Part C: Appendices
Part C: Appendices
Part C: Appendices
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Chapter:<br />
VIII<br />
Page:<br />
4<br />
Version:<br />
2.2<br />
Edition:<br />
2000-05-10<br />
Homebanking-Computer-Interface (HBCI)<br />
Chapter:<br />
Section:<br />
<strong>Appendices</strong><br />
List of contents<br />
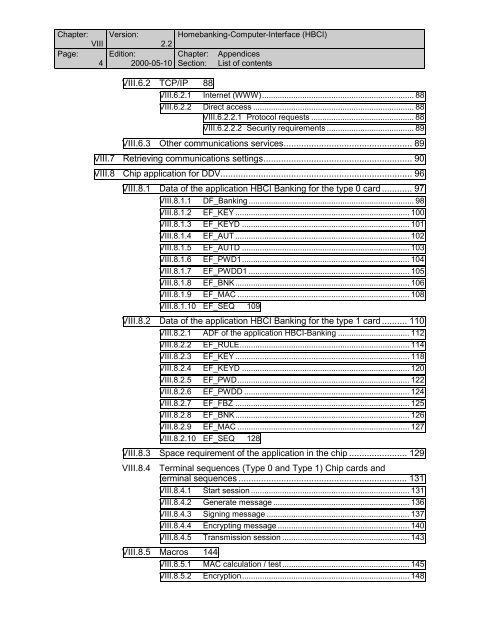
VIII.6.2 TCP/IP 88<br />
VIII.6.2.1 Internet (WWW).................................................................... 88<br />
VIII.6.2.2 Direct access ........................................................................ 88<br />
VIII.6.2.2.1 Protocol requests .............................................. 88<br />
VIII.6.2.2.2 Security requirements ....................................... 89<br />
VIII.6.3 Other communications services................................................... 89<br />
VIII.7 Retrieving communications settings........................................................... 90<br />
VIII.8 Chip application for DDV............................................................................ 96<br />
VIII.8.1 Data of the application HBCI Banking for the type 0 card ............ 97<br />
VIII.8.1.1 DF_Banking .......................................................................... 98<br />
VIII.8.1.2 EF_KEY .............................................................................. 100<br />
VIII.8.1.3 EF_KEYD ........................................................................... 101<br />
VIII.8.1.4 EF_AUT .............................................................................. 102<br />
VIII.8.1.5 EF_AUTD ........................................................................... 103<br />
VIII.8.1.6 EF_PWD1........................................................................... 104<br />
VIII.8.1.7 EF_PWDD1 ........................................................................ 105<br />
VIII.8.1.8 EF_BNK.............................................................................. 106<br />
VIII.8.1.9 EF_MAC ............................................................................. 108<br />
VIII.8.1.10 EF_SEQ 109<br />
VIII.8.2 Data of the application HBCI Banking for the type 1 card .......... 110<br />
VIII.8.2.1 ADF of the application HBCI-Banking ................................ 112<br />
VIII.8.2.2 EF_RULE............................................................................ 114<br />
VIII.8.2.3 EF_KEY .............................................................................. 118<br />
VIII.8.2.4 EF_KEYD ........................................................................... 120<br />
VIII.8.2.5 EF_PWD............................................................................. 122<br />
VIII.8.2.6 EF_PWDD .......................................................................... 124<br />
VIII.8.2.7 EF_FBZ .............................................................................. 125<br />
VIII.8.2.8 EF_BNK.............................................................................. 126<br />
VIII.8.2.9 EF_MAC ............................................................................. 127<br />
VIII.8.2.10 EF_SEQ 128<br />
VIII.8.3 Space requirement of the application in the chip ....................... 129<br />
VIII.8.4 Terminal sequences (Type 0 and Type 1) Chip cards and<br />
terminal sequences ................................................................... 131<br />
VIII.8.4.1 Start session ....................................................................... 131<br />
VIII.8.4.2 Generate message ............................................................. 136<br />
VIII.8.4.3 Signing message ................................................................ 137<br />
VIII.8.4.4 Encrypting message ........................................................... 140<br />
VIII.8.4.5 Transmission session ......................................................... 143<br />
VIII.8.5 Macros 144<br />
VIII.8.5.1 MAC calculation / test......................................................... 145<br />
VIII.8.5.2 Encryption........................................................................... 148