IPT Attack Mitigation - Interop
IPT Attack Mitigation - Interop
IPT Attack Mitigation - Interop
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
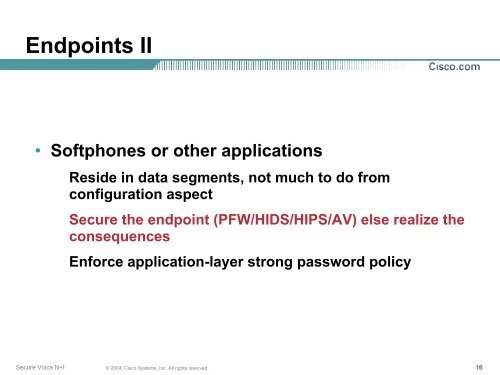
Endpoints II<br />
• Softphones or other applications<br />
Reside in data segments, not much to do from<br />
configuration aspect<br />
Secure the endpoint (PFW/HIDS/HIPS/AV) else realize the<br />
consequences<br />
Enforce application-layer strong password policy<br />
Secure Voice N+I<br />
© 2004, Cisco Systems, Inc. All rights reserved.<br />
16