Rooting Every Android From extension to exploitation
eu-16-Shen-Rooting-Every-Android-From-Extension-To-Exploitation
eu-16-Shen-Rooting-Every-Android-From-Extension-To-Exploitation
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
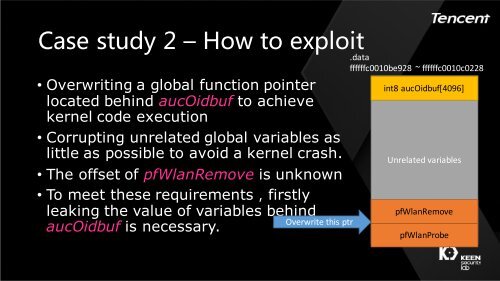
Case study 2 – How <strong>to</strong> exploit<br />
• Overwriting a global function pointer<br />
located behind aucOidbuf <strong>to</strong> achieve<br />
kernel code execution<br />
• Corrupting unrelated global variables as<br />
little as possible <strong>to</strong> avoid a kernel crash.<br />
• The offset of pfWlanRemove is unknown<br />
• To meet these requirements,firstly<br />
leaking the value of variables behind<br />
aucOidbuf is necessary.<br />
Overwrite this ptr<br />
.data<br />
ffffffc0010be928 ~ ffffffc0010c0228<br />
int8 aucOidbuf[4096]<br />
Unrelated variables<br />
pfWlanRemove<br />
pfWlanProbe