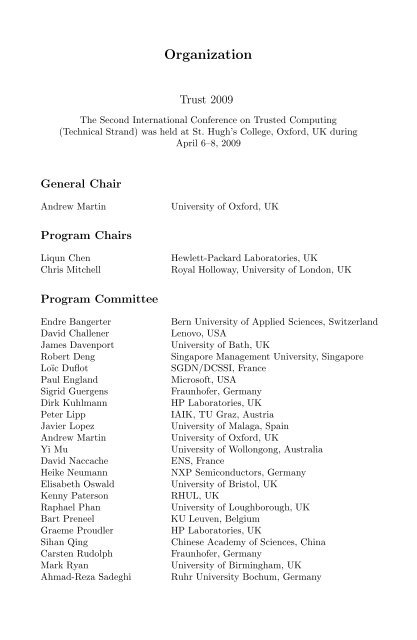
- Page 2 and 3: Liqun Chen Chris J. MitchellAndrew
- Page 6 and 7: VIIIOrganizationJean-Pierre Seifert
- Page 8: XTable of ContentsTrustable Remote
- Page 11: Towards a Programmable TPM 3Count-L
- Page 16 and 17: 8 P. England and T. Tariqperforms t
- Page 18 and 19: 10 P. England and T. Tariq3) Valida
- Page 20 and 21: 12 P. England and T. TariqUnfortuna
- Page 22 and 23: ACPI: Design Principles and Concern
- Page 24 and 25: 16 L. Duflot, O. Levillain, and B.
- Page 26 and 27: 18 L. Duflot, O. Levillain, and B.
- Page 28 and 29: 20 L. Duflot, O. Levillain, and B.
- Page 30 and 31: 22 L. Duflot, O. Levillain, and B.
- Page 32 and 33: 24 L. Duflot, O. Levillain, and B.
- Page 34 and 35: 26 L. Duflot, O. Levillain, and B.
- Page 36 and 37: 28 L. Duflot, O. Levillain, and B.
- Page 38 and 39: 30 K. Dietrich and J. Winterassumpt
- Page 40 and 41: 32 K. Dietrich and J. Wintercommand
- Page 42 and 43: 34 K. Dietrich and J. WinterThe har
- Page 44 and 45: 36 K. Dietrich and J. WinterThe act
- Page 46 and 47: 38 K. Dietrich and J. WinterMany ca
- Page 48 and 49: 40 K. Dietrich and J. Wintermechani
- Page 50 and 51: 42 K. Dietrich and J. Winteruntrust
- Page 52 and 53: 44 K. Dietrich and J. Winter8. Trus
- Page 54 and 55:
46 H. Löhr et al.on a very low lev
- Page 56 and 57:
48 H. Löhr et al.been modified, an
- Page 58 and 59:
50 H. Löhr et al.of HASK-PP is mor
- Page 60 and 61:
52 H. Löhr et al.A security kernel
- Page 62 and 63:
54 H. Löhr et al.Fig. 3. Overview
- Page 64 and 65:
56 H. Löhr et al.Definition 1 (Sec
- Page 66 and 67:
58 H. Löhr et al.the protected dat
- Page 68 and 69:
60 H. Löhr et al.5. Kurth, H., Kru
- Page 70 and 71:
62 H. Löhr et al.Table 1. Security
- Page 72 and 73:
64 M. Nauman et al.strength lies in
- Page 74 and 75:
66 M. Nauman et al.platform, we cre
- Page 76 and 77:
68 M. Nauman et al.Using these stru
- Page 78 and 79:
70 M. Nauman et al.Fig. 2. Remote A
- Page 80 and 81:
72 M. Nauman et al.INITs1.a:o1.a:s1
- Page 82 and 83:
74 M. Nauman et al.{ delete }s 3{ p
- Page 84 and 85:
76 M. Nauman et al.Algorithm 1. Inf
- Page 86 and 87:
78 M. Nauman et al.6 Conclusion and
- Page 88 and 89:
80 M. Nauman et al.21. Haldar, V.,
- Page 90 and 91:
82 F. Baiardi et al.the integrity o
- Page 92 and 93:
84 F. Baiardi et al.without receivi
- Page 94 and 95:
86 F. Baiardi et al.1. granular che
- Page 96 and 97:
88 F. Baiardi et al.- the VMM is tr
- Page 98 and 99:
90 F. Baiardi et al.be periodically
- Page 100 and 101:
92 F. Baiardi et al.Table 1. Exampl
- Page 102 and 103:
94 F. Baiardi et al.Fig. 2. Attesta
- Page 104 and 105:
96 F. Baiardi et al.• an elapsed
- Page 106 and 107:
98 F. Baiardi et al.(a)(b)Fig. 6. H
- Page 108 and 109:
100 F. Baiardi et al.16. Loscocco,
- Page 110 and 111:
102 M. Pirker et al.actually be tru
- Page 112 and 113:
104 M. Pirker et al.Fig. 1. Overvie
- Page 114 and 115:
106 M. Pirker et al.Guideline 3. Us
- Page 116 and 117:
108 M. Pirker et al.not stipulate a
- Page 118 and 119:
110 M. Pirker et al.4.1 TCcertAs ou
- Page 120 and 121:
112 M. Pirker et al.supplies an EK
- Page 122 and 123:
114 M. Pirker et al.Table 1. Overvi
- Page 124 and 125:
116 M. Pirker et al.[12] µ-kernel,
- Page 126 and 127:
118 M. Pirker et al.13. Housley, R.
- Page 128 and 129:
Revocation of TPM KeysStefan Katzen
- Page 130 and 131:
122 S. Katzenbeisser, K. Kursawe, a
- Page 132 and 133:
124 S. Katzenbeisser, K. Kursawe, a
- Page 134 and 135:
126 S. Katzenbeisser, K. Kursawe, a
- Page 136 and 137:
128 S. Katzenbeisser, K. Kursawe, a
- Page 138 and 139:
130 S. Katzenbeisser, K. Kursawe, a
- Page 140 and 141:
132 S. Katzenbeisser, K. Kursawe, a
- Page 142 and 143:
134 T.E. Levin et al.In this paper,
- Page 144 and 145:
136 T.E. Levin et al.used — Devic
- Page 146 and 147:
138 T.E. Levin et al.4 New Security
- Page 148 and 149:
140 T.E. Levin et al.providers, a s
- Page 150 and 151:
142 T.E. Levin et al.Fig. 5. Data F
- Page 152 and 153:
144 T.E. Levin et al.overwriting th
- Page 154 and 155:
146 T.E. Levin et al.services, they
- Page 156 and 157:
148 T.E. Levin et al.6.1 Prototype
- Page 158 and 159:
150 T.E. Levin et al.8 ConclusionsT
- Page 160 and 161:
152 T.E. Levin et al.24. Xen User
- Page 162 and 163:
154 J. Lyle2 Background, Definition
- Page 164 and 165:
156 J. Lyleachieve with web service
- Page 166 and 167:
158 J. Lyle Fig. 2. An overview o
- Page 168 and 169:
160 J. LyleSun JDK are used as the
- Page 170 and 171:
162 J. Lyleinput. Essentially, any
- Page 172 and 173:
164 J. Lyle(TVM) to attest to high-
- Page 174 and 175:
166 J. LyleCert B0Pre: ...Post: Q o
- Page 176 and 177:
168 J. Lyle11. Necula, G.: Proof-Ca
- Page 178 and 179:
170 J.H. Huh and J. LyleThe rest of
- Page 180 and 181:
172 J.H. Huh and J. Lylelogs have b
- Page 182 and 183:
174 J.H. Huh and J. Lyleanonymisati
- Page 184 and 185:
176 J.H. Huh and J. LyleCT =(PCR AI
- Page 186 and 187:
178 J.H. Huh and J. LyleFig. 4. Sub
- Page 188 and 189:
180 J.H. Huh and J. LyleTable 1. Tr
- Page 190 and 191:
182 J.H. Huh and J. Lyle11. Ng, H.-
- Page 192 and 193:
184 S. Türpe et al.to withstand at
- Page 194 and 195:
186 S. Türpe et al.- The attacker
- Page 196 and 197:
188 S. Türpe et al.Copy the entire
- Page 198 and 199:
190 S. Türpe et al.Requirements. R
- Page 200 and 201:
192 S. Türpe et al.No trusted path
- Page 202 and 203:
194 S. Türpe et al.Fig. 1. Spoofed
- Page 204 and 205:
196 S. Türpe et al.References1. Mi
- Page 206 and 207:
198 S. Schulz and A.-R. Sadeghicurr
- Page 208 and 209:
200 S. Schulz and A.-R. Sadeghitraf
- Page 210 and 211:
202 S. Schulz and A.-R. Sadeghi/S2/
- Page 212 and 213:
204 S. Schulz and A.-R. Sadeghiwith
- Page 214 and 215:
206 S. Schulz and A.-R. Sadeghichan
- Page 216 and 217:
208 S. Schulz and A.-R. Sadeghi/M1/
- Page 218 and 219:
210 S. Schulz and A.-R. Sadeghiip2i
- Page 220 and 221:
212 S. Schulz and A.-R. Sadeghiwill
- Page 222 and 223:
214 S. Schulz and A.-R. Sadeghi/S2/
- Page 224 and 225:
216 S. Schulz and A.-R. Sadeghi17.
- Page 226 and 227:
218 C. Soghoian and I. Aadbudget an
- Page 228 and 229:
220 C. Soghoian and I. Aadto tackle
- Page 230 and 231:
222 C. Soghoian and I. AadThe Conci
- Page 232 and 233:
224 C. Soghoian and I. Aad- Motivat
- Page 234 and 235:
226 C. Soghoian and I. AadFrom Merc
- Page 236 and 237:
228 C. Soghoian and I. AadConcierge
- Page 238 and 239:
230 C. Soghoian and I. Aadon giving
- Page 240 and 241:
232 C. Soghoian and I. AadProcessin
- Page 242 and 243:
234 C. Soghoian and I. Aadtransacti
- Page 244 and 245:
236 C. Soghoian and I. AadFurthermo
- Page 246 and 247:
238 C. Soghoian and I. AadReference
- Page 248 and 249:
A Property-Dependent Agent Transfer
- Page 250 and 251:
242 E. Gallery, A. Nagarajan, and V
- Page 252 and 253:
244 E. Gallery, A. Nagarajan, and V
- Page 254 and 255:
246 E. Gallery, A. Nagarajan, and V
- Page 256 and 257:
248 E. Gallery, A. Nagarajan, and V
- Page 258 and 259:
250 E. Gallery, A. Nagarajan, and V
- Page 260 and 261:
252 E. Gallery, A. Nagarajan, and V
- Page 262 and 263:
254 E. Gallery, A. Nagarajan, and V
- Page 264 and 265:
256 E. Gallery, A. Nagarajan, and V
- Page 266 and 267:
258 E. Gallery, A. Nagarajan, and V
- Page 268 and 269:
260 E. Gallery, A. Nagarajan, and V
- Page 270 and 271:
262 E. Gallery, A. Nagarajan, and V
- Page 272:
Author IndexAad, Imad 217Alam, Maso