1Y0-401 PDF Questions - Pass 1Y0-401 Exam via DumpsArchive Citrix 1Y0-401 Exam Questions
-- Visit here for more: https://dumpsarchive.com/dumps/1Y0-401/ -- -- Reasons to Use Citrix 1Y0-401 exam questions -- This is usually only possible with the aid of 1Y0-401 braindumps and listed below are the reasons why we believe you should opt to purchase the 1Y0-401 dumps pdf. -- Incomparable 1Y0-401 exam questions product Quality -- The 1Y0-401 exam dumps will save you time that you might otherwise have spent wasting trying to look up the 1Y0-401 dumps and studying on your own, all to no avail. Instead you can make life easier for yourself by opting the 1Y0-401 dumps pdf which has all the questions as they are coming in the Citrix 1Y0-401 Specialist exam along with the answers.
-- Visit here for more: https://dumpsarchive.com/dumps/1Y0-401/ --
-- Reasons to Use Citrix 1Y0-401 exam questions --
This is usually only possible with the aid of 1Y0-401 braindumps and listed below are the reasons why we believe you should opt to purchase the 1Y0-401 dumps pdf.
-- Incomparable 1Y0-401 exam questions product Quality --
The 1Y0-401 exam dumps will save you time that you might otherwise have spent wasting trying to look up the 1Y0-401 dumps and studying on your own, all to no avail.
Instead you can make life easier for yourself by opting the 1Y0-401 dumps pdf which has all the questions as they are coming in the Citrix 1Y0-401 Specialist exam along with the answers.
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
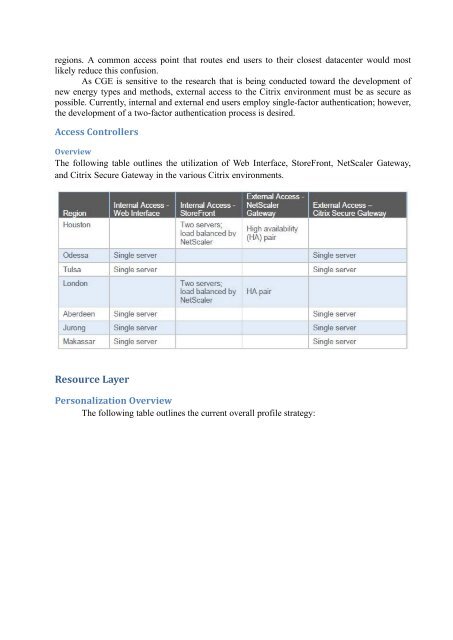
egions. A common access point that routes end users to their closest datacenter would most<br />
likely reduce this confusion.<br />
As CGE is sensitive to the research that is being conducted toward the development of<br />
new energy types and methods, external access to the <strong>Citrix</strong> environment must be as secure as<br />
possible. Currently, internal and external end users employ single-factor authentication; however,<br />
the development of a two-factor authentication process is desired.<br />
Access Controllers<br />
Overview<br />
The following table outlines the utilization of Web Interface, StoreFront, NetScaler Gateway,<br />
and <strong>Citrix</strong> Secure Gateway in the various <strong>Citrix</strong> environments.<br />
Resource Layer<br />
Personalization Overview<br />
The following table outlines the current overall profile strategy: