Wendell Crenshaw Technologies presents
Outline
Outline
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
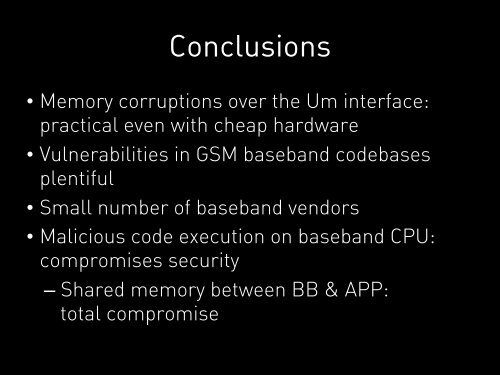
Conclusions• Memory corruptions over the Um interface:practical even with cheap hardware• Vulnerabilities in GSM baseband codebasesplentiful• Small number of baseband vendors• Malicious code execution on baseband CPU:compromises security– Shared memory between BB & APP:total compromise