Fulltext - International Journal of Computer Technology and ...
Fulltext - International Journal of Computer Technology and ...
Fulltext - International Journal of Computer Technology and ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
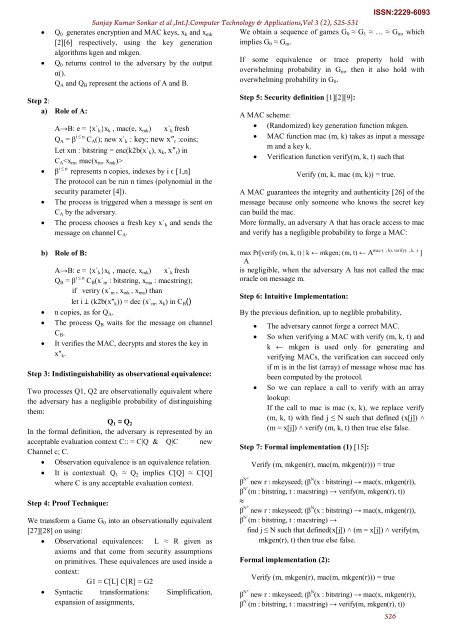
Q 0 generates encryption <strong>and</strong> MAC keys, x k <strong>and</strong> x mk<br />
[2][6] respectively, using the key generation<br />
algorithms kgen <strong>and</strong> mkgen.<br />
Q 0 returns control to the adversary by the output<br />
α().<br />
Q A <strong>and</strong> Q B represent the actions <strong>of</strong> A <strong>and</strong> B.<br />
Step 2:<br />
a) Role <strong>of</strong> A:<br />
<br />
<br />
<br />
Sanjay Kumar Sonkar et al ,Int.J.<strong>Computer</strong> <strong>Technology</strong> & Applications,Vol 3 (2), 525-531<br />
A→B: e = {xˋk}x k , mac(e, x mk ) xˋk fresh<br />
Q A = β i ≤ n C A (); new xˋk : key; new x″ r :coins;<br />
Let xm : bitstring = enc(k2b(xˋk), x k , x″ r ) in<br />
C A <br />
β i ≤ n represents n copies, indexes by i ϵ [1,n]<br />
The protocol can be run n times (polynomial in the<br />
security parameter [4]).<br />
The process is triggered when a message is sent on<br />
C A by the adversary.<br />
The process chooses a fresh key xˋk <strong>and</strong> sends the<br />
message on channel C A .<br />
We obtain a sequence <strong>of</strong> games G 0 ≈ G 1 ≈ … ≈ G m , which<br />
implies G 0 ≈ G m .<br />
If some equivalence or trace property hold with<br />
overwhelming probability in G m , then it also hold with<br />
overwhelming probability in G 0 .<br />
Step 5: Security definition [1][2][9]:<br />
A MAC scheme:<br />
(R<strong>and</strong>omized) key generation function mkgen.<br />
MAC function mac (m, k) takes as input a message<br />
m <strong>and</strong> a key k.<br />
Verification function verify(m, k, t) such that<br />
Verify (m, k, mac (m, k)) = true.<br />
ISSN:2229-6093<br />
A MAC guarantees the integrity <strong>and</strong> authenticity [26] <strong>of</strong> the<br />
message because only someone who knows the secret key<br />
can build the mac.<br />
More formally, an adversary A that has oracle access to mac<br />
<strong>and</strong> verify has a negligible probability to forge a MAC:<br />
b) Role <strong>of</strong> B:<br />
A→B: e = {xˋk}x k , mac(e, x mk ) xˋk fresh<br />
Q B = β i ≤ n C B (xˋm : bitstring, x ma : macstring);<br />
if veriry (xˋm , x mk , x ma ) than<br />
let i ⊥ (k2b(x″ k )) = dec (xˋm, x k ) in C B ()<br />
n copies, as for Q A .<br />
The process Q B waits for the message on channel<br />
C B .<br />
It verifies the MAC, decrypts <strong>and</strong> stores the key in<br />
x″ k .<br />
Step 3: Indistinguishability as observational equivalence:<br />
Two processes Q1, Q2 are observationally equivalent where<br />
the adversary has a negligible probability <strong>of</strong> distinguishing<br />
them:<br />
Q 1 ≈ Q 2<br />
In the formal definition, the adversary is represented by an<br />
acceptable evaluation context C:: = C|Q & Q|C new<br />
Channel c; C.<br />
Observation equivalence is an equivalence relation.<br />
It is contextual: Q 1 ≈ Q 2 implies C[Q] ≈ C[Q]<br />
where C is any acceptable evaluation context.<br />
Step 4: Pro<strong>of</strong> Technique:<br />
We transform a Game G 0 into an observationally equivalent<br />
[27][28] on using:<br />
Observational equivalences: L ≈ R given as<br />
axioms <strong>and</strong> that come from security assumptions<br />
on primitives. These equivalences are used inside a<br />
context:<br />
G1 ≈ C[L] C[R] ≈ G2<br />
Syntactic transformations: Simplification,<br />
expansion <strong>of</strong> assignments,<br />
max Pr[verify (m, k, t) | k ← mkgen; (m, t) ← A mac (. , k), verify(. , k, .) ]<br />
A<br />
is negligible, when the adversary A has not called the mac<br />
oracle on message m.<br />
Step 6: Intuitive Implementation:<br />
By the previous definition, up to neglible probability,<br />
<br />
<br />
<br />
The adversary cannot forge a correct MAC.<br />
So when verifying a MAC with verify (m, k, t) <strong>and</strong><br />
k ← mkgen is used only for generating <strong>and</strong><br />
verifying MACs, the verification can succeed only<br />
if m is in the list (array) <strong>of</strong> message whose mac has<br />
been computed by the protocol.<br />
So we can replace a call to verify with an array<br />
lookup:<br />
If the call to mac is mac (x, k), we replace verify<br />
(m, k, t) with find j ≤ N such that defined (x[j]) ˄<br />
(m = x[j]) ˄ verify (m, k, t) then true else false.<br />
Step 7: Formal implementation (1) [15]:<br />
Verify (m, mkgen(r), mac(m, mkgen(r))) = true<br />
β N″ new r : mkeyseed; (β N (x : bitstring) → mac(x, mkgen(r)),<br />
β Nˋ(m : bitstring, t : macstring) → verify(m, mkgen(r), t))<br />
≈<br />
β N″ new r : mkeyseed; (β N (x : bitstring) → mac(x, mkgen(r)),<br />
β Nˋ(m : bitstring, t : macstring) →<br />
find j ≤ N such that defined(x[j]) ˄ (m = x[j]) ˄ verify(m,<br />
mkgen(r), t) then true else false.<br />
Formal implementation (2):<br />
Verify (m, mkgen(r), mac(m, mkgen(r))) = true<br />
β N″ new r : mkeyseed; (β N (x : bitstring) → mac(x, mkgen(r)),<br />
β Nˋ(m : bitstring, t : macstring) → verify(m, mkgen(r), t))<br />
526