Blackberry Proof-of-Concept: Malicious Applications - Hacker Halted
Blackberry Proof-of-Concept: Malicious Applications - Hacker Halted
Blackberry Proof-of-Concept: Malicious Applications - Hacker Halted
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
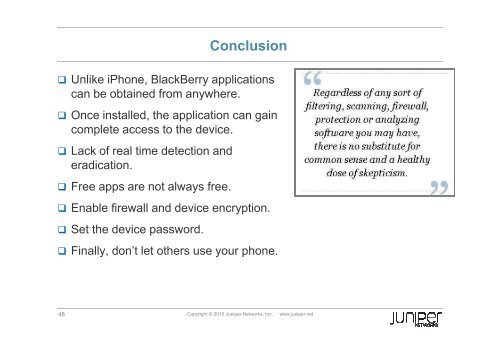
Conclusion<br />
Unlike iPhone, BlackBerry applications<br />
can be obtained from anywhere.<br />
Once installed, the application can gain<br />
complete access to the device.<br />
Lack <strong>of</strong> real time detection and<br />
eradication.<br />
Free apps are not always free.<br />
Enable firewall and device encryption.<br />
Set the device password.<br />
Finally, don’t let others use your phone.<br />
48 Copyright © 2010 Juniper Networks, Inc. www.juniper.net