richard-bach-slides
richard-bach-slides
richard-bach-slides
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
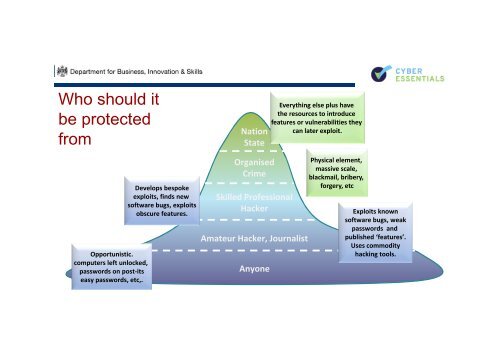
Who should it<br />
be protected<br />
from<br />
Opportunistic.<br />
computers left unlocked,<br />
passwords on post‐its<br />
easy passwords, etc,.<br />
Develops bespoke<br />
exploits, finds new<br />
software bugs, exploits<br />
obscure features.<br />
Nation<br />
State<br />
Organised<br />
Crime<br />
Skilled Professional<br />
Hacker<br />
Amateur Hacker, Journalist<br />
Anyone<br />
Everything else plus have<br />
the resources to introduce<br />
features or vulnerabilities they<br />
can later exploit.<br />
Physical element,<br />
massive scale,<br />
blackmail, bribery,<br />
forgery, etc<br />
Exploits known<br />
software bugs, weak<br />
passwords and<br />
published ‘features’.<br />
Uses commodity<br />
hacking tools.