- Page 1 and 2:
1
- Page 3 and 4:
Contents Welcome to CDM’s RSAC 20
- Page 5 and 6:
CYBER DEFENSE MAGAZINE is a Cyber D
- Page 7 and 8:
7
- Page 9 and 10:
Regula Delivers Remote Identity Ver
- Page 11 and 12:
technology. Regula Document reader
- Page 13 and 14:
13
- Page 15 and 16:
approach to analyzing network activ
- Page 17 and 18:
What’s the architecture for a suc
- Page 19 and 20:
How Cobwebs Technologies' Webint Pl
- Page 21 and 22:
About the Author Udi Levy is the CE
- Page 23 and 24:
23
- Page 25 and 26:
Over the last few months, cybersecu
- Page 27 and 28:
Anomalous Value” alert. This will
- Page 29 and 30:
5. This incident at Oldsmar, highli
- Page 31 and 32:
The best part is that these solutio
- Page 33 and 34:
33
- Page 35 and 36:
Modern IT infrastructure is a méla
- Page 37 and 38:
A New Era of Malware Analysis By St
- Page 39 and 40:
A new way to get results faster and
- Page 41 and 42:
41
- Page 43 and 44:
ERP applications have historically
- Page 45 and 46:
About the Author My Name is Piyush
- Page 47 and 48:
Here at Axiad, we speak with custom
- Page 49 and 50:
Final thoughts In the age of digita
- Page 51 and 52:
51
- Page 53 and 54:
CIEM? Looks a lot like SIEM. CIEM m
- Page 55 and 56:
The Cloud Permissions Gap across an
- Page 57 and 58:
Transformation happens fast in toda
- Page 59 and 60:
59
- Page 61 and 62:
The Rise of Ransomware Understandin
- Page 63 and 64:
Consider the impact an attack like
- Page 65 and 66:
No other platform has ever been abl
- Page 67 and 68:
67
- Page 69 and 70:
The cybersecurity industry was a di
- Page 71 and 72:
Difenda Shield: A New Approach to a
- Page 73 and 74:
73
- Page 75 and 76:
priority — enabling remote workfo
- Page 77 and 78:
The cyber skills gap Every aspect o
- Page 79 and 80:
79
- Page 81 and 82:
For decades, security companies and
- Page 83 and 84:
83
- Page 85 and 86:
The Security Challenge of Democrati
- Page 87 and 88: We also asked if they are worried a
- Page 89 and 90: 89
- Page 91 and 92: The downside of this approach is th
- Page 93 and 94: Organizations can also pair Attivo
- Page 95 and 96: Evitoken Technology A New Way to Ke
- Page 97 and 98: physically located at the location
- Page 99 and 100: How to Become Unattractive for Cybe
- Page 101 and 102: 4. Shadow IT Shadow IT refers to th
- Page 103 and 104: Why XDR is Not Enough By Guy Rosefe
- Page 105 and 106: • XDR response is not granular No
- Page 107 and 108: Sangfor’s Award Winning XDDR Secu
- Page 109 and 110: 109
- Page 111 and 112: 111
- Page 113 and 114: Award Winners Welcome to the Cyber
- Page 115 and 116: Cyber Defense InfoSec Awards for 20
- Page 117 and 118: Cyber Defense InfoSec Awards for 20
- Page 119 and 120: Cyber Defense InfoSec Awards for 20
- Page 121 and 122: Cyber Defense InfoSec Awards for 20
- Page 123 and 124: Cyber Defense InfoSec Awards for 20
- Page 125 and 126: Cyber Defense InfoSec Awards for 20
- Page 127 and 128: Cyber Defense InfoSec Awards for 20
- Page 129 and 130: Cyber Defense InfoSec Awards for 20
- Page 131 and 132: Cyber Defense InfoSec Awards for 20
- Page 133 and 134: Cyber Defense InfoSec Awards for 20
- Page 135 and 136: Cyber Defense InfoSec Awards for 20
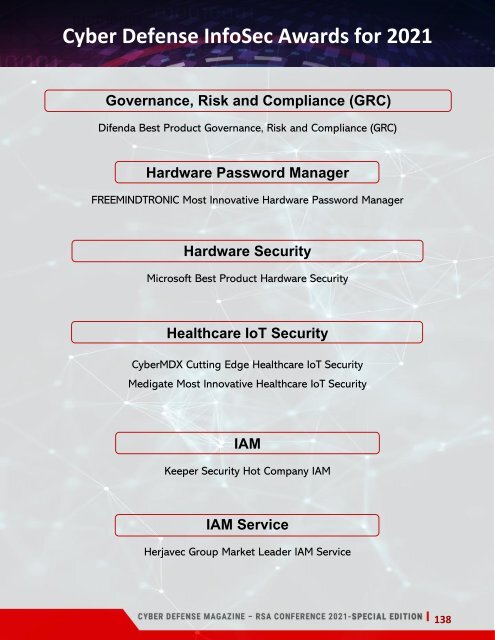
- Page 137: Cyber Defense InfoSec Awards for 20
- Page 141 and 142: Cyber Defense InfoSec Awards for 20
- Page 143 and 144: Cyber Defense InfoSec Awards for 20
- Page 145 and 146: Cyber Defense InfoSec Awards for 20
- Page 147 and 148: Cyber Defense InfoSec Awards for 20
- Page 149 and 150: Cyber Defense InfoSec Awards for 20
- Page 151 and 152: Cyber Defense InfoSec Awards for 20
- Page 153 and 154: Cyber Defense InfoSec Awards for 20
- Page 155 and 156: Cyber Defense InfoSec Awards for 20
- Page 157 and 158: Cyber Defense InfoSec Awards for 20
- Page 159 and 160: Cyber Defense InfoSec Awards for 20
- Page 161 and 162: Cyber Defense InfoSec Awards for 20
- Page 163 and 164: Cyber Defense InfoSec Awards for 20
- Page 165 and 166: 165
- Page 167 and 168: 167