DirectCertify 312-50 Latest Exam Brain Dumps
Get your future secure with our training kits of PDF questions answers which are verified and authorized by the experts and professionals regarding 312-50 Exam. For more info please visit here: http://www.directcertify.com/312-50.html
Get your future secure with our training kits of PDF questions answers which are verified and authorized by the experts and professionals regarding 312-50 Exam. For more info please visit here: http://www.directcertify.com/312-50.html
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
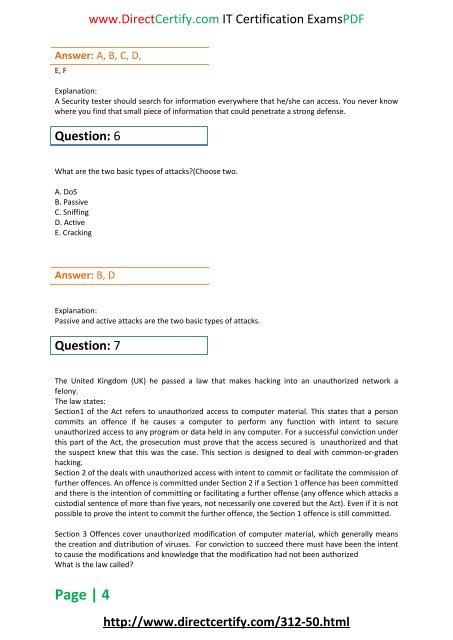
www.<strong>DirectCertify</strong>.com IT Certification <strong>Exam</strong>sPDF<br />
Answer: A, B, C, D,<br />
E, F<br />
Explanation:<br />
A Security tester should search for information everywhere that he/she can access. You never know<br />
where you find that small piece of information that could penetrate a strong defense.<br />
Question: 6<br />
What are the two basic types of attacks?(Choose two.<br />
A. DoS<br />
B. Passive<br />
C. Sniffing<br />
D. Active<br />
E. Cracking<br />
Answer: B, D<br />
Explanation:<br />
Passive and active attacks are the two basic types of attacks.<br />
Question: 7<br />
The United Kingdom (UK) he passed a law that makes hacking into an unauthorized network a<br />
felony.<br />
The law states:<br />
Section1 of the Act refers to unauthorized access to computer material. This states that a person<br />
commits an offence if he causes a computer to perform any function with intent to secure<br />
unauthorized access to any program or data held in any computer. For a successful conviction under<br />
this part of the Act, the prosecution must prove that the access secured is unauthorized and that<br />
the suspect knew that this was the case. This section is designed to deal with common-or-graden<br />
hacking.<br />
Section 2 of the deals with unauthorized access with intent to commit or facilitate the commission of<br />
further offences. An offence is committed under Section 2 if a Section 1 offence has been committed<br />
and there is the intention of committing or facilitating a further offense (any offence which attacks a<br />
custodial sentence of more than five years, not necessarily one covered but the Act). Even if it is not<br />
possible to prove the intent to commit the further offence, the Section 1 offence is still committed.<br />
Section 3 Offences cover unauthorized modification of computer material, which generally means<br />
the creation and distribution of viruses. For conviction to succeed there must have been the intent<br />
to cause the modifications and knowledge that the modification had not been authorized<br />
What is the law called?<br />
Page | 4<br />
http://www.directcertify.com/<strong>312</strong>-<strong>50</strong>.html