Catalog of Control Systems Security: Recommendations for Standards Developers
Catalog of Control Systems Security: Recommendations for Standards Developers
Catalog of Control Systems Security: Recommendations for Standards Developers
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
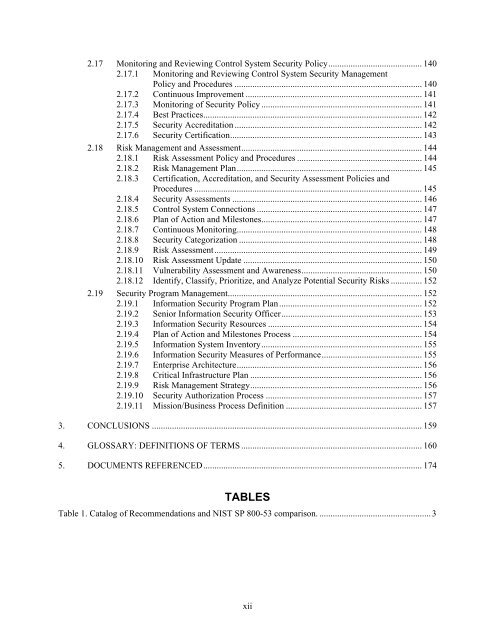
2.17 Monitoring and Reviewing <strong>Control</strong> System <strong>Security</strong> Policy .......................................... 140<br />
2.17.1 Monitoring and Reviewing <strong>Control</strong> System <strong>Security</strong> Management<br />
Policy and Procedures .................................................................................... 140<br />
2.17.2 Continuous Improvement ............................................................................... 141<br />
2.17.3 Monitoring <strong>of</strong> <strong>Security</strong> Policy ........................................................................ 141<br />
2.17.4 Best Practices .................................................................................................. 142<br />
2.17.5 <strong>Security</strong> Accreditation .................................................................................... 142<br />
2.17.6 <strong>Security</strong> Certification ...................................................................................... 143<br />
2.18 Risk Management and Assessment ................................................................................. 144<br />
2.18.1 Risk Assessment Policy and Procedures ........................................................ 144<br />
2.18.2 Risk Management Plan ................................................................................... 145<br />
2.18.3 Certification, Accreditation, and <strong>Security</strong> Assessment Policies and<br />
Procedures ...................................................................................................... 145<br />
2.18.4 <strong>Security</strong> Assessments ..................................................................................... 146<br />
2.18.5 <strong>Control</strong> System Connections .......................................................................... 147<br />
2.18.6 Plan <strong>of</strong> Action and Milestones ........................................................................ 147<br />
2.18.7 Continuous Monitoring................................................................................... 148<br />
2.18.8 <strong>Security</strong> Categorization .................................................................................. 148<br />
2.18.9 Risk Assessment ............................................................................................. 149<br />
2.18.10 Risk Assessment Update ................................................................................ 150<br />
2.18.11 Vulnerability Assessment and Awareness ...................................................... 150<br />
2.18.12 Identify, Classify, Prioritize, and Analyze Potential <strong>Security</strong> Risks .............. 152<br />
2.19 <strong>Security</strong> Program Management ....................................................................................... 152<br />
2.19.1 In<strong>for</strong>mation <strong>Security</strong> Program Plan ................................................................ 152<br />
2.19.2 Senior In<strong>for</strong>mation <strong>Security</strong> Officer ............................................................... 153<br />
2.19.3 In<strong>for</strong>mation <strong>Security</strong> Resources ..................................................................... 154<br />
2.19.4 Plan <strong>of</strong> Action and Milestones Process .......................................................... 154<br />
2.19.5 In<strong>for</strong>mation System Inventory ........................................................................ 155<br />
2.19.6 In<strong>for</strong>mation <strong>Security</strong> Measures <strong>of</strong> Per<strong>for</strong>mance ............................................. 155<br />
2.19.7 Enterprise Architecture ................................................................................... 156<br />
2.19.8 Critical Infrastructure Plan ............................................................................. 156<br />
2.19.9 Risk Management Strategy ............................................................................. 156<br />
2.19.10 <strong>Security</strong> Authorization Process ...................................................................... 157<br />
2.19.11 Mission/Business Process Definition ............................................................. 157<br />
3. CONCLUSIONS ......................................................................................................................... 159<br />
4. GLOSSARY: DEFINITIONS OF TERMS ................................................................................. 160<br />
5. DOCUMENTS REFERENCED .................................................................................................. 174<br />
TABLES<br />
Table 1. <strong>Catalog</strong> <strong>of</strong> <strong>Recommendations</strong> and NIST SP 800-53 comparison. .................................................. 3<br />
xii