Layer 2 Network encryption Verifiably secure, simple, fast. - Secunet
Layer 2 Network encryption Verifiably secure, simple, fast. - Secunet
Layer 2 Network encryption Verifiably secure, simple, fast. - Secunet
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Simple and effective - from integration<br />
to commissioning right through to live operation.<br />
SINA L2 Boxes can be integrated into your network conveniently and<br />
quickly and no change to your network infrastructure is required! Encryption<br />
is performed between boxes that are “invisible” to the network – the<br />
components can be deployed immediately and are easily integrated into<br />
the line between provider and company network. The <strong>simple</strong>st installation<br />
for a medium-sized company or public authority network, for example,<br />
can be completed within one day and without affecting live operation.<br />
SINA L2 Box<br />
From the point of integration onwards, your data and classified matters<br />
are transferred <strong>secure</strong>ly. Attackers are no longer able to identify the network<br />
infrastructure behind the SINA L2 Boxes. Once in use, the SINA L2<br />
Boxes operate with practically no administration and maintenance, thus<br />
reducing your operating costs to a minimum.<br />
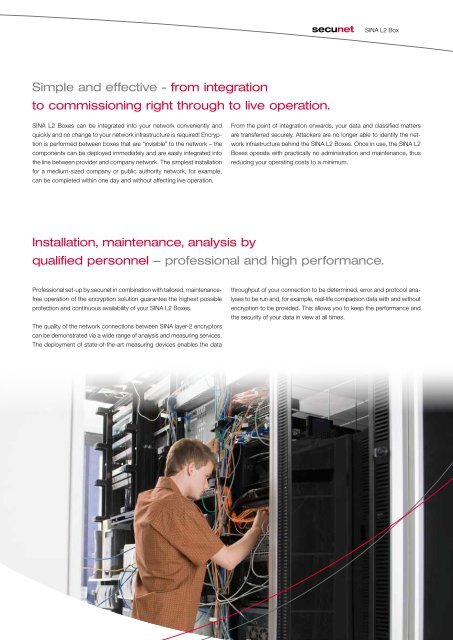
Installation, maintenance, analysis by<br />
qualified personnel – professional and high performance.<br />
Professional set-up by secunet in combination with tailored, maintenancefree<br />
operation of the <strong>encryption</strong> solution guarantee the highest possible<br />
protection and continuous availability of your SINA L2 Boxes.<br />
The quality of the network connections between SINA layer-2 encryptors<br />
can be demonstrated via a wide range of analysis and measuring services.<br />
The deployment of state-of-the-art measuring devices enables the data<br />
throughput of your connection to be determined, error and protocol analyses<br />
to be run and, for example, real-life comparison data with and without<br />
<strong>encryption</strong> to be provided. This allows you to keep the performance and<br />
the security of your data in view at all times.