Security Architecture of BIND 9
20160520-janog-us-2-jinmei
20160520-janog-us-2-jinmei
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
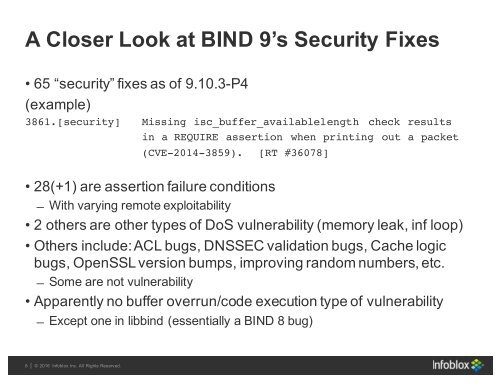
A Closer Look at <strong>BIND</strong> 9’s <strong>Security</strong> Fixes<br />
• 65 “security” fixes as <strong>of</strong> 9.10.3-P4<br />
(example)<br />
3861.[security] Missing isc_buffer_availablelength check results<br />
in a REQUIRE assertion when printing out a packet<br />
(CVE-2014-3859). [RT #36078]<br />
• 28(+1) are assertion failure conditions<br />
̶ With varying remote exploitability<br />
• 2 others are other types <strong>of</strong> DoS vulnerability (memory leak, inf loop)<br />
• Others include: ACL bugs, DNSSEC validation bugs, Cache logic<br />
bugs, OpenSSL version bumps, improving random numbers, etc.<br />
̶ Some are not vulnerability<br />
• Apparently no buffer overrun/code execution type <strong>of</strong> vulnerability<br />
̶ Except one in libbind (essentially a <strong>BIND</strong> 8 bug)<br />
8 | | © 2016 2013 Infoblox Infoblox Inc. All Inc. Rights All Reserved. Rights Reserved.