IMSI Catchers and Mobile Security
EAS499Honors-IMSICatchersandMobileSecurity-V18F-1
EAS499Honors-IMSICatchersandMobileSecurity-V18F-1
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
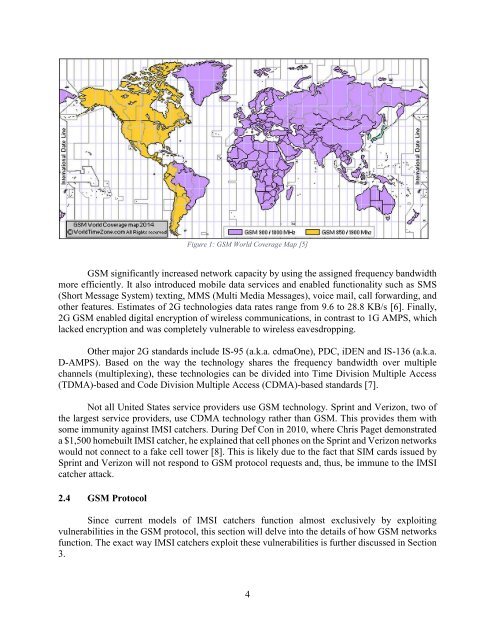
Figure 1: GSM World Coverage Map [5]<br />
GSM significantly increased network capacity by using the assigned frequency b<strong>and</strong>width<br />
more efficiently. It also introduced mobile data services <strong>and</strong> enabled functionality such as SMS<br />
(Short Message System) texting, MMS (Multi Media Messages), voice mail, call forwarding, <strong>and</strong><br />
other features. Estimates of 2G technologies data rates range from 9.6 to 28.8 KB/s [6]. Finally,<br />
2G GSM enabled digital encryption of wireless communications, in contrast to 1G AMPS, which<br />
lacked encryption <strong>and</strong> was completely vulnerable to wireless eavesdropping.<br />
Other major 2G st<strong>and</strong>ards include IS-95 (a.k.a. cdmaOne), PDC, iDEN <strong>and</strong> IS-136 (a.k.a.<br />
D-AMPS). Based on the way the technology shares the frequency b<strong>and</strong>width over multiple<br />
channels (multiplexing), these technologies can be divided into Time Division Multiple Access<br />
(TDMA)-based <strong>and</strong> Code Division Multiple Access (CDMA)-based st<strong>and</strong>ards [7].<br />
Not all United States service providers use GSM technology. Sprint <strong>and</strong> Verizon, two of<br />
the largest service providers, use CDMA technology rather than GSM. This provides them with<br />
some immunity against <strong>IMSI</strong> catchers. During Def Con in 2010, where Chris Paget demonstrated<br />
a $1,500 homebuilt <strong>IMSI</strong> catcher, he explained that cell phones on the Sprint <strong>and</strong> Verizon networks<br />
would not connect to a fake cell tower [8]. This is likely due to the fact that SIM cards issued by<br />
Sprint <strong>and</strong> Verizon will not respond to GSM protocol requests <strong>and</strong>, thus, be immune to the <strong>IMSI</strong><br />
catcher attack.<br />
2.4 GSM Protocol<br />
Since current models of <strong>IMSI</strong> catchers function almost exclusively by exploiting<br />
vulnerabilities in the GSM protocol, this section will delve into the details of how GSM networks<br />
function. The exact way <strong>IMSI</strong> catchers exploit these vulnerabilities is further discussed in Section<br />
3.<br />
4