sqs-dg-2009-02-01
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Amazon Simple Queue Service Developer Guide<br />
HMAC-SHA Signatures<br />
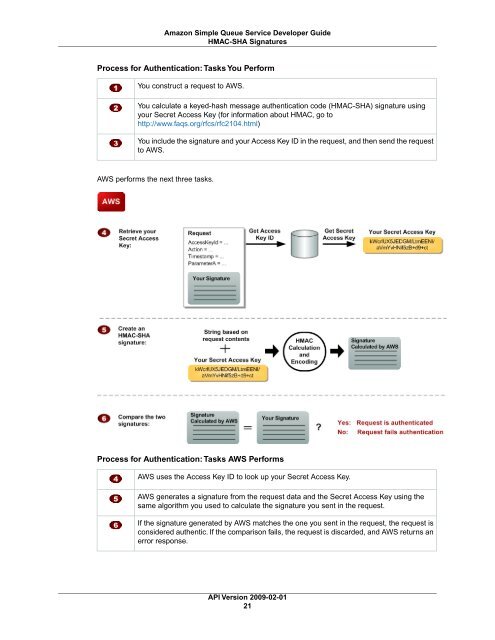
Process for Authentication: Tasks You Perform<br />
You construct a request to AWS.<br />
You calculate a keyed-hash message authentication code (HMAC-SHA) signature using<br />
your Secret Access Key (for information about HMAC, go to<br />
http://www.faqs.org/rfcs/rfc2104.html)<br />
You include the signature and your Access Key ID in the request, and then send the request<br />
to AWS.<br />
AWS performs the next three tasks.<br />
Process for Authentication: Tasks AWS Performs<br />
AWS uses the Access Key ID to look up your Secret Access Key.<br />
AWS generates a signature from the request data and the Secret Access Key using the<br />
same algorithm you used to calculate the signature you sent in the request.<br />
If the signature generated by AWS matches the one you sent in the request, the request is<br />
considered authentic. If the comparison fails, the request is discarded, and AWS returns an<br />
error response.<br />
API Version <strong>2009</strong>-<strong>02</strong>-<strong>01</strong><br />
21