iPhone Rootkit? There's an App for that! - Reverse Engineering Mac ...
iPhone Rootkit? There's an App for that! - Reverse Engineering Mac ...
iPhone Rootkit? There's an App for that! - Reverse Engineering Mac ...
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
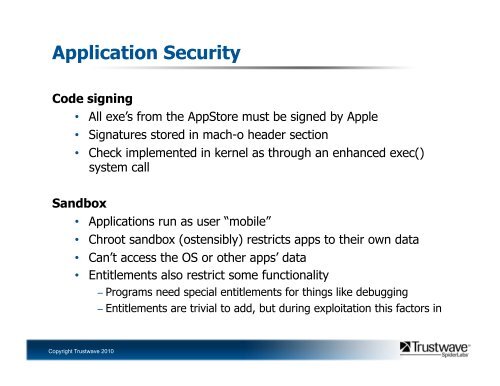
<strong>App</strong>lication SecurityCode signing• All exe’s from the <strong>App</strong>Store must be signed by <strong>App</strong>le• Signatures stored in mach-o header section• Check implemented in kernel as through <strong>an</strong> enh<strong>an</strong>ced exec()system callS<strong>an</strong>dbox• <strong>App</strong>lications run as user “mobile”• Chroot s<strong>an</strong>dbox (ostensibly) restricts apps to their own data• C<strong>an</strong>’t access the OS or other apps’ data• Entitlements also restrict some functionality− Programs need special entitlements <strong>for</strong> things like debugging− Entitlements are trivial to add, but during exploitation this factors inCopyright Trustwave 2010