System i: Programming Secure Sockets APIs - IBM
System i: Programming Secure Sockets APIs - IBM
System i: Programming Secure Sockets APIs - IBM
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
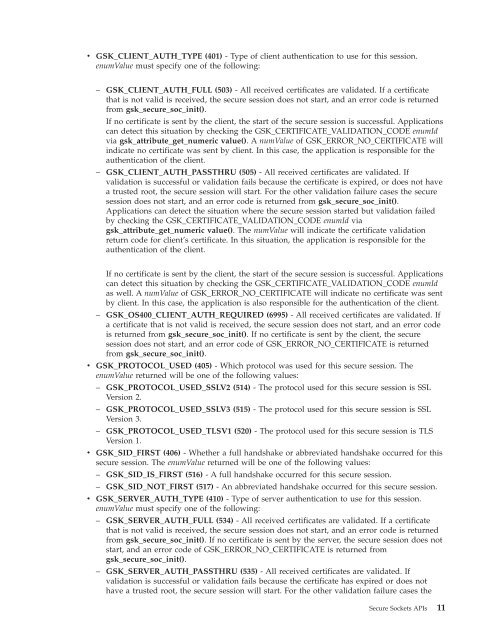
v GSK_CLIENT_AUTH_TYPE (401) - Type of client authentication to use for this session.<br />
enumValue must specify one of the following:<br />
– GSK_CLIENT_AUTH_FULL (503) - All received certificates are validated. If a certificate<br />
that is not valid is received, the secure session does not start, and an error code is returned<br />
from gsk_secure_soc_init().<br />
If no certificate is sent by the client, the start of the secure session is successful. Applications<br />
can detect this situation by checking the GSK_CERTIFICATE_VALIDATION_CODE enumId<br />
via gsk_attribute_get_numeric value(). A numValue of GSK_ERROR_NO_CERTIFICATE will<br />
indicate no certificate was sent by client. In this case, the application is responsible for the<br />
authentication of the client.<br />
– GSK_CLIENT_AUTH_PASSTHRU (505) - All received certificates are validated. If<br />
validation is successful or validation fails because the certificate is expired, or does not have<br />
a trusted root, the secure session will start. For the other validation failure cases the secure<br />
session does not start, and an error code is returned from gsk_secure_soc_init().<br />
Applications can detect the situation where the secure session started but validation failed<br />
by checking the GSK_CERTIFICATE_VALIDATION_CODE enumId via<br />
gsk_attribute_get_numeric value(). The numValue will indicate the certificate validation<br />
return code for client’s certificate. In this situation, the application is responsible for the<br />
authentication of the client.<br />
If no certificate is sent by the client, the start of the secure session is successful. Applications<br />
can detect this situation by checking the GSK_CERTIFICATE_VALIDATION_CODE enumId<br />
as well. A numValue of GSK_ERROR_NO_CERTIFICATE will indicate no certificate was sent<br />
by client. In this case, the application is also responsible for the authentication of the client.<br />
– GSK_OS400_CLIENT_AUTH_REQUIRED (6995) - All received certificates are validated. If<br />
a certificate that is not valid is received, the secure session does not start, and an error code<br />
is returned from gsk_secure_soc_init(). If no certificate is sent by the client, the secure<br />
session does not start, and an error code of GSK_ERROR_NO_CERTIFICATE is returned<br />
from gsk_secure_soc_init().<br />
v GSK_PROTOCOL_USED (405) - Which protocol was used for this secure session. The<br />
enumValue returned will be one of the following values:<br />
– GSK_PROTOCOL_USED_SSLV2 (514) - The protocol used for this secure session is SSL<br />
Version 2.<br />
– GSK_PROTOCOL_USED_SSLV3 (515) - The protocol used for this secure session is SSL<br />
Version 3.<br />
– GSK_PROTOCOL_USED_TLSV1 (520) - The protocol used for this secure session is TLS<br />
Version 1.<br />
v GSK_SID_FIRST (406) - Whether a full handshake or abbreviated handshake occurred for this<br />
secure session. The enumValue returned will be one of the following values:<br />
– GSK_SID_IS_FIRST (516) - A full handshake occurred for this secure session.<br />
– GSK_SID_NOT_FIRST (517) - An abbreviated handshake occurred for this secure session.<br />
v GSK_SERVER_AUTH_TYPE (410) - Type of server authentication to use for this session.<br />
enumValue must specify one of the following:<br />
– GSK_SERVER_AUTH_FULL (534) - All received certificates are validated. If a certificate<br />
that is not valid is received, the secure session does not start, and an error code is returned<br />
from gsk_secure_soc_init(). If no certificate is sent by the server, the secure session does not<br />
start, and an error code of GSK_ERROR_NO_CERTIFICATE is returned from<br />
gsk_secure_soc_init().<br />
– GSK_SERVER_AUTH_PASSTHRU (535) - All received certificates are validated. If<br />
validation is successful or validation fails because the certificate has expired or does not<br />
have a trusted root, the secure session will start. For the other validation failure cases the<br />
<strong>Secure</strong> <strong>Sockets</strong> <strong>APIs</strong> 11