- Page 3:
Internet CommunicationsUsing SIPSec
- Page 6 and 7:
Internet Communications Using SIP:
- Page 9:
About the AuthorsDr. Henry Sinnreic
- Page 13 and 14:
ContentsForewordAcknowledgmentsIntr
- Page 17:
ContentsxvCall Processing Language
- Page 20 and 21:
xviiiContentsTranscoding Services 2
- Page 23 and 24:
ForewordAbout 10 years ago, the fir
- Page 25 and 26:
AcknowledgmentsWe have enjoyed the
- Page 27 and 28:
IntroductionThe second edition of I
- Page 29 and 30:
Introduction xxviiRedefining Commun
- Page 33 and 34:
CHAPTER1IntroductionThe telecommuni
- Page 35 and 36:
Introduction 3CATEGORY WHO PROTOCOL
- Page 37 and 38:
Introduction 5Voice over IPAlthough
- Page 39 and 40:
Introduction 7The Short History of
- Page 41 and 42:
Introduction 9SIP-related drafts th
- Page 43 and 44:
CHAPTER2Internet CommunicationsEnab
- Page 45 and 46:
Internet Communications Enabled by
- Page 47 and 48:
Internet Communications Enabled by
- Page 49 and 50:
Internet Communications Enabled by
- Page 51 and 52:
Internet Communications Enabled by
- Page 53 and 54:
Internet Communications Enabled by
- Page 55 and 56:
Internet Communications Enabled by
- Page 57 and 58:
Internet Communications Enabled by
- Page 59 and 60:
Internet Communications Enabled by
- Page 61 and 62:
Internet Communications Enabled by
- Page 63 and 64:
Internet Communications Enabled by
- Page 65 and 66:
Internet Communications Enabled by
- Page 67 and 68:
Internet Communications Enabled by
- Page 69:
Internet Communications Enabled by
- Page 72 and 73:
40 Chapter 3Services supported byin
- Page 74 and 75:
Other IP NetworksPSTN/ISDN42 Chapte
- Page 76 and 77:
44 Chapter 3No single point of fail
- Page 78 and 79:
46 Chapter 3Table 3.1(continued)GUI
- Page 80 and 81:
48 Chapter 3The Internet Standards
- Page 82 and 83:
50 Chapter 3Wide Web is that the va
- Page 84 and 85:
52 Chapter 3SummaryThe emergence of
- Page 86 and 87:
54 Chapter 4Since the built-in DNS
- Page 88 and 89:
56 Chapter 4Tel URINo Internet devi
- Page 90 and 91:
58 Chapter 4locate an appropriate g
- Page 92 and 93:
60 Chapter 4The DNS is designed to
- Page 94 and 95:
62 Chapter 4Table 4.2(continued)The
- Page 96 and 97:
64 Chapter 4Following is the legend
- Page 98 and 99:
66 Chapter 4DNS ResolverSIPProxyor
- Page 100 and 101:
68 Chapter 4DO YOU REALLY HAVE VOIP
- Page 102 and 103:
70 Chapter 4We will describe here t
- Page 104 and 105:
72 Chapter 4■■■■■■Real-
- Page 106 and 107:
74 Chapter 4PBX Enterprise Voice Ne
- Page 108 and 109:
76 Chapter 4We notice here that the
- Page 110 and 111:
78 Chapter 4Data TamperingDuring th
- Page 112 and 113:
80 Chapter 4[7] “Uniform Resource
- Page 114 and 115:
82 Chapter 5■■■■■■Scali
- Page 116 and 117:
84 Chapter 5Table 5.1(continued)NAM
- Page 118 and 119:
86 Chapter 5IP UNICAST AND MULTICAS
- Page 120 and 121:
88 Chapter 5The description here of
- Page 122 and 123:
90 Chapter 5■■■■■■■
- Page 124 and 125:
92 Chapter 5■■■■■■Lost
- Page 126 and 127:
94 Chapter 5Authentication and Key
- Page 129 and 130:
CHAPTER6SIP OverviewIn this chapter
- Page 131 and 132:
SIP Overview 99FORKINGNETWORKPROXYI
- Page 133 and 134:
SIP Overview 101Watching How Sausag
- Page 135 and 136:
SIP Overview 103Table 6.1SIP Method
- Page 137 and 138:
SIP Overview 105Table 6.3(continued
- Page 139 and 140:
SIP Overview 107LOCATING SIP SERVER
- Page 141 and 142:
SIP Overview 109sends a set of ENUM
- Page 143 and 144:
SIP Overview 111TRANSPORT OF SIP ME
- Page 145 and 146:
SIP Overview 113Table 6.4LINESDP Of
- Page 147 and 148:
SIP Overview 115In the example of F
- Page 149 and 150:
SIP Overview 117A user agent receiv
- Page 151 and 152:
SIP Overview 119PSTN UserGatewayGat
- Page 153 and 154:
SIP Overview 121Preconditions For C
- Page 155 and 156:
SIP Overview 123SIP User AgentProxy
- Page 157 and 158:
SIP Overview 125A user agent can be
- Page 159 and 160:
SIP Overview 127between two user ag
- Page 161 and 162:
SIP Overview 129between the user ag
- Page 163 and 164:
SIP Overview 131There is also a Pro
- Page 165:
SIP Overview 133[16] “AAA Usage f
- Page 168 and 169:
136 Chapter 7services will include
- Page 170 and 171:
138 Chapter 7SIP CallerProxy Server
- Page 172 and 173:
140 Chapter 7The construction of th
- Page 174 and 175:
142 Chapter 7listing supported meth
- Page 176 and 177:
144 Chapter 7Table 7.2TAGcplCPL Tag
- Page 178 and 179:
146 Chapter 7Example of CPL Scripts
- Page 180 and 181:
148 Chapter 7SIP CGI is an interfac
- Page 182 and 183:
150 Chapter 7In this example, the s
- Page 185 and 186:
CHAPTER8User PreferencesAny advance
- Page 187 and 188:
User Preferences 155The instruction
- Page 189 and 190:
User Preferences 157Preferences of
- Page 191 and 192:
CHAPTER9SIP SecurityThe Security Co
- Page 193 and 194:
SIP Security 161Presence and IMThe
- Page 195 and 196:
SIP Security 163SIP can also use ce
- Page 197 and 198:
SIP Security 165Confidentiality can
- Page 199 and 200:
SIP Security 167optional feature wi
- Page 201 and 202:
SIP Security 169DTLSThe Datagram TL
- Page 203:
SIP Security 171[17] “Datagram Tr
- Page 206 and 207:
174 Chapter 10■■■■Modificat
- Page 208 and 209:
176 Chapter 10SIP User Agent A1. IN
- Page 210 and 211:
178 Chapter 10SIP User Agent AFirew
- Page 212 and 213:
180 Chapter 10result, these STUN pa
- Page 214 and 215:
182 Chapter 10back to the IP addres
- Page 216 and 217:
184 Chapter 10SummaryNAT and firewa
- Page 218 and 219:
186 Chapter 11There are two basic a
- Page 220 and 221:
188 Chapter 11in a gateway involves
- Page 222 and 223:
190 Chapter 11would generate it. Th
- Page 224 and 225:
192 Chapter 11The IAM can be mapped
- Page 226 and 227:
194 Chapter 11Call-ID: 12345602@ngw
- Page 228 and 229:
196 Chapter 11Enhanced Telephony Se
- Page 230 and 231:
198 Chapter 11■■■■■■■
- Page 232 and 233:
200 Chapter 11A list of call scenar
- Page 234 and 235:
202 Chapter 11Following are example
- Page 236 and 237:
204 Chapter 11controller to the con
- Page 238 and 239:
206 Chapter 11SIP servers that norm
- Page 241 and 242:
CHAPTER12Voicemail and UniversalMes
- Page 243 and 244:
Voicemail and Universal Messaging 2
- Page 245 and 246:
Voicemail and Universal Messaging 2
- Page 247 and 248:
Voicemail and Universal Messaging 2
- Page 249 and 250:
Voicemail and Universal Messaging 2
- Page 251 and 252:
Voicemail and Universal Messaging 2
- Page 253 and 254:
Voicemail and Universal Messaging 2
- Page 255 and 256:
CHAPTER13Presence andInstant Messag
- Page 257 and 258:
Presence and Instant Messaging 225T
- Page 259 and 260:
Presence and Instant Messaging 227A
- Page 261 and 262:
Presence and Instant Messaging 229C
- Page 263 and 264:
Presence and Instant Messaging 231
- Page 265 and 266: Presence and Instant Messaging 233N
- Page 267 and 268: Presence and Instant Messaging 235T
- Page 269 and 270: Presence and Instant Messaging 237
- Page 271 and 272: Presence and Instant Messaging 239S
- Page 273 and 274: Presence and Instant Messaging 241M
- Page 275: Presence and Instant Messaging 243[
- Page 278 and 279: 246 Chapter 14■■So-called Web C
- Page 280 and 281: 248 Chapter 14Each conference model
- Page 282 and 283: 250 Chapter 14for moving existing p
- Page 284 and 285: 252 Chapter 14[8] “The Session In
- Page 286 and 287: 254 Chapter 15■■■■■■tho
- Page 288 and 289: 256 Chapter 15Table 15.1(continued)
- Page 290 and 291: 258 Chapter 15RoamingUser(Callee)DH
- Page 292 and 293: 260 Chapter 15alice@example.comReac
- Page 294 and 295: 262 Chapter 15SIP Mobility2WISPInte
- Page 296 and 297: 264 Chapter 152 - Datagram is tunne
- Page 298 and 299: 266 Chapter 15Figure 15.8 SIP user
- Page 300 and 301: 268 Chapter 15The elements in the I
- Page 302 and 303: 270 Chapter 15Different credentials
- Page 305 and 306: CHAPTER16Emergency and PreemptionCo
- Page 307 and 308: Emergency and Preemption Communicat
- Page 309 and 310: Emergency and Preemption Communicat
- Page 311 and 312: Emergency and Preemption Communicat
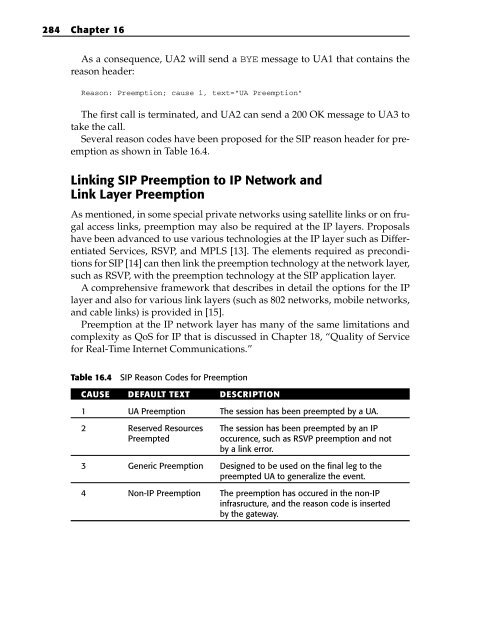
- Page 313 and 314: Emergency and Preemption Communicat
- Page 315: Emergency and Preemption Communicat
- Page 319 and 320: CHAPTER17Accessibility forthe Disab
- Page 321 and 322: Accessibility for the Disabled 289R
- Page 323 and 324: Accessibility for the Disabled 291
- Page 325 and 326: Accessibility for the Disabled 293
- Page 327 and 328: Accessibility for the Disabled 295N
- Page 329 and 330: Accessibility for the Disabled 297H
- Page 331: Accessibility for the Disabled 299I
- Page 334 and 335: 302 Chapter 18MR. QOS VS. MR. BANDW
- Page 336 and 337: 304 Chapter 18Some wireless SIP bas
- Page 338 and 339: 306 Chapter 18A comparison of the I
- Page 340 and 341: 308 Chapter 18The Endpoint Quality
- Page 342 and 343: 310 Chapter 18Global Resonse Time (
- Page 344 and 345: 312 Chapter 18Table 18.2(continued)
- Page 346 and 347: 314 Chapter 18Monitoring QoS for Re
- Page 348 and 349: 316 Chapter 18[8] “RTP Payload Fo
- Page 350 and 351: 318 Chapter 19“softswitch” in q
- Page 352 and 353: 320 Chapter 19New features in the s
- Page 354 and 355: 322 Chapter 19enterprise networks.
- Page 356 and 357: 324 Chapter 19■■■■■■■
- Page 358 and 359: 326 Chapter 19The architecture is c
- Page 360 and 361: 328 Chapter 19The cause parameters
- Page 362 and 363: 330 Chapter 19Collecting DTMF Digit
- Page 364 and 365: 332 Chapter 19The controller then i
- Page 366 and 367:
334 Chapter 19CALLER CONTROLLER IVR
- Page 368 and 369:
336 Chapter 19WEBA BSCHEDULER MIXER
- Page 371 and 372:
CHAPTER20Peer-to-Peer SIPPeer-to-pe
- Page 373 and 374:
Peer-to-Peer SIP 341ApplicationTran
- Page 375 and 376:
Peer-to-Peer SIP 343In a DHT, the h
- Page 377 and 378:
Peer-to-Peer SIP 3452. A significan
- Page 379 and 380:
Peer-to-Peer SIP 347DNSSRV & Aqueri
- Page 381 and 382:
Peer-to-Peer SIP 349■■■■■
- Page 383 and 384:
Peer-to-Peer SIP 351same features a
- Page 385 and 386:
CHAPTER21Conclusions and FutureDire
- Page 387 and 388:
Conclusions and Future Directions 3
- Page 389 and 390:
IndexSYMBOLS AND NUMERICS!DOCTYPE h
- Page 391 and 392:
Index 359bridges, conferencing, 247
- Page 393 and 394:
Index 361text phones, 296transcodin
- Page 395 and 396:
Index 363gatewaysALGs, 173, 180-183
- Page 397 and 398:
Index 365Internet Engineering Task
- Page 399 and 400:
Index 367text-based, 209transport,
- Page 401 and 402:
Index 369peer-to-peer traffic, 14,
- Page 403 and 404:
Index 371reason headers, SIP, 282-2
- Page 405 and 406:
Index 373disrupting, 160, 161modify
- Page 407 and 408:
Index 375quality, 302, 303-305, 308
- Page 409:
Index 377web conferencing, 246web s