Exploiting Voice over IP Networks - Hacking Exposed VoIP
Exploiting Voice over IP Networks - Hacking Exposed VoIP
Exploiting Voice over IP Networks - Hacking Exposed VoIP
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
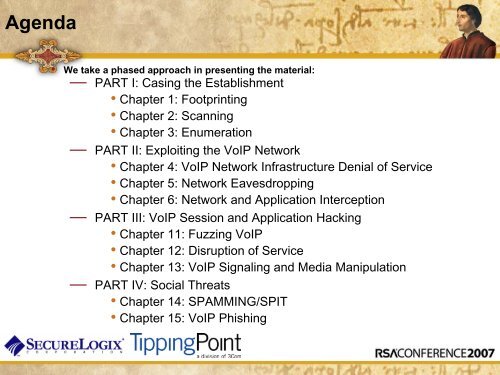
Agenda• We take a phased approach in presenting the material:— PART I: Casing the Establishment• Chapter 1: Footprinting• Chapter 2: Scanning• Chapter 3: Enumeration— PART II: <strong>Exploiting</strong> the Vo<strong>IP</strong> Network• Chapter 4: Vo<strong>IP</strong> Network Infrastructure Denial of Service• Chapter 5: Network Eavesdropping• Chapter 6: Network and Application Interception— PART III: Vo<strong>IP</strong> Session and Application <strong>Hacking</strong>• Chapter 11: Fuzzing Vo<strong>IP</strong>• Chapter 12: Disruption of Service• Chapter 13: Vo<strong>IP</strong> Signaling and Media Manipulation— PART IV: Social Threats• Chapter 14: SPAMMING/SPIT• Chapter 15: Vo<strong>IP</strong> Phishing