CFC REPORT SPHINX MOTH
1WLUwDt
1WLUwDt
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
<strong>CFC</strong> <strong>REPORT</strong>: <strong>SPHINX</strong> <strong>MOTH</strong><br />
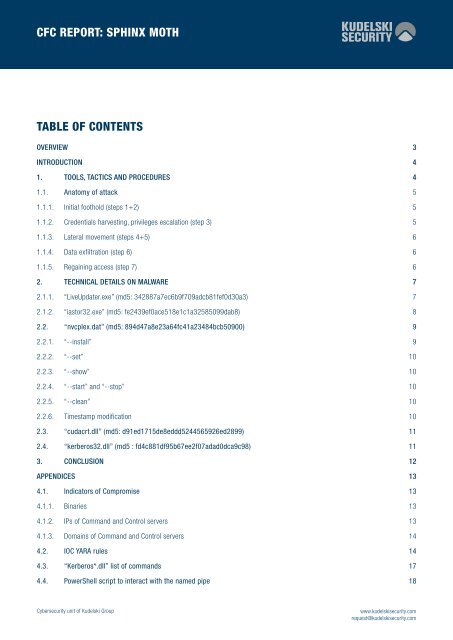
TABLE OF CONTENTS<br />
OVERVIEW 3<br />
INTRODUCTION 4<br />
1. TOOLS, TACTICS AND PROCEDURES 4<br />
1.1. Anatomy of attack 5<br />
1.1.1. Initial foothold (steps 1+2) 5<br />
1.1.2. Credentials harvesting, privileges escalation (step 3) 5<br />
1.1.3. Lateral movement (steps 4+5) 6<br />
1.1.4. Data exfiltration (step 6) 6<br />
1.1.5. Regaining access (step 7) 6<br />
2. TECHNICAL DETAILS ON MALWARE 7<br />
2.1.1. “LiveUpdater.exe” (md5: 342887a7ec6b9f709adcb81fef0d30a3) 7<br />
2.1.2. “iastor32.exe” (md5: fe2439ef0ace518e1c1a32585099dab8) 8<br />
2.2. “nvcplex.dat” (md5: 894d47a8e23a64fc41a23484bcb50900) 9<br />
2.2.1. “--install” 9<br />
2.2.2. “--set” 10<br />
2.2.3. “--show” 10<br />
2.2.4. “--start” and “--stop” 10<br />
2.2.5. “--clean” 10<br />
2.2.6. Timestamp modification 10<br />
2.3. “cudacrt.dll” (md5: d91ed1715de8eddd5244565926ed2899) 11<br />
2.4. “kerberos32.dll” (md5 : fd4c881df95b67ee2f07adad0dca9c98) 11<br />
3. CONCLUSION 12<br />
APPENDICES 13<br />
4.1. Indicators of Compromise 13<br />
4.1.1. Binaries 13<br />
4.1.2. IPs of Command and Control servers 13<br />
4.1.3. Domains of Command and Control servers 14<br />
4.2. IOC YARA rules 14<br />
4.3. “Kerberos*.dll” list of commands 17<br />
4.4. PowerShell script to interact with the named pipe 18<br />
Cybersecurity unit of Kudelski Group<br />
www.kudelskisecurity.com<br />
request@kudelskisecurity.com