Advanced Mac OS X Rootkits.pdf - Reverse Engineering Mac OS X
Advanced Mac OS X Rootkits.pdf - Reverse Engineering Mac OS X
Advanced Mac OS X Rootkits.pdf - Reverse Engineering Mac OS X
- No tags were found...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
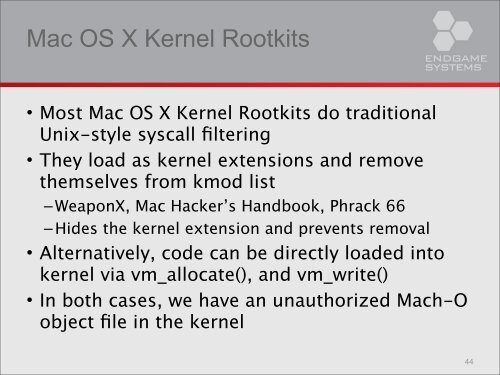
<strong>Mac</strong> <strong>OS</strong> X Kernel <strong>Rootkits</strong>• Most <strong>Mac</strong> <strong>OS</strong> X Kernel <strong>Rootkits</strong> do traditionalUnix-style syscall filtering• They load as kernel extensions and removethemselves from kmod list– WeaponX, <strong>Mac</strong> Hacker’s Handbook, Phrack 66– Hides the kernel extension and prevents removal• Alternatively, code can be directly loaded intokernel via vm_allocate(), and vm_write()• In both cases, we have an unauthorized <strong>Mac</strong>h-Oobject file in the kernel44