Side-Channel Analysis (SCA) â A comparative approach on smart ...
Side-Channel Analysis (SCA) â A comparative approach on smart ...
Side-Channel Analysis (SCA) â A comparative approach on smart ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
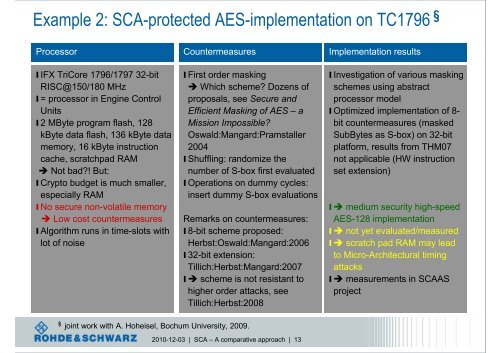
Example 2: <str<strong>on</strong>g>SCA</str<strong>on</strong>g>-protected AES-implementati<strong>on</strong> <strong>on</strong> TC1796 §<br />
Processor Countermeasures Implementati<strong>on</strong> results<br />
l IFX TriCore 1796/1797 32-bit<br />
RISC@150/180 MHz<br />
l = processor in Engine C<strong>on</strong>trol<br />
Units<br />
l 2 MByte program flash, 128<br />
kByte data flash, 136 kByte data<br />
memory, 16 kByte instructi<strong>on</strong><br />
cache, scratchpad RAM<br />
Not bad?! But:<br />
l Crypto budget is much smaller,<br />
especially RAM<br />
l No secure n<strong>on</strong>-volatile memory<br />
Low cost countermeasures<br />
l Algorithm runs in time-slots with<br />
lot of noise<br />
l First order masking<br />
Which scheme? Dozens of<br />
proposals, see Secure and<br />
Efficient Masking of AES – a<br />
Missi<strong>on</strong> Impossible?<br />
Oswald:Mangard:Pramstaller<br />
2004<br />
l Shuffling: randomize the<br />
number of S-box first evaluated<br />
l Operati<strong>on</strong>s <strong>on</strong> dummy cycles:<br />
insert dummy S-box evaluati<strong>on</strong>s<br />
Remarks <strong>on</strong> countermeasures:<br />
l 8-bit scheme proposed:<br />
Herbst:Oswald:Mangard:2006<br />
l 32-bit extensi<strong>on</strong>:<br />
Tillich:Herbst:Mangard:2007<br />
l scheme is not resistant to<br />
higher order attacks, see<br />
Tillich:Herbst:2008<br />
l Investigati<strong>on</strong> of various masking<br />
schemes using abstract<br />
processor model<br />
l Optimized implementati<strong>on</strong> of 8-<br />
bit countermeasures (masked<br />
SubBytes as S-box) <strong>on</strong> 32-bit<br />
platform, results from THM07<br />
not applicable (HW instructi<strong>on</strong><br />
set extensi<strong>on</strong>)<br />
l medium security high-speed<br />
AES-128 implementati<strong>on</strong><br />
l not yet evaluated/measured<br />
l scratch pad RAM may lead<br />
to Micro-Architectural timing<br />
attacks<br />
l measurements in <str<strong>on</strong>g>SCA</str<strong>on</strong>g>AS<br />
project<br />
§ joint work with A. Hoheisel, Bochum University, 2009.<br />
2010-12-03 | <str<strong>on</strong>g>SCA</str<strong>on</strong>g> – A <str<strong>on</strong>g>comparative</str<strong>on</strong>g> <str<strong>on</strong>g>approach</str<strong>on</strong>g> | 13