- Page 1 and 2:
When MacsGet HackedSarah Edwards@ia
- Page 3 and 4:
Current Threats:SuspiciousUseInside
- Page 5 and 6:
Current Threats:Imuler Hidden .app
- Page 7 and 8:
Current Threats:MacControl MS WordV
- Page 9 and 10:
Windows InvestigationsIncidentRespo
- Page 11 and 12:
Incident Response:MacQuisition by B
- Page 13 and 14:
Incident Response:MacResponse by AI
- Page 15 and 16:
Incident Response:System Informatio
- Page 17 and 18:
Incident Response:Network Data - Ro
- Page 19 and 20:
Incident Response:Open Files lsof!b
- Page 21 and 22:
Incident Response:Running Processes
- Page 23 and 24:
Incident Response:System Profileroo
- Page 25 and 26:
Memory Analysis:Volafox http://code
- Page 27 and 28:
Memory Analysis:Volafoxoompa@csh.ri
- Page 29 and 30:
Mac AutorunsWhat XPC Services Launc
- Page 31 and 32:
Autoruns:XPC Services Exampleoompa@
- Page 33 and 34:
Autoruns:Launch Agents Agent - Back
- Page 35 and 36:
Autoruns:Launch Agents Examplesoomp
- Page 37 and 38:
Autoruns:Launch Daemons Daemon - Ba
- Page 39 and 40:
Autoruns:LoginItems Launched when u
- Page 41 and 42:
Autoruns:Deprecated Methods/etc/cro
- Page 43 and 44:
Internet HistoryWhat Browsers Safar
- Page 45 and 46:
Internet History:Safari - Downloads
- Page 47 and 48:
Internet History:Safari - Last Sess
- Page 49 and 50:
Internet History:Chrome - Internet
- Page 51 and 52:
Internet History:Chrome - Cache ~/L
- Page 53 and 54:
Internet History:FireFox - Cache ~/
- Page 55 and 56:
Email:Apple Mail ~/Library/Mail/V2/
- Page 57 and 58:
Email:Apple Mail - Attachments“Qu
- Page 59 and 60:
Temp & Cache Directories:Java Temp
- Page 61 and 62: Java Temp & Cache:IDX File Contents
- Page 64 and 65: Log Analysis:Apple System Logs Loca
- Page 66 and 67: Log Analysis:Console.appoompa@csh.r
- Page 68 and 69: Log Analysis:syslog -T utc -F raw -
- Page 70 and 71: Log Analysis:praudit -xn /var/audit
- Page 72 and 73: Log Analysismonthly.out Account Aud
- Page 74 and 75: Log Analysis:Account CreationAudit
- Page 76 and 77: Log Analysis:install.logMay 27 11:5
- Page 78 and 79: Volume AnalysisWhat Log Files MRU F
- Page 80 and 81: Volume Analysis:kernel.log Search f
- Page 82 and 83: Volume Analysis:com.apple.finder.pl
- Page 84 and 85: Antivirus:File Quarantine Introduce
- Page 86 and 87: Antivirus:File Quarantine EventsLio
- Page 88 and 89: Antivirus:Extended AttributesComman
- Page 90 and 91: Antivirus:XProtect /System/Library/
- Page 92 and 93: Antivirus:GateKeeper 10.8 - Mountai
- Page 94 and 95: Anti-ForensicsWhat Encryption Optim
- Page 96 and 97: Anti-forensics:Other Encryption App
- Page 98 and 99: Other FilesWhat Kernel Extensions B
- Page 100 and 101: Other Files:CommandUsageBash Histor
- Page 102 and 103: Other Files:Application HookingFlas
- Page 104 and 105: Basic Reverse EngineeringWhat Basic
- Page 106 and 107: Basic Reverse Engineering:Static: l
- Page 108 and 109: Basic Reverse Engineering:Static: o
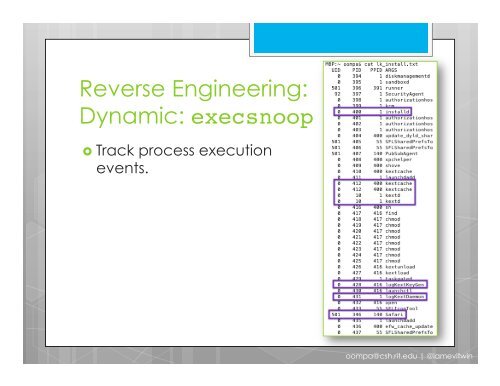
- Page 110 and 111: Basic Reverse Engineering:Dynamic:
- Page 114: When MacsGet HackedSarah Edwards@ia