- Page 1 and 2:
CEH v6 Resource Guide http://www.ec
- Page 3 and 4:
Page 8 Hackers are here. Where are
- Page 5 and 6:
Page 10 http://www.eccouncil.org Co
- Page 7 and 8:
Page 12 o 18 U.S.C. § 1029 • Pen
- Page 9 and 10:
Page 14 • People Search http://ww
- Page 11 and 12:
Page 16 • Necrosoft Advanced DIG
- Page 13 and 14:
Page 18 o Finding Specifi c Files o
- Page 15 and 16:
Page 20 � Tool: Google Hacks �
- Page 17 and 18:
Page 22 o Atelier Web Ports Traffi
- Page 19 and 20:
Page 24 o IIS Lockdown Tool o Tool:
- Page 21 and 22:
Page 26 • NetProxy • Proxy+ •
- Page 23 and 24:
Page 28 o Management Information Ba
- Page 25 and 26:
Page 30 o PDF Password Cracker o Ab
- Page 27 and 28:
Page 32 o Cracking NT/2000 password
- Page 29 and 30:
Page 34 o Advanced Anti Keylogger o
- Page 31 and 32:
Page 36 http://www.eccouncil.org
- Page 33 and 34:
Page 38 http://www.eccouncil.org
- Page 35 and 36:
Page 40 o Criminal Rat Beta o VicSp
- Page 37 and 38:
Page 42 o CurrPorts Tool o Process
- Page 39 and 40:
Page 44 • Self -Modifi cation htt
- Page 41 and 42:
Page 46 o ClamWin o Norman Virus Co
- Page 43 and 44:
Page 48 � DNS Poisoning Technique
- Page 45 and 46:
Page 50 Module 11: Social Engineeri
- Page 47 and 48:
Page 52 � Reasons for Successful
- Page 49 and 50:
Page 54 � Creating Strong Passwor
- Page 51 and 52:
Page 56 � Refl ective DNS Attacks
- Page 53 and 54:
Page 58 � Programs that Performs
- Page 55 and 56:
Page 60 � Patch Management Checkl
- Page 57 and 58:
Page 62 � Cookie Snooping � Aut
- Page 59 and 60:
Page 64 • Digest Authentication o
- Page 61 and 62:
Page 66 o Atomic Mailbox Password C
- Page 63 and 64:
Page 68 o Absinthe � Blind SQL In
- Page 65 and 66:
Page 70 o WEP Attack o Cracking WEP
- Page 67 and 68:
Page 72 o 40W Digital Cellular Mobi
- Page 69 and 70:
Page 74 o Auditing Tool: BSD-Airtoo
- Page 71 and 72:
Page 76 � Laptop Security Counter
- Page 73 and 74:
Page 78 � Linux Tool: IPTraf �
- Page 75 and 76:
Page 80 � What is a Firewall? o W
- Page 77 and 78:
Page 82 • Honeypot - honeyd • H
- Page 79 and 80: Page 84 � RC4, RC5, RC6, Blowfi s
- Page 81 and 82: Page 86 � Cracking S/MIME Encrypt
- Page 83 and 84: Page 88 � Calculating Relative Cr
- Page 85 and 86: Page 90 � What is Covert Channel?
- Page 87 and 88: Page 92 � Testing Virus Codes �
- Page 89 and 90: Page 94 � Linking the object fi l
- Page 91 and 92: Page 96 o NASM o GDB o objdump o kt
- Page 93 and 94: Page 98 � NULL byte � shellcode
- Page 95 and 96: Page 100 � Tool: IDA Pro � Conv
- Page 97 and 98: Page 102 o OSX/Leap-A o Inqtana.A o
- Page 99 and 100: Page 104 � Waldo Beta 0.7 (b) Mod
- Page 101 and 102: Page 106 o Kaspersky Antivirus Mobi
- Page 103 and 104: Page 108 � Countermeasures Module
- Page 105 and 106: Page 110 o Service Interception o H
- Page 107 and 108: Page 112 o How to Write an RFID Vir
- Page 109 and 110: Page 114 � USB Attack on Windows
- Page 111 and 112: Page 116 Module 43: Cyber Warfare-
- Page 113 and 114: Page 118 o Tool: Adult Photo Blanke
- Page 115 and 116: Page 120 o Sunbelt Personal Firewal
- Page 117 and 118: Page 122 � Spying � Motives of
- Page 119 and 120: Page 124 � Introduction To Corpor
- Page 121 and 122: Page 126 http://www.eccouncil.org o
- Page 123 and 124: Page 128 Module 51: Hacking and Che
- Page 125 and 126: Page 130 o Cleaning Up Browsing His
- Page 127 and 128: Page 132 Module 54: Proxy Server Te
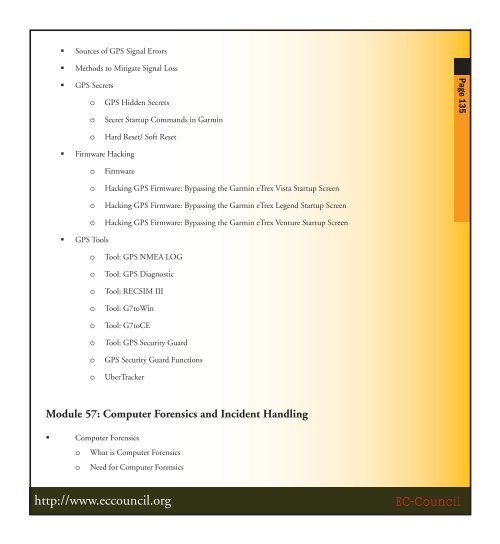
- Page 129: Page 134 o MailMarshal o WebMarshal
- Page 133 and 134: Page 138 o Net Credit/Debit Card Fr
- Page 135 and 136: Page 140 o Hardware Firewall o Netg
- Page 137 and 138: Page 142 o Minimum Password Age o M
- Page 139 and 140: Page 144 � Adjust Memory Quotas f
- Page 141 and 142: Page 146 � Devices: Allowed to Fo
- Page 143 and 144: Page 148 � Event Log o Maximum Ev
- Page 145 and 146: Page 150 � Intersite Messaging
- Page 147 and 148: Page 152 � SAP Agent � Secondar
- Page 149 and 150: Page 154 � Allow Active Content f
- Page 151 and 152: Page 156 � IP Security Policy Pro
- Page 153 and 154: Page 158 � NTFS � Data and Appl
- Page 155 and 156: Page 160 45 Minutes Physical Securi
- Page 157 and 158: Page 162 http://www.eccouncil.org C
- Page 159 and 160: Page 164 Lab 5.6 Scan the Network U
- Page 161 and 162: Page 166 Module 09 Viruses and Worm
- Page 163 and 164: Page 168 Lab 15.1 Session Hijacking
- Page 165 and 166: Page 170 Lab 22.3 Unreliable Guide
- Page 167 and 168: Page 172 Lab 35.4 8 Steps to protec
- Page 169 and 170: Page 174 Lab 42.1 SQL Server securi
- Page 171 and 172: Page 176 Module 50 - Software Pirac
- Page 173 and 174: Page 178 1. Introduction to Ethical
- Page 175 and 176: Page 180 8. Trojans and Backdoors M
- Page 177 and 178: Page 182 Module Brief: The Internet
- Page 179 and 180: Page 184 The security issues relate
- Page 181 and 182:
Page 186 IPNetsentryX, and FileGuar
- Page 183 and 184:
Page 188 43. Cyber Warfare- Hacking
- Page 185 and 186:
Page 190 example of popular game ex
- Page 187 and 188:
Page 192 Exam Code: 312-50 No. of q
- Page 189 and 190:
Page 194 Enumeration • Understand
- Page 191 and 192:
Page 196 • Understand ARP poisoni
- Page 193 and 194:
Page 198 • Understand patch manag
- Page 195 and 196:
Page 200 Buffer Overfl ows • Over