Lutte Anti-Virus Limites des techniques de détection et d ... - OSSIR
Lutte Anti-Virus Limites des techniques de détection et d ... - OSSIR
Lutte Anti-Virus Limites des techniques de détection et d ... - OSSIR
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
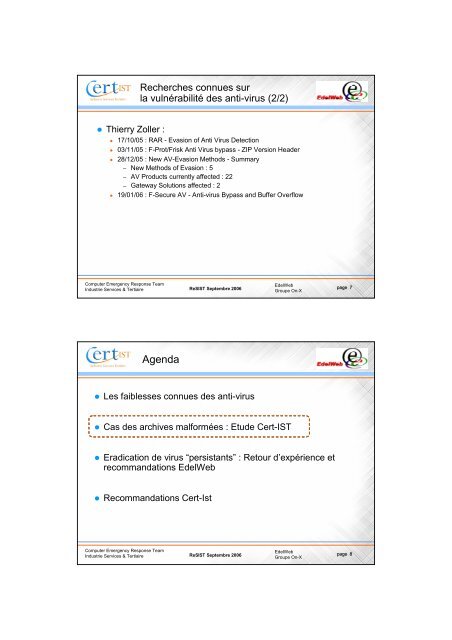
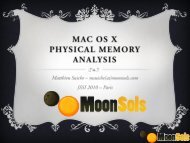
Recherches connues surla vulnérabilité <strong><strong>de</strong>s</strong> anti-virus (2/2) Thierry Zoller :17/10/05 : RAR - Evasion of <strong>Anti</strong> <strong>Virus</strong> D<strong>et</strong>ection03/11/05 : F-Prot/Frisk <strong>Anti</strong> <strong>Virus</strong> bypass - ZIP Version Hea<strong>de</strong>r28/12/05 : New AV-Evasion M<strong>et</strong>hods - Summary– New M<strong>et</strong>hods of Evasion : 5– AV Products currently affected : 22– Gateway Solutions affected : 219/01/06 : F-Secure AV - <strong>Anti</strong>-virus Bypass and Buffer OverflowComputer Emergency Response TeamIndustrie Services & TertiaireReSIST Septembre 2006E<strong>de</strong>lWebGroupe On-Xpage 7Agenda Les faiblesses connues <strong><strong>de</strong>s</strong> anti-virus Cas <strong><strong>de</strong>s</strong> archives malformées : Etu<strong>de</strong> Cert-IST Eradication <strong>de</strong> virus “persistants” : R<strong>et</strong>our d’expérience <strong>et</strong>recommandations E<strong>de</strong>lWeb Recommandations Cert-IstComputer Emergency Response TeamIndustrie Services & TertiaireReSIST Septembre 2006E<strong>de</strong>lWebGroupe On-Xpage 8