Panduan Penerapan Tata Kelola Keamanan Informasi bagi ...
Panduan Penerapan Tata Kelola Keamanan Informasi bagi ...
Panduan Penerapan Tata Kelola Keamanan Informasi bagi ...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
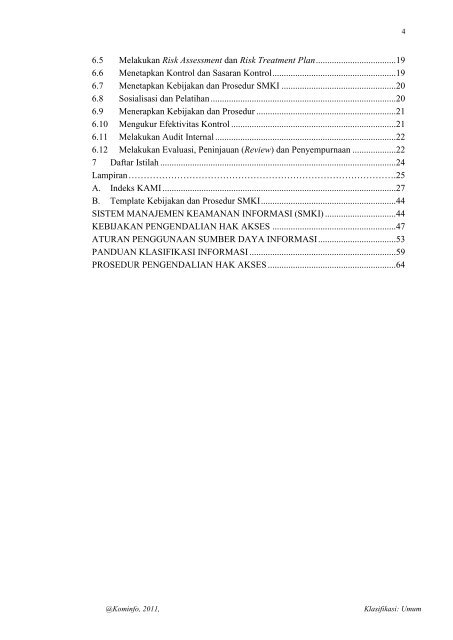
46.5 Melakukan Risk Assessment dan Risk Treatment Plan ................................... 196.6 Menetapkan Kontrol dan Sasaran Kontrol ...................................................... 196.7 Menetapkan Kebijakan dan Prosedur SMKI .................................................. 206.8 Sosialisasi dan Pelatihan ................................................................................. 206.9 Menerapkan Kebijakan dan Prosedur ............................................................. 216.10 Mengukur Efektivitas Kontrol ........................................................................ 216.11 Melakukan Audit Internal ............................................................................... 226.12 Melakukan Evaluasi, Peninjauan (Review) dan Penyempurnaan ................... 227 Daftar Istilah ....................................................................................................... 24Lampiran …………………………………………………………………………….25A. Indeks KAMI ...................................................................................................... 27B. Template Kebijakan dan Prosedur SMKI ........................................................... 44SISTEM MANAJEMEN KEAMANAN INFORMASI (SMKI) ............................... 44KEBIJAKAN PENGENDALIAN HAK AKSES ...................................................... 47ATURAN PENGGUNAAN SUMBER DAYA INFORMASI .................................. 53PANDUAN KLASIFIKASI INFORMASI ................................................................ 59PROSEDUR PENGENDALIAN HAK AKSES ........................................................ 64@Kominfo, 2011,Klasifikasi: Umum



![Materi I_2011 [Compatibility Mode]](https://img.yumpu.com/50071358/1/190x245/materi-i-2011-compatibility-mode.jpg?quality=85)