Corruption de la mémoire lors de l'exploitation - Sstic
Corruption de la mémoire lors de l'exploitation - Sstic
Corruption de la mémoire lors de l'exploitation - Sstic
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
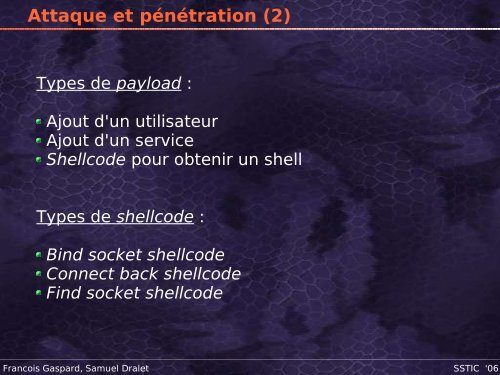
Attaque et pénétration (2)<br />
Types <strong>de</strong> payload :<br />
Ajout d'un utilisateur<br />
Ajout d'un service<br />
Shellco<strong>de</strong> pour obtenir un shell<br />
Types <strong>de</strong> shellco<strong>de</strong> :<br />
Bind socket shellco<strong>de</strong><br />
Connect back shellco<strong>de</strong><br />
Find socket shellco<strong>de</strong><br />
Francois Gaspard, Samuel Dralet SSTIC '06