Understanding Digital Identity Management - Phil Windley's ...
Understanding Digital Identity Management - Phil Windley's ...
Understanding Digital Identity Management - Phil Windley's ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
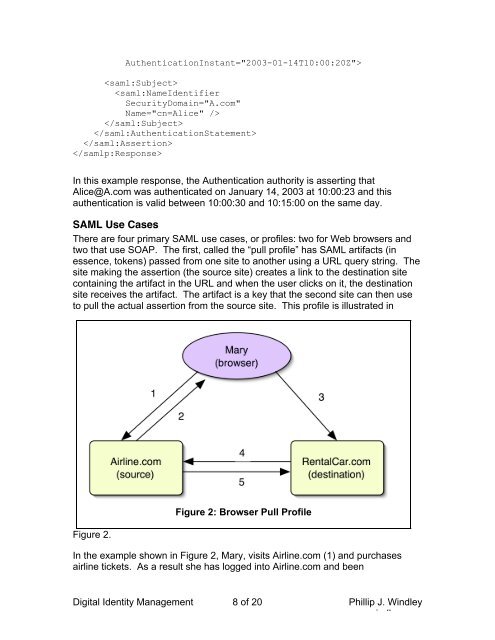
AuthenticationInstant="2003-01-14T10:00:20Z">In this example response, the Authentication authority is asserting thatAlice@A.com was authenticated on January 14, 2003 at 10:00:23 and thisauthentication is valid between 10:00:30 and 10:15:00 on the same day.SAML Use CasesThere are four primary SAML use cases, or profiles: two for Web browsers andtwo that use SOAP. The first, called the “pull profile” has SAML artifacts (inessence, tokens) passed from one site to another using a URL query string. Thesite making the assertion (the source site) creates a link to the destination sitecontaining the artifact in the URL and when the user clicks on it, the destinationsite receives the artifact. The artifact is a key that the second site can then useto pull the actual assertion from the source site. This profile is illustrated inFigure 2.Figure 2: Browser Pull ProfileIn the example shown in Figure 2, Mary, visits Airline.com (1) and purchasesairline tickets. As a result she has logged into Airline.com and been<strong>Digital</strong> <strong>Identity</strong> <strong>Management</strong> 8 of 20 <strong>Phil</strong>lip J. Windleywww.windley.com