What is new in CHFI v8 Module - SSE
What is new in CHFI v8 Module - SSE
What is new in CHFI v8 Module - SSE
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
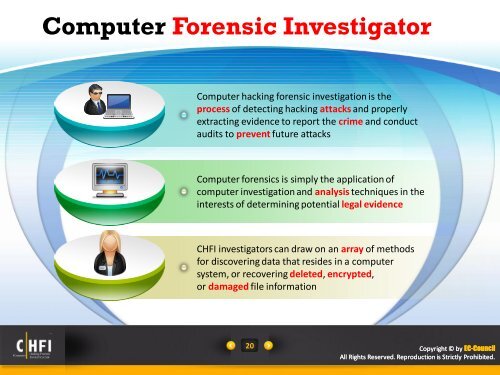
Computer Forensic InvestigatorComputer hack<strong>in</strong>g forensic <strong>in</strong>vestigation <strong>is</strong> theprocess of detect<strong>in</strong>g hack<strong>in</strong>g attacks and properlyextract<strong>in</strong>g evidence to report the crime and conductaudits to prevent future attacksComputer forensics <strong>is</strong> simply the application ofcomputer <strong>in</strong>vestigation and analys<strong>is</strong> techniques <strong>in</strong> the<strong>in</strong>terests of determ<strong>in</strong><strong>in</strong>g potential legal evidence<strong>CHFI</strong> <strong>in</strong>vestigators can draw on an array of methodsfor d<strong>is</strong>cover<strong>in</strong>g data that resides <strong>in</strong> a computersystem, or recover<strong>in</strong>g deleted, encrypted,or damaged file <strong>in</strong>formation20Copyright © by EC-CouncilAll Rights Reserved. Reproduction <strong>is</strong> Strictly Prohibited.