Can you still trust your network card? - Agence nationale de la ...
Can you still trust your network card? - Agence nationale de la ...
Can you still trust your network card? - Agence nationale de la ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
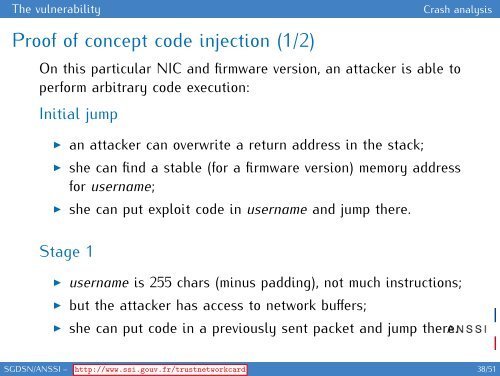
The vulnerability Crash analysis<br />
Proof of concept co<strong>de</strong> injection (1/2)<br />
On this particu<strong>la</strong>r NIC and firmware version, an attacker is able to<br />
perform arbitrary co<strong>de</strong> execution:<br />
Initial jump<br />
◮ an attacker can overwrite a return address in the stack;<br />
◮ she can find a stable (for a firmware version) memory address<br />
for username;<br />
◮ she can put exploit co<strong>de</strong> in username and jump there.<br />
Stage 1<br />
◮ username is 255 chars (minus padding), not much instructions;<br />
◮ but the attacker has access to <strong>network</strong> buffers;<br />
◮ she can put co<strong>de</strong> in a previously sent packet and jump there.<br />
SGDSN/ANSSI – http://www.ssi.gouv.fr/<strong>trust</strong><strong>network</strong><strong>card</strong> 38/51