Nessus Compliance Reference
Erfolgreiche ePaper selbst erstellen
Machen Sie aus Ihren PDF Publikationen ein blätterbares Flipbook mit unserer einzigartigen Google optimierten e-Paper Software.
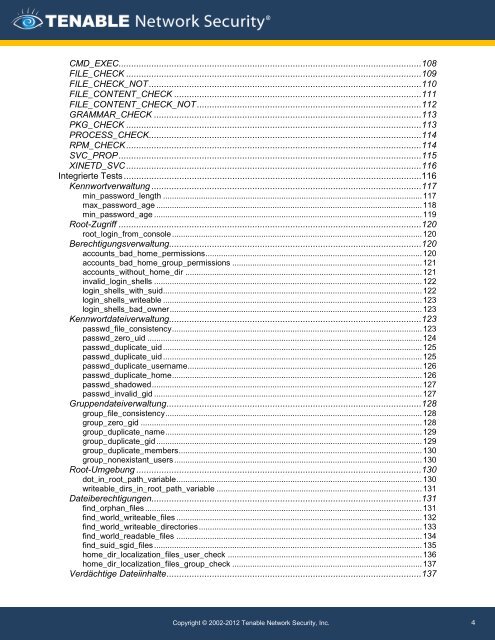
CMD_EXEC........................................................................................................................ 108<br />
FILE_CHECK ..................................................................................................................... 109<br />
FILE_CHECK_NOT ............................................................................................................ 110<br />
FILE_CONTENT_CHECK .................................................................................................. 111<br />
FILE_CONTENT_CHECK_NOT ......................................................................................... 112<br />
GRAMMAR_CHECK .......................................................................................................... 113<br />
PKG_CHECK ..................................................................................................................... 113<br />
PROCESS_CHECK ............................................................................................................ 114<br />
RPM_CHECK ..................................................................................................................... 114<br />
SVC_PROP ........................................................................................................................ 115<br />
XINETD_SVC ..................................................................................................................... 116<br />
Integrierte Tests ...................................................................................................................... 116<br />
Kennwortverwaltung ........................................................................................................... 117<br />
min_password_length .................................................................................................................... 117<br />
max_password_age ....................................................................................................................... 118<br />
min_password_age ........................................................................................................................ 119<br />
Root-Zugriff ........................................................................................................................ 120<br />
root_login_from_console ................................................................................................................ 120<br />
Berechtigungsverwaltung.................................................................................................... 120<br />
accounts_bad_home_permissions ................................................................................................. 120<br />
accounts_bad_home_group_permissions ..................................................................................... 121<br />
accounts_without_home_dir .......................................................................................................... 121<br />
invalid_login_shells ........................................................................................................................ 122<br />
login_shells_with_suid.................................................................................................................... 122<br />
login_shells_writeable .................................................................................................................... 123<br />
login_shells_bad_owner ................................................................................................................. 123<br />
Kennwortdateiverwaltung.................................................................................................... 123<br />
passwd_file_consistency ................................................................................................................ 123<br />
passwd_zero_uid ........................................................................................................................... 124<br />
passwd_duplicate_uid .................................................................................................................... 125<br />
passwd_duplicate_uid .................................................................................................................... 125<br />
passwd_duplicate_username ......................................................................................................... 126<br />
passwd_duplicate_home ................................................................................................................ 126<br />
passwd_shadowed ......................................................................................................................... 127<br />
passwd_invalid_gid ........................................................................................................................ 127<br />
Gruppendateiverwaltung ..................................................................................................... 128<br />
group_file_consistency ................................................................................................................... 128<br />
group_zero_gid .............................................................................................................................. 128<br />
group_duplicate_name ................................................................................................................... 129<br />
group_duplicate_gid ....................................................................................................................... 129<br />
group_duplicate_members ............................................................................................................. 130<br />
group_nonexistant_users ............................................................................................................... 130<br />
Root-Umgebung ................................................................................................................. 130<br />
dot_in_root_path_variable .............................................................................................................. 130<br />
writeable_dirs_in_root_path_variable ............................................................................................ 131<br />
Dateiberechtigungen ........................................................................................................... 131<br />
find_orphan_files ............................................................................................................................ 131<br />
find_world_writeable_files .............................................................................................................. 132<br />
find_world_writeable_directories .................................................................................................... 133<br />
find_world_readable_files .............................................................................................................. 134<br />
find_suid_sgid_files ........................................................................................................................ 135<br />
home_dir_localization_files_user_check ....................................................................................... 136<br />
home_dir_localization_files_group_check ..................................................................................... 137<br />
Verdächtige Dateiinhalte ..................................................................................................... 137<br />
Copyright © 2002-2012 Tenable Network Security, Inc.<br />
4