Civil Liberties and Security in Cyberspace - Hoover Institution
Civil Liberties and Security in Cyberspace - Hoover Institution
Civil Liberties and Security in Cyberspace - Hoover Institution
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
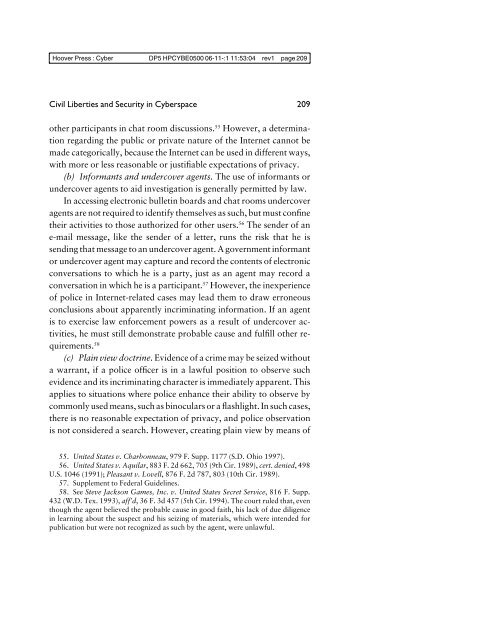
<strong>Hoover</strong> Press : Cyber DP5 HPCYBE0500 06-11-:1 11:53:04 rev1 page 209<br />
<strong>Civil</strong> <strong>Liberties</strong> <strong>and</strong> <strong>Security</strong> <strong>in</strong> <strong>Cyberspace</strong><br />
209<br />
other participants <strong>in</strong> chat room discussions. 55 However, a determ<strong>in</strong>ation<br />
regard<strong>in</strong>g the public or private nature of the Internet cannot be<br />
made categorically, because the Internet can be used <strong>in</strong> different ways,<br />
with more or less reasonable or justifiable expectations of privacy.<br />
(b) Informants <strong>and</strong> undercover agents. The use of <strong>in</strong>formants or<br />
undercover agents to aid <strong>in</strong>vestigation is generally permitted by law.<br />
In access<strong>in</strong>g electronic bullet<strong>in</strong> boards <strong>and</strong> chat rooms undercover<br />
agents are not required to identify themselves as such, but must conf<strong>in</strong>e<br />
their activities to those authorized for other users. 56 The sender of an<br />
e-mail message, like the sender of a letter, runs the risk that he is<br />
send<strong>in</strong>g that message to an undercover agent. A government <strong>in</strong>formant<br />
or undercover agent may capture <strong>and</strong> record the contents of electronic<br />
conversations to which he is a party, just as an agent may record a<br />
conversation <strong>in</strong> which he is a participant. 57 However, the <strong>in</strong>experience<br />
of police <strong>in</strong> Internet-related cases may lead them to draw erroneous<br />
conclusions about apparently <strong>in</strong>crim<strong>in</strong>at<strong>in</strong>g <strong>in</strong>formation. If an agent<br />
is to exercise law enforcement powers as a result of undercover activities,<br />
he must still demonstrate probable cause <strong>and</strong> fulfill other requirements.<br />
58<br />
(c) Pla<strong>in</strong> view doctr<strong>in</strong>e. Evidence of a crime may be seized without<br />
a warrant, if a police officer is <strong>in</strong> a lawful position to observe such<br />
evidence <strong>and</strong> its <strong>in</strong>crim<strong>in</strong>at<strong>in</strong>g character is immediately apparent. This<br />
applies to situations where police enhance their ability to observe by<br />
commonly used means, such as b<strong>in</strong>oculars or a flashlight. In such cases,<br />
there is no reasonable expectation of privacy, <strong>and</strong> police observation<br />
is not considered a search. However, creat<strong>in</strong>g pla<strong>in</strong> view by means of<br />
55. United States v. Charbonneau, 979 F. Supp. 1177 (S.D. Ohio 1997).<br />
56. United States v. Aquilar, 883 F. 2d 662, 705 (9th Cir. 1989), cert. denied, 498<br />
U.S. 1046 (1991); Pleasant v. Lovell, 876 F. 2d 787, 803 (10th Cir. 1989).<br />
57. Supplement to Federal Guidel<strong>in</strong>es.<br />
58. See Steve Jackson Games, Inc. v. United States Secret Service, 816 F. Supp.<br />
432 (W.D. Tex. 1993), aff’d, 36 F. 3d 457 (5th Cir. 1994). The court ruled that, even<br />
though the agent believed the probable cause <strong>in</strong> good faith, his lack of due diligence<br />
<strong>in</strong> learn<strong>in</strong>g about the suspect <strong>and</strong> his seiz<strong>in</strong>g of materials, which were <strong>in</strong>tended for<br />
publication but were not recognized as such by the agent, were unlawful.