ASERT-Threat-Intelligence-Report-2016-03-The-Four-Element-Sword-Engagement
ASERT-Threat-Intelligence-Report-2016-03-The-Four-Element-Sword-Engagement
ASERT-Threat-Intelligence-Report-2016-03-The-Four-Element-Sword-Engagement
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
<strong>ASERT</strong> <strong>Threat</strong> <strong>Intelligence</strong> <strong>Report</strong> <strong>2016</strong>-<strong>03</strong>: <strong>The</strong> <strong>Four</strong>-<strong>Element</strong> <strong>Sword</strong> <strong>Engagement</strong><br />
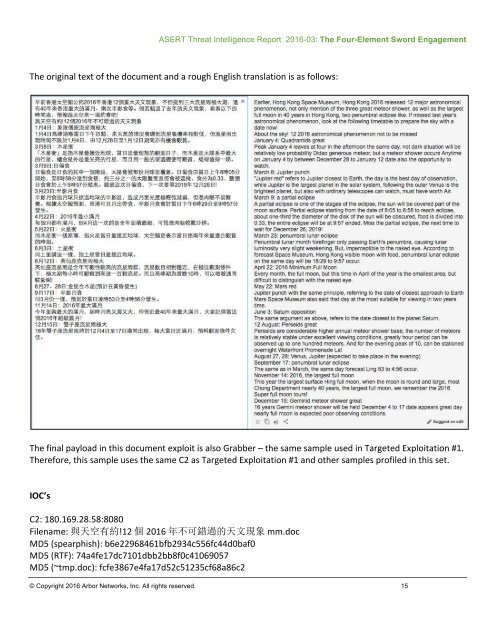
<strong>The</strong> original text of the document and a rough English translation is as follows: <br />
<strong>The</strong> final payload in this document exploit is also Grabber – the same sample used in Targeted Exploitation #1. <br />
<strong>The</strong>refore, this sample uses the same C2 as Targeted Exploitation #1 and other samples profiled in this set. <br />
IOC’s <br />
C2: 180.169.28.58:8080 <br />
Filename: 與 天 空 有 約 !12 個 <strong>2016</strong> 年 不 可 錯 過 的 天 文 現 象 mm.doc <br />
MD5 (spearphish): b6e22968461bfb2934c556fc44d0baf0 <br />
MD5 (RTF): 74a4fe17dc7101dbb2bb8f0c41069057 <br />
MD5 (~tmp.doc): fcfe3867e4fa17d52c51235cf68a86c2 <br />
© Copyright <strong>2016</strong> Arbor Networks, Inc. All rights reserved. 15