Business IT - ΤΕΥΧΟΣ 37
Business IT solutions and services.
Business IT solutions and services.
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
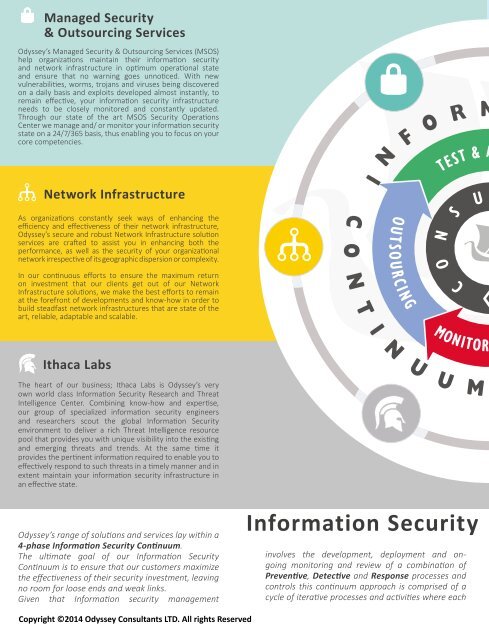
Managed Security<br />
& Outsourcing Services<br />
Odyssey’s Managed Security & Outsourcing Services (MSOS)<br />
help organizations maintain their information security<br />
and network infrastructure in optimum operational state<br />
and ensure that no warning goes unnoticed. With new<br />
vulnerabilities, worms, trojans and viruses being discovered<br />
on a daily basis and exploits developed almost instantly, to<br />
remain effective, your information security infrastructure<br />
needs to be closely monitored and constantly updated.<br />
Through our state of the art MSOS Security Operations<br />
Center we manage and/ or monitor your information security<br />
state on a 24/7/365 basis, thus enabling you to focus on your<br />
core competencies.<br />
Network Infrastructure<br />
As organizations constantly seek ways of enhancing the<br />
efficiency and effectiveness of their network infrastructure,<br />
Odyssey’s secure and robust Network Infrastructure solution<br />
s e r v i c e s a r e c r a ft e d t o a s s i s t y o u i n e n h a n c i n g b o t h t h e<br />
performance, as well as the security of your organizational<br />
network irrespective of its geographic dispersion or complexity.<br />
In our continuous efforts to ensure the maximum return<br />
on investment that our clients get out of our Network<br />
Infrastructure solutions, we make the best efforts to remain<br />
at the forefront of developments and know-how in order to<br />
build steadfast network infrastructures that are state of the<br />
art, reliable, adaptable and scalable.<br />
Ithaca Labs<br />
The heart of our business; Ithaca Labs is Odyssey’s very<br />
own world class Information Security Research and Threat<br />
Intelligence Center. Combining know-how and expertise,<br />
our group of specialized information security engineers<br />
and researchers scout the global Information Security<br />
environment to deliver a rich Threat Intelligence resource<br />
pool that provides you with unique visibility into the existing<br />
and emerging threats and trends. At the same time it<br />
provides the pertinent information required to enable you to<br />
effectively respond to such threats in a timely manner and in<br />
extent maintain your information security infrastructure in<br />
an effective state.<br />
Odyssey’s range of solutions and services lay within a<br />
4-phase Information Security Continuum.<br />
The ultimate goal of our Information Security<br />
Continuum is to ensure that our customers maximize<br />
the effectiveness of their security investment, leaving<br />
no room for loose ends and weak links.<br />
Given that Information security management<br />
Information Security<br />
involves the development, deployment and ong<br />
o i n g m o ni to r i n g a n d re vi ew of a co mb i n a ti o n of<br />
Preventive, Detective and Response processes and<br />
controls this continuum approach is comprised of a<br />
cycle of iterative processes and activities where each<br />
Copyright ©2014 Odyssey Consultants LTD. All rights Reserved