evolution-of-poweliks
evolution-of-poweliks
evolution-of-poweliks
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
The <strong>evolution</strong> <strong>of</strong> the fileless click-fraud malware Poweliks<br />
Figure 6. Script 2 encoded using COM programing<br />
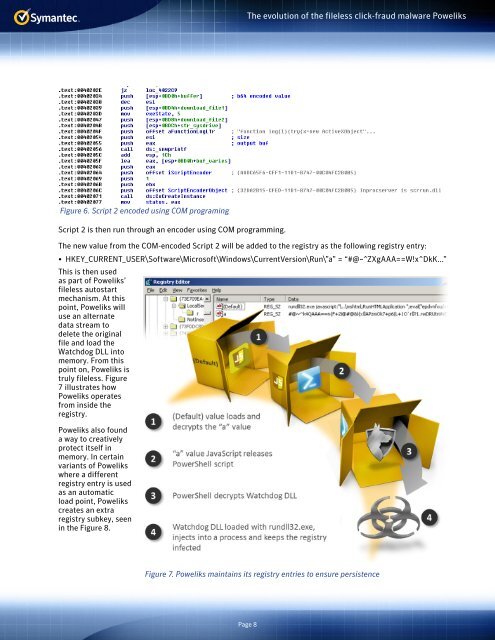
Script 2 is then run through an encoder using COM programming.<br />
The new value from the COM-encoded Script 2 will be added to the registry as the following registry entry:<br />
• HKEY_CURRENT_USER\S<strong>of</strong>tware\Micros<strong>of</strong>t\Windows\CurrentVersion\Run\”a” = “#@~^ZXgAAA==W!x^DkK...”<br />
This is then used<br />
as part <strong>of</strong> Poweliks’<br />
fileless autostart<br />
mechanism. At this<br />
point, Poweliks will<br />
use an alternate<br />
data stream to<br />
delete the original<br />
file and load the<br />
Watchdog DLL into<br />
memory. From this<br />
point on, Poweliks is<br />
truly fileless. Figure<br />
7 illustrates how<br />
Poweliks operates<br />
from inside the<br />
registry.<br />
Poweliks also found<br />
a way to creatively<br />
protect itself in<br />
memory. In certain<br />
variants <strong>of</strong> Poweliks<br />
where a different<br />
registry entry is used<br />
as an automatic<br />
load point, Poweliks<br />
creates an extra<br />
registry subkey, seen<br />
in the Figure 8.<br />
Figure 7. Poweliks maintains its registry entries to ensure persistence<br />
Page 8