F5 SSL Everywhere
3ztjr
3ztjr
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
RECOMMENDED PRACTICES<br />
<strong>F5</strong> <strong>SSL</strong> <strong>Everywhere</strong><br />
How all the clients got their certificates is a management problem all in itself. Typically all<br />
the clients are members of a well-funded organization (like a branch of the military) or Wall<br />
Street traders, for instance. And often the certificates reside on smart cards or other<br />
devices where they are accessed over public key cryptography standard (PKCS) protocol<br />
#11.<br />
Part 8 of the DevCentral series on <strong>SSL</strong> profiles provides a detailed breakdown of exactly<br />
how client certificate authentication works within the TLS handshake.<br />
Historically, the most common intersection of client certificate authentication and the <strong>F5</strong><br />
platform occurs in <strong>SSL</strong> termination and <strong>SSL</strong> bridging modes: the BIG-IP device is acting<br />
as the <strong>SSL</strong> server to a client on the Internet and authenticating that client’s certificate. The<br />
back-end servers, which trust the BIG-IP system, need to get information about the client<br />
certificate. There are three ways to forward that client certificate information to the servers:<br />
• X509 extraction<br />
The oldest trick (and still one of the easiest) is to extract and insert fields from the<br />
client certificate’s X509 directory information into the underlying HTTP stream as<br />
headers. A typical iRules script might include gathering the issuer of the client<br />
certificate and then inserting it into the HTTP request to the server as “<strong>F5</strong>_CLIENT_<br />
ISSUER=[X509::issuer [<strong>SSL</strong>::cert 0]]”. See this DevCentral post for a more complete<br />
example.<br />
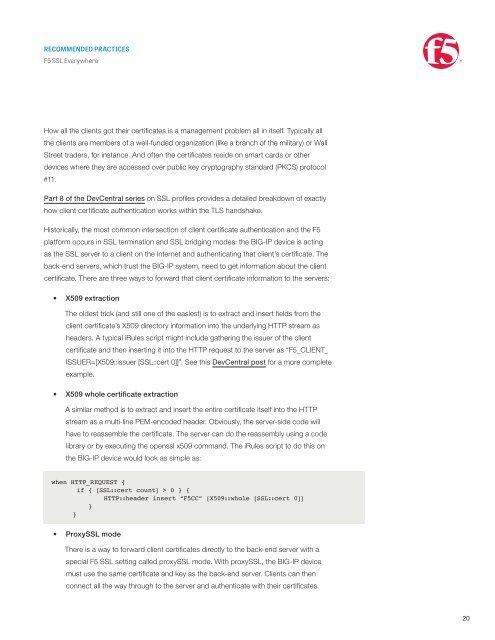
• X509 whole certificate extraction<br />
A similar method is to extract and insert the entire certificate itself into the HTTP<br />
stream as a multi-line PEM-encoded header. Obviously, the server-side code will<br />
have to reassemble the certificate. The server can do the reassembly using a code<br />
library or by executing the openssl x509 command. The iRules script to do this on<br />
the BIG-IP device would look as simple as:<br />
when HTTP_REQUEST {<br />
if { [<strong>SSL</strong>::cert count] > 0 } {<br />
HTTP::header insert “<strong>F5</strong>CC” [X509::whole [<strong>SSL</strong>::cert 0]]<br />
}<br />
}<br />
• Proxy<strong>SSL</strong> mode<br />
There is a way to forward client certificates directly to the back-end server with a<br />
special <strong>F5</strong> <strong>SSL</strong> setting called proxy<strong>SSL</strong> mode. With proxy<strong>SSL</strong>, the BIG-IP device<br />
must use the same certificate and key as the back-end server. Clients can then<br />
connect all the way through to the server and authenticate with their certificates.<br />
20