Cyber Defense eMagazine November 2019
Cyber Defense eMagazine November Edition for 2019 #CDM #CYBERDEFENSEMAG @CyberDefenseMag by @Miliefsky a world-renowned cyber security expert and the Publisher of Cyber Defense Magazine as part of the Cyber Defense Media Group
Cyber Defense eMagazine November Edition for 2019 #CDM #CYBERDEFENSEMAG @CyberDefenseMag by @Miliefsky a world-renowned cyber security expert and the Publisher of Cyber Defense Magazine as part of the Cyber Defense Media Group
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
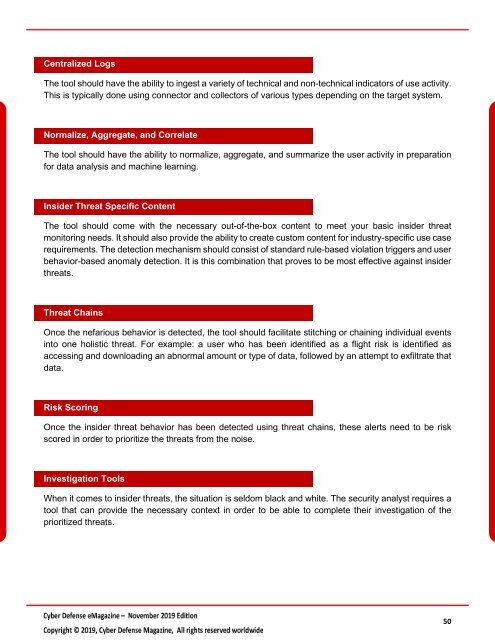
Centralized Logs<br />
The tool should have the ability to ingest a variety of technical and non-technical indicators of use activity.<br />
This is typically done using connector and collectors of various types depending on the target system.<br />
Normalize, Aggregate, and Correlate<br />
The tool should have the ability to normalize, aggregate, and summarize the user activity in preparation<br />
for data analysis and machine learning.<br />
Insider Threat Specific Content<br />
The tool should come with the necessary out-of-the-box content to meet your basic insider threat<br />
monitoring needs. It should also provide the ability to create custom content for industry-specific use case<br />
requirements. The detection mechanism should consist of standard rule-based violation triggers and user<br />
behavior-based anomaly detection. It is this combination that proves to be most effective against insider<br />
threats.<br />
Threat Chains<br />
Once the nefarious behavior is detected, the tool should facilitate stitching or chaining individual events<br />
into one holistic threat. For example: a user who has been identified as a flight risk is identified as<br />
accessing and downloading an abnormal amount or type of data, followed by an attempt to exfiltrate that<br />
data.<br />
Risk Scoring<br />
Once the insider threat behavior has been detected using threat chains, these alerts need to be risk<br />
scored in order to prioritize the threats from the noise.<br />
Investigation Tools<br />
When it comes to insider threats, the situation is seldom black and white. The security analyst requires a<br />
tool that can provide the necessary context in order to be able to complete their investigation of the<br />
prioritized threats.<br />
50