Defeating Overflow Attacks - orkspace.net
Defeating Overflow Attacks - orkspace.net
Defeating Overflow Attacks - orkspace.net
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
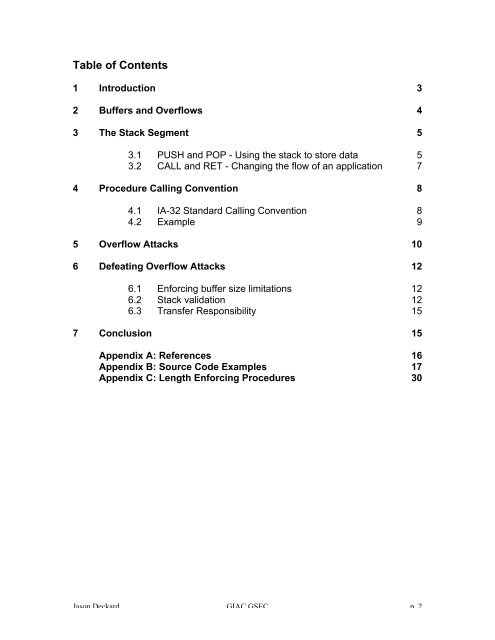
Table of Contents<br />
1 Introduction 3<br />
2 Buffers and <strong>Overflow</strong>s 4<br />
3 The Stack Segment 5<br />
3.1 PUSH and POP - Using the stack to store data 5<br />
3.2 CALL and RET - Changing the flow of an application 7<br />
4 Procedure Calling Convention 8<br />
4.1 IA-32 Standard Calling Convention 8<br />
4.2 Example 9<br />
5 <strong>Overflow</strong> <strong>Attacks</strong> 10<br />
6 <strong>Defeating</strong> <strong>Overflow</strong> <strong>Attacks</strong> 12<br />
6.1 Enforcing buffer size limitations 12<br />
6.2 Stack validation 12<br />
6.3 Transfer Responsibility 15<br />
7 Conclusion 15<br />
Appendix A: References 16<br />
Appendix B: Source Code Examples 17<br />
Appendix C: Length Enforcing Procedures 30<br />
Jason Deckard GIAC GSEC p. 2