Nessus Compliance Reference
Erfolgreiche ePaper selbst erstellen
Machen Sie aus Ihren PDF Publikationen ein blätterbares Flipbook mit unserer einzigartigen Google optimierten e-Paper Software.
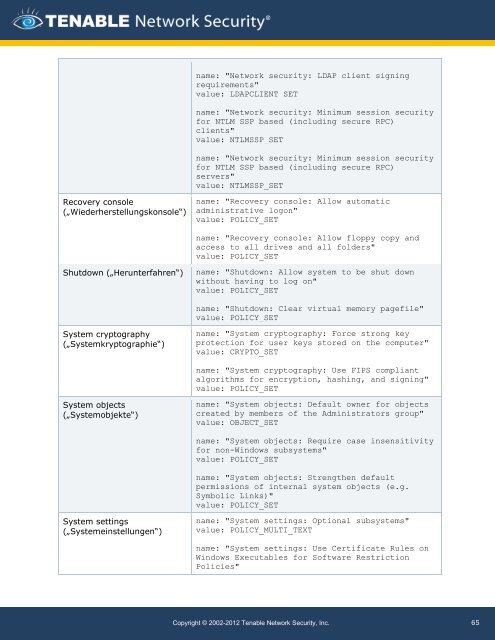
Recovery console<br />
(„Wiederherstellungskonsole“)<br />
Shutdown („Herunterfahren“)<br />
System cryptography<br />
(„Systemkryptographie“)<br />
System objects<br />
(„Systemobjekte“)<br />
System settings<br />
(„Systemeinstellungen“)<br />
name: "Network security: LDAP client signing<br />
requirements"<br />
value: LDAPCLIENT_SET<br />
name: "Network security: Minimum session security<br />
for NTLM SSP based (including secure RPC)<br />
clients"<br />
value: NTLMSSP_SET<br />
name: "Network security: Minimum session security<br />
for NTLM SSP based (including secure RPC)<br />
servers"<br />
value: NTLMSSP_SET<br />
name: "Recovery console: Allow automatic<br />
administrative logon"<br />
value: POLICY_SET<br />
name: "Recovery console: Allow floppy copy and<br />
access to all drives and all folders"<br />
value: POLICY_SET<br />
name: "Shutdown: Allow system to be shut down<br />
without having to log on"<br />
value: POLICY_SET<br />
name: "Shutdown: Clear virtual memory pagefile"<br />
value: POLICY_SET<br />
name: "System cryptography: Force strong key<br />
protection for user keys stored on the computer"<br />
value: CRYPTO_SET<br />
name: "System cryptography: Use FIPS compliant<br />
algorithms for encryption, hashing, and signing"<br />
value: POLICY_SET<br />
name: "System objects: Default owner for objects<br />
created by members of the Administrators group"<br />
value: OBJECT_SET<br />
name: "System objects: Require case insensitivity<br />
for non-Windows subsystems"<br />
value: POLICY_SET<br />
name: "System objects: Strengthen default<br />
permissions of internal system objects (e.g.<br />
Symbolic Links)"<br />
value: POLICY_SET<br />
name: "System settings: Optional subsystems"<br />
value: POLICY_MULTI_TEXT<br />
name: "System settings: Use Certificate Rules on<br />
Windows Executables for Software Restriction<br />
Policies"<br />
Copyright © 2002-2012 Tenable Network Security, Inc.<br />
65