Check Point Vpn-1/Securemote/Secureclient Version 4.1 SP2 ...
Check Point Vpn-1/Securemote/Secureclient Version 4.1 SP2 ...
Check Point Vpn-1/Securemote/Secureclient Version 4.1 SP2 ...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
SecuRemote/SecureClient<br />
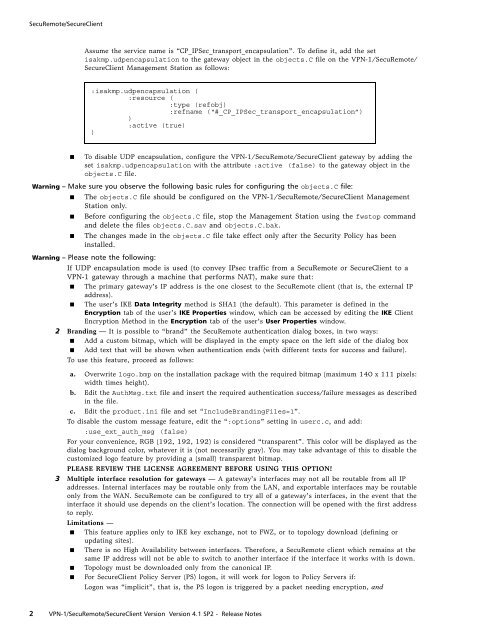
Assume the service name is “CP_IPSec_transport_encapsulation”. To define it, add the set<br />
isakmp.udpencapsulation to the gateway object in the objects.C file on the VPN-1/SecuRemote/<br />
SecureClient Management Station as follows:<br />
:isakmp.udpencapsulation (<br />
:resource (<br />
:type (refobj)<br />
:refname (“#_CP_IPSec_transport_encapsulation”)<br />
)<br />
:active (true)<br />
)<br />
■ To disable UDP encapsulation, configure the VPN-1/SecuRemote/SecureClient gateway by adding the<br />
set isakmp.udpencapsulation with the attribute :active (false) to the gateway object in the<br />
objects.C file.<br />
Warning – Make sure you observe the following basic rules for configuring the objects.C file:<br />
■ The objects.C file should be configured on the VPN-1/SecuRemote/SecureClient Management<br />
Station only.<br />
■ Before configuring the objects.C file, stop the Management Station using the fwstop command<br />
and delete the files objects.C.sav and objects.C.bak.<br />
■ The changes made in the objects.C file take effect only after the Security Policy has been<br />
installed.<br />
Warning – Please note the following:<br />
If UDP encapsulation mode is used (to convey IPsec traffic from a SecuRemote or SecureClient to a<br />
VPN-1 gateway through a machine that performs NAT), make sure that:<br />
■ The primary gateway’s IP address is the one closest to the SecuRemote client (that is, the external IP<br />
address).<br />
■ The user’s IKE Data Integrity method is SHA1 (the default). This parameter is defined in the<br />
Encryption tab of the user’s IKE Properties window, which can be accessed by editing the IKE Client<br />
Encryption Method in the Encryption tab of the user’s User Properties window.<br />
2 Branding — It is possible to “brand” the SecuRemote authentication dialog boxes, in two ways:<br />
■ Add a custom bitmap, which will be displayed in the empty space on the left side of the dialog box<br />
■ Add text that will be shown when authentication ends (with different texts for success and failure).<br />
To use this feature, proceed as follows:<br />
a. Overwrite logo.bmp on the installation package with the required bitmap (maximum 140 x 111 pixels:<br />
width times height).<br />
b. Edit the AuthMsg.txt file and insert the required authentication success/failure messages as described<br />
in the file.<br />
c. Edit the product.ini file and set “IncludeBrandingFiles=1”.<br />
To disable the custom message feature, edit the “:options” setting in userc.c, and add:<br />
:use_ext_auth_msg (false)<br />
For your convenience, RGB (192, 192, 192) is considered “transparent”. This color will be displayed as the<br />
dialog background color, whatever it is (not necessarily gray). You may take advantage of this to disable the<br />
customized logo feature by providing a (small) transparent bitmap.<br />
PLEASE REVIEW THE LICENSE AGREEMENT BEFORE USING THIS OPTION!<br />
3 Multiple interface resolution for gateways — A gateway’s interfaces may not all be routable from all IP<br />
addresses. Internal interfaces may be routable only from the LAN, and exportable interfaces may be routable<br />
only from the WAN. SecuRemote can be configured to try all of a gateway’s interfaces, in the event that the<br />
interface it should use depends on the client’s location. The connection will be opened with the first address<br />
to reply.<br />
Limitations —<br />
■ This feature applies only to IKE key exchange, not to FWZ, or to topology download (defining or<br />
updating sites).<br />
■ There is no High Availability between interfaces. Therefore, a SecuRemote client which remains at the<br />
same IP address will not be able to switch to another interface if the interface it works with is down.<br />
■ Topology must be downloaded only from the canonical IP.<br />
■ For SecureClient Policy Server (PS) logon, it will work for logon to Policy Servers if:<br />
Logon was “implicit”, that is, the PS logon is triggered by a packet needing encryption, and<br />
2 VPN-1/SecuRemote/SecureClient <strong>Version</strong> <strong>Version</strong> <strong>4.1</strong> <strong>SP2</strong> - Release Notes