Cyber Handbook-Enterprise v1.6
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
ACCREDITED. FLEXIBLE. ONLINE.<br />
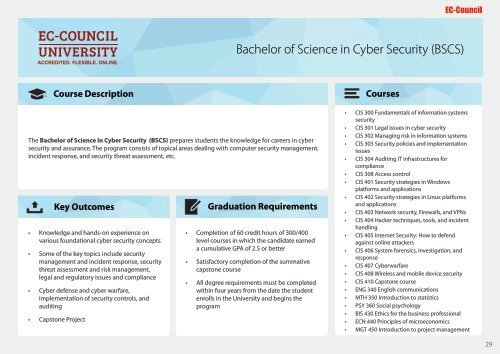
Bachelor of Science in <strong>Cyber</strong> Security (BSCS)<br />
Course Description<br />
Courses<br />
Outline<br />
The Bachelor of Science in <strong>Cyber</strong> Security (BSCS) prepares students the knowledge for careers in cyber<br />
security and assurance. The program consists of topical areas dealing with computer security management,<br />
incident response, and security threat assessment, etc.<br />
Key Outcomes<br />
• Knowledge and hands-on experience on<br />
various foundational cyber security concepts<br />
• Some of the key topics include security<br />
management and incident response, security<br />
threat assessment and risk management,<br />
legal and regulatory issues and compliance<br />
• <strong>Cyber</strong> defense and cyber warfare,<br />
implementation of security controls, and<br />
auditing<br />
• Capstone Project<br />
Graduation Exam Information Requirements<br />
• Completion of 60 credit hours of 300/400<br />
level courses in which the candidate earned<br />
a cumulative GPA of 2.5 or better<br />
• Satisfactory completion of the summative<br />
capstone course<br />
• All degree requirements must be completed<br />
within four years from the date the student<br />
enrolls in the University and begins the<br />
program<br />
• CIS 300 Fundamentals of information systems<br />
security<br />
• CIS 301 Legal issues in cyber security<br />
• CIS 302 Managing risk in information systems<br />
• CIS 303 Security policies and implementation<br />
issues<br />
• CIS 304 Auditing IT infrastructures for<br />
compliance<br />
• CIS 308 Access control<br />
• CIS 401 Security strategies in Windows<br />
platforms and applications<br />
• CIS 402 Security strategies in Linux platforms<br />
and applications<br />
• CIS 403 Network security, Firewalls, and VPNs<br />
• CIS 404 Hacker techniques, tools, and incident<br />
handling<br />
• CIS 405 Internet Security: How to defend<br />
against online attackers<br />
• CIS 406 System forensics, investigation, and<br />
response<br />
• CIS 407 <strong>Cyber</strong>warfare<br />
• CIS 408 Wireless and mobile device security<br />
• CIS 410 Capstone course<br />
• ENG 340 English communications<br />
• MTH 350 Introduction to statistics<br />
• PSY 360 Social psychology<br />
• BIS 430 Ethics for the business professional<br />
• ECN 440 Principles of microeconomics<br />
• MGT 450 Introduction to project management<br />
29