Zombie networks: An investigation into the use of anti-forensic ...
Zombie networks: An investigation into the use of anti-forensic ...
Zombie networks: An investigation into the use of anti-forensic ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
M801 Final Dissertation P6354752<br />
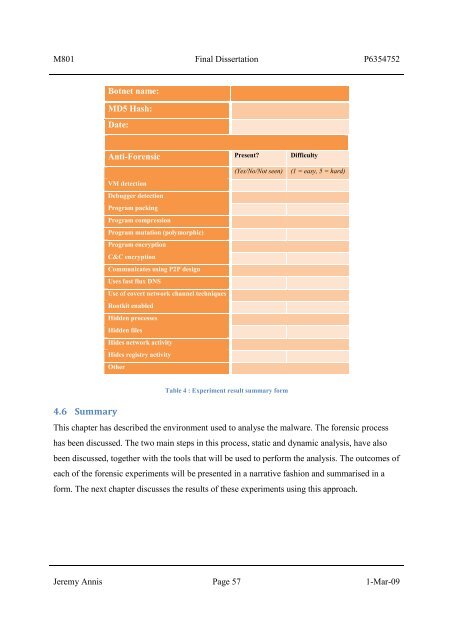
Botnet name:<br />
MD5 Hash:<br />
Date:<br />
<strong>An</strong>ti-Forensic Present? Difficulty<br />
VM detection<br />
Debugger detection<br />
Program packing<br />
Program compression<br />
Program mutation (polymorphic)<br />
Program encryption<br />
C&C encryption<br />
Communicates using P2P design<br />
Uses fast flux DNS<br />
Use <strong>of</strong> covert network channel techniques<br />
Rootkit enabled<br />
Hidden processes<br />
Hidden files<br />
Hides network activity<br />
Hides registry activity<br />
O<strong>the</strong>r<br />
4.6 Summary<br />
Table 4 : Experiment result summary form<br />
(Yes/No/Not seen) (1 = easy, 5 = hard)<br />
This chapter has described <strong>the</strong> environment <strong>use</strong>d to analyse <strong>the</strong> malware. The <strong>forensic</strong> process<br />
has been discussed. The two main steps in this process, static and dynamic analysis, have also<br />
been discussed, toge<strong>the</strong>r with <strong>the</strong> tools that will be <strong>use</strong>d to perform <strong>the</strong> analysis. The outcomes <strong>of</strong><br />
each <strong>of</strong> <strong>the</strong> <strong>forensic</strong> experiments will be presented in a narrative fashion and summarised in a<br />
form. The next chapter discusses <strong>the</strong> results <strong>of</strong> <strong>the</strong>se experiments using this approach.<br />
Jeremy <strong>An</strong>nis Page 57 1-Mar-09