Hashå½æ° - å京大å¦è®¡ç®æºç§å¦ææ¯ç 究æ
Hashå½æ° - å京大å¦è®¡ç®æºç§å¦ææ¯ç 究æ
Hashå½æ° - å京大å¦è®¡ç®æºç§å¦ææ¯ç 究æ
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
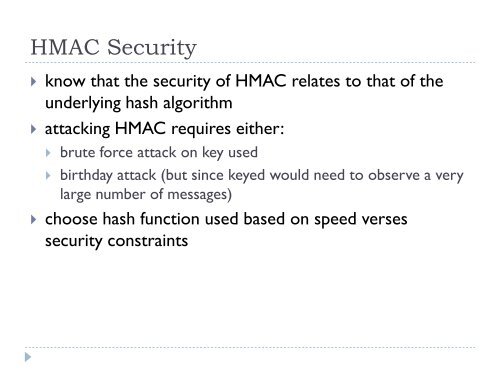
HMAC Security know that the security of HMAC relates to that of theunderlying hash algorithm attacking HMAC requires either: brute force attack on key used birthday attack (but since keyed would need to observe a verylarge number of messages) choose hash function used based on speed versessecurity constraints