Hack.lu edition 2012 A forensic analysis of Android Malware
Hack.lu edition 2012 A forensic analysis of Android Malware
Hack.lu edition 2012 A forensic analysis of Android Malware
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
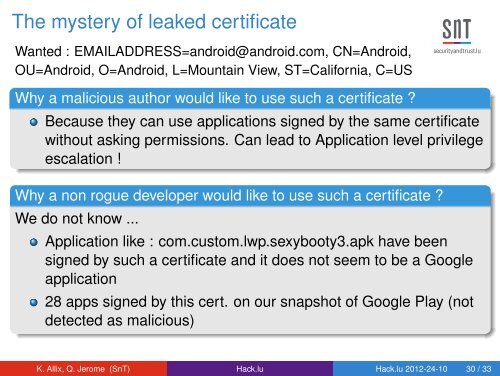
The mystery <strong>of</strong> leaked certificateWanted : EMAILADDRESS=android@android.com, CN=<strong>Android</strong>,OU=<strong>Android</strong>, O=<strong>Android</strong>, L=Mountain View, ST=California, C=USWhy a malicious author would like to use such a certificate ?Because they can use applications signed by the same certificatewithout asking permissions. Can lead to Application level privilegeescalation !Why a non rogue developer would like to use such a certificate ?We do not know ...Application like : com.custom.lwp.sexybooty3.apk have beensigned by such a certificate and it does not seem to be a Googleapplication28 apps signed by this cert. on our snapshot <strong>of</strong> Google Play (notdetected as malicious)K. Allix, Q. Jerome (SnT) <strong>Hack</strong>.<strong>lu</strong> <strong>Hack</strong>.<strong>lu</strong> <strong>2012</strong>-24-10 30 / 33