CYBER RESILIENCE HOW TO PROTECT SMALL FIRMS IN THE DIGITAL ECONOMY
FSB-Cyber-Resilience-report-2016
FSB-Cyber-Resilience-report-2016
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
fsb.org.uk<br />
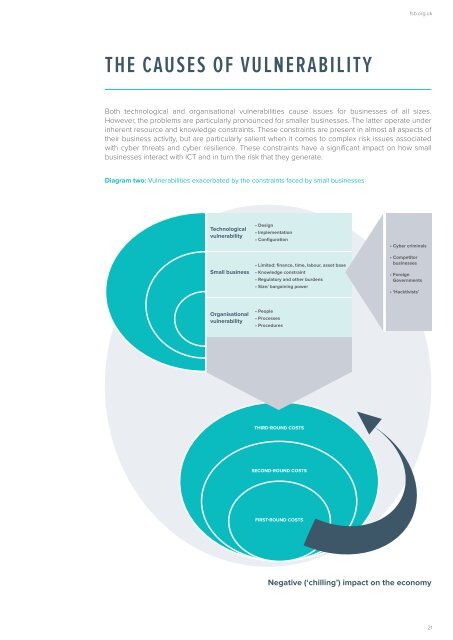
<strong>THE</strong> CAUSES OF VULNERABILITY<br />
Both technological and organisational vulnerabilities cause issues for businesses of all sizes.<br />
However, the problems are particularly pronounced for smaller businesses. The latter operate under<br />
inherent resource and knowledge constraints. These constraints are present in almost all aspects of<br />
their business activity, but are particularly salient when it comes to complex risk issues associated<br />
with cyber threats and cyber resilience. These constraints have a significant impact on how small<br />
businesses interact with ICT and in turn the risk that they generate.<br />
Diagram two: Vulnerabilities exacerbated by the constraints faced by small businesses<br />
Technological<br />
vulnerability<br />
Small business<br />
• Design<br />
• Implementation<br />
• Configuration<br />
• Limited: finance, time, labour, asset base<br />
• Knowledge constraint<br />
• Regulatory and other burdens<br />
• Size/ bargaining power<br />
• Cyber criminals<br />
• Competitor<br />
businesses<br />
• Foreign<br />
Governments<br />
• ‘Hacktivists’<br />
Organisational<br />
vulnerability<br />
• People<br />
• Processes<br />
• Procedures<br />
THIRD-ROUND COSTS<br />
SECOND-ROUND COSTS<br />
FIRST-ROUND COSTS<br />
Negative (‘chilling’) impact on the economy<br />
21