID, Wendy Kwan, Customer Service<br />
Office: +1-609-819-IRIS (4747), wkwan@irisid.<br />
com<br />
40
GSN Interviews Louis R. Hughes<br />
Continued from page 19<br />
came through personal use, but I<br />
am saying, get rid of the risk of<br />
personal use. Why not?<br />
GSN: Is WorkPlay Technology<br />
easy to implement?<br />
LH: Yes. It’s a core technology<br />
you can adapt to any ARM<br />
device, which in the mobile<br />
world are very common. But I<br />
think the more telling answer is,<br />
our core technology is small, just<br />
several thousand lines of code.<br />
That’s not much when you look<br />
at the size of other containerization<br />
methods. This is important<br />
because the code is pretty easy<br />
to evaluate, modify and support.<br />
The underlying technology was<br />
validated for us by a NIST-certifying<br />
lab, Cygnacom. So it is not a<br />
large or long exercise to fit it into<br />
the majority of existing hardware<br />
platforms.<br />
GSN: What about cost?<br />
LH: We expect to make it<br />
quite inexpensive to the user customer<br />
- - imagine dividing your<br />
tablet into a Work tablet and a<br />
Play tablet, for just a few extra<br />
dollars.<br />
GSN: How do you plan to<br />
get it implemented?<br />
LH: We work with chip<br />
makers, OEMs and large customers<br />
who want it, like the government,<br />
or should want it. We can<br />
integrate it into existing devices<br />
in the field or new production<br />
devices. It’s just a simple way of<br />
eliminating a dilemma between<br />
using a device for business and<br />
personal use, or any other reason<br />
for separating data, like between<br />
classified and unclassified information.<br />
And when it is implemented<br />
there’s no downside to<br />
the user, there are just two real<br />
devices in one. Our view is, why<br />
not if you can?<br />
GSN: Has the marketplace<br />
had a chance to evaluate and respond?<br />
LH: We’ve both proven and<br />
demonstrated WorkPlay Technology’s<br />
validity, effectiveness<br />
and ease of use to our potential<br />
partner-customers. We have<br />
agencies, chip makers, OEMs and<br />
large cyber technology providers<br />
we are in various degrees of serious<br />
discussion with right now.<br />
Each of these has its own needs<br />
and wants, and our mission is to<br />
make it easy and satisfy them. It<br />
is important to make it as easy<br />
as possible for the end users, especially<br />
government and critical<br />
41<br />
enterprises, to seamlessly be able<br />
to benefit from WorkPlay Technology<br />
to, as I said, eliminate half<br />
the problem.<br />
GSN: Thanks, Lou. If the<br />
old saying is true that “All work<br />
and no play makes Jack a dull<br />
boy,” it looks like you may have<br />
found a solution for a lot of potential<br />
workaholics.<br />
Louis R. Hughes is the former<br />
President of Lockheed Martin and<br />
General Motors International Operations,<br />
a current member of the<br />
Board of Directors of several large<br />
multinational companies including<br />
Alcatel-Lucent and ABB, and<br />
served as State Department Chief<br />
of Staff for Afghanistan Reconstruction.<br />
Now, he also serves as<br />
Chairman of a local R&D firm,<br />
InZero Systems, specializing in<br />
embedded computer security<br />
technology. InZero has developed<br />
“WorkPlay Technology” for mobile<br />
devices and laptop/desktops.<br />
Contact: InZero Systems ,13755<br />
Sunrise Valley Drive, Suite 750,<br />
Herndon, VA 20171, Email:<br />
info@workplaytablet.com, Phone:<br />
703-636-2048, www.workplaytablet.com/.
International training essential to<br />
global stability and security<br />
Continued from page 26<br />
close striking distance. And if<br />
viable threats do exist, nations<br />
with autonomous capability can<br />
contain them without U.S. assistance<br />
in most cases. Finally,<br />
in the extreme cases where a local<br />
or regional threat is not easily<br />
contained with indigenous forces,<br />
threatened partner nations<br />
can function inter-operably with<br />
U.S. and/or other friendly foreign<br />
forces to most effectively neutralize<br />
menaces to stability.<br />
We are currently seeing a<br />
shift to more U.S. defense contractors<br />
performing and/or providing<br />
support to security assistance<br />
missions utilizing an<br />
extremely capable cohort of<br />
largely former military personnel.<br />
This U.S. veteran workforce<br />
combined with highly motivated<br />
private sector individuals is ensuring<br />
critical missions continue<br />
to successfully train and better<br />
prepare foreign military partners<br />
for self-defense and/or coalition<br />
participation.<br />
The U.S. will always play an<br />
important role in international<br />
stability and the future will rely<br />
more and more on the strength<br />
and capability of our partners.<br />
Increasing the capability of our<br />
partners through security assistance<br />
training is the most effective<br />
solution to mitigate the U.S. military<br />
drawdown<br />
while preserving<br />
regional and<br />
global security.<br />
We simply can’t<br />
afford not to!<br />
Scott Seavers, former USAF Colonel<br />
and Air Force <strong>Security</strong> Assistance<br />
Training Commander, is a<br />
Vice President at Salient Federal<br />
Solutions in Fairfax, Virginia.<br />
U.S./Canada sign preclearance<br />
agreement<br />
Continued from page 5<br />
by which CBP Officers stationed<br />
abroad screen and make admissibility<br />
decisions about passengers<br />
and their accompanying goods<br />
or baggage heading to the United<br />
States before they leave a foreign<br />
port. CBP officers do, however,<br />
42<br />
retain the authority to inspect<br />
passengers and their accompanying<br />
goods or baggage after<br />
arriving in the United States.<br />
CBP officers currently conduct<br />
preclearance operations at eight<br />
Canadian airports: Calgary, Edmonton,<br />
Halifax, Montreal, Ottawa,<br />
Toronto, Vancouver and<br />
Winnipeg.<br />
This agreement achieves a<br />
key component of the Beyond<br />
the Border: A Shared Vision for<br />
Perimeter <strong>Security</strong> and Economic<br />
Competitiveness Action<br />
Plan. On February 4, 2011, President<br />
Obama and Prime Minister<br />
Harper released the Beyond the<br />
Border Declaration, articulating a<br />
shared vision in which our countries<br />
work together to address<br />
threats at the earliest point possible<br />
while facilitating the legitimate<br />
movement of people, goods<br />
and services across our shared<br />
border. The Action Plan outlines<br />
the specific steps our countries<br />
intend to take to achieve the security<br />
and economic competitiveness<br />
goals outlined in the Beyond<br />
the Border Declaration.<br />
For more information, visit<br />
www.dhs.gov.
2015 Airport/Seaport/Border <strong>Security</strong> Awards<br />
Now Accepting Entries!<br />
<strong>Government</strong> <strong>Security</strong> <strong>News</strong> would like to take this opportunity to invite all Technology<br />
Vendors, Airport, Seaport and Border <strong>Security</strong> Officers, Executives and <strong>Security</strong> Teams<br />
to visit the GSN 2015 Awards website at www.asbsecurityawards.com, review the<br />
37 updated entry categories, and if you find one or more of them that fits your company<br />
or agency, go for the gold!<br />
And we mean that literally, because all winners will<br />
receive a handsome, gold-trimmed plaque that you<br />
can post in your office or other prominent position,<br />
and all Winners and Finalists will be invited to post<br />
their winning entries and additional information in our 2015 Yearbook of Airport,<br />
Seaport, Border <strong>Security</strong> Awards Recipients.<br />
It’s great publicity and exposure in <strong>Government</strong> <strong>Security</strong> <strong>News</strong>, which is sure to be further<br />
enhanced by Google and the other Search engines and Social Media. Check out<br />
the many new categories in the 2015 entry categories and be sure to see the kind of<br />
distinguished company you’ll be in as a Winner or Finalist by looking through our 2014<br />
Yearbook of Airport, Seaport, Border <strong>Security</strong> Awards at:<br />
http://www.gsnmagazine.com/2014ASB<strong>Security</strong>Yearbook.<br />
43
Coming Attractions<br />
March – May 2015<br />
March Print Edition<br />
Technology Focus:<br />
Market Focus:<br />
Cybersecurity/Closing the Gap<br />
Maritime/Port <strong>Security</strong><br />
April Digital Edition<br />
Technology Focus:<br />
Market Focus:<br />
Video Surveillance/Analytics<br />
Video Management Software<br />
Border <strong>Security</strong>/Immigration<br />
May Print Edition<br />
Technology Focus:<br />
Market Focus:<br />
Satellite Communications<br />
Oil/Gas/Electric/Nuclear Monitoring<br />
For GSN Media Kit<br />
or Advertising Rates<br />
Contact Publisher<br />
Mike Madsen at<br />
732-233-8119<br />
or by email at<br />
mmadsen@gsnmagazine.com<br />
44
The <strong>News</strong> Leader in Physical, IT and Homeland <strong>Security</strong><br />
Publisher:<br />
Michael Madsen<br />
(O) 212-344-0759, X1<br />
(C) 732-233-8119<br />
mmadsen@gsnmagazine.com<br />
Executive Editor:<br />
John Wagley<br />
(O) 212-344-0759, X2<br />
(C) 202-425-0196<br />
wagley.jr@gmail.com<br />
Senior Writer:<br />
Lorrie Barclay<br />
(O) 212-344-0759, X5<br />
(C) 508-685-0652<br />
lorriebarclay@gmail.com<br />
Columnist:<br />
John Convy<br />
Convy on Netcentric <strong>Security</strong><br />
john@convyassociates.com<br />
Columnist:<br />
John Romanowich<br />
Romanowich on Video Surveillance<br />
jromanowich@sightloxic.com<br />
Guest Expert Contributor:<br />
Denise Rucker Krepp<br />
(C) 202-546-2533<br />
kdrkrepp@hotmail.com<br />
Art Director:<br />
Gerry O’Hara<br />
OHDesign3<br />
(C) 203-249-0626<br />
gerry@ohd3.com<br />
Production/Design Specialist:<br />
Brenden Hitt<br />
(C) 315-723-6203<br />
brenden@ihitt.com<br />
Editorial Director/CEO:<br />
Adrian Courtenay<br />
(O) 212-344-0759, X3<br />
(C) 917-696-5782<br />
acourtenay@gsnmagazine.com<br />
Mailing Address:<br />
<strong>Government</strong> <strong>Security</strong> <strong>News</strong><br />
P.O. Box 7608<br />
Greenwich, CT 06836<br />
<strong>Government</strong> <strong>Security</strong> <strong>News</strong> (ISSN 1548-940X and UPS 022-845) is published in six print editions (Jan, Mar, May, Jul, Sep, Nov) and<br />
six digital editions (Feb, Apr, Jun, Aug, Oct, Dec) per year by World Business Media, LLC, P.O. Box 7608, Greenwich, CT 06836.<br />
Telephone (212) 344-0759. Periodicals postage paid at New York, NY and additional mailing offices. POSTMASTER: Send address<br />
changes to GSN: <strong>Government</strong> <strong>Security</strong> <strong>News</strong>, Subscription Department, P.O. Box 316, Congers, NY 10920-0316. For <strong>Government</strong><br />
decision makers and business executives involved with security products, systems and series. Qualified U.S. subscribers received<br />
GSN: <strong>Government</strong> <strong>Security</strong> <strong>News</strong> at no charge. Non-qualified subscribers in the U.S. are charged $75.00 per year. Canadian and<br />
foreign subscribers are charged $140 International Airmail. Copyright 2015 by GSN: <strong>Government</strong> <strong>Security</strong> <strong>News</strong>. All rights reserved.<br />
Printed in the U.S.A. GSN: <strong>Government</strong> <strong>Security</strong> <strong>News</strong> assumes resonsibility for validity of claims in items reported.<br />
45
Secure access<br />
to cloud, data<br />
and door<br />
Go beyond simple passwords. Protect your<br />
organisation with cost-effective, risk appropriate<br />
Identity Assurance Solutions from HID Global.<br />
With the ever increasing risk from advanced IT security threats, organisations are looking to take authentication<br />
beyond passwords, while lowering cost at the same time. HID Global’s authentication solution provides you<br />
with the convenience, flexibility and comprehensive control you need to deliver secure access, without<br />
compromising on security. HID Global can empower your employee’s, partners and customers with anytime,<br />
anywhere access to enterprise cloud applications, data and the door.<br />
Experience authentication beyond passwords. hidglobal.com<br />
© 2015 HID Global Corporation/ASSA ABLOY AB. All rights reserved. HID, HID Global, the HID Blue Brick logo, and the Chain Design are trademarks or registered trademarks of HID Global or its<br />
licensor(s)/supplier(s) in the US and other countries and may not be used without permission.